Data Remediation Best Practices Guide

Data Remediation Best Practices Guide Learn data remediation best practices to reduce risk faster, prioritize exposures, and turn data security insights into action. If you perform the remediation process correctly, you can reduce the chance of data theft, malware, and other cyber attacks. below are the key steps to effectively remediate the vulnerabilities from your system.
Data Remediation Best Practices Guide Follow these 10 vulnerability remediation best practices to fix flaws faster, reduce risk, and stay ahead of attackers in 2026. Learn top vulnerability management, scanning, and remediation best practices to protect your systems and reduce security risks effectively. read today!. Through years of remediating vulnerabilities across diverse environments, i’ve developed best practices that consistently improve outcomes while reducing stress on security and operations teams. This article outlines key best practices that help organizations remediate vulnerabilities efficiently. the practices depend upon asset visibility, discovery processes, and operational planning.
Data Remediation Best Practices Guide Through years of remediating vulnerabilities across diverse environments, i’ve developed best practices that consistently improve outcomes while reducing stress on security and operations teams. This article outlines key best practices that help organizations remediate vulnerabilities efficiently. the practices depend upon asset visibility, discovery processes, and operational planning. After you establish the correct controls and data security posture for your data, monitor for any changes that can put your data at risk. see the recommendations in scenario 1. Vulnerability remediation best practices building on the process framework above, here are the practices that separate high performing remediation programs from those constantly fighting their backlog:. Ensure data quality and reliability in modern pipelines with effective data remediation. learn the key steps you should follow in the data remediation process. Explore what data remediation is, why it's critical for compliance, and key strategies to fix and manage data issues.

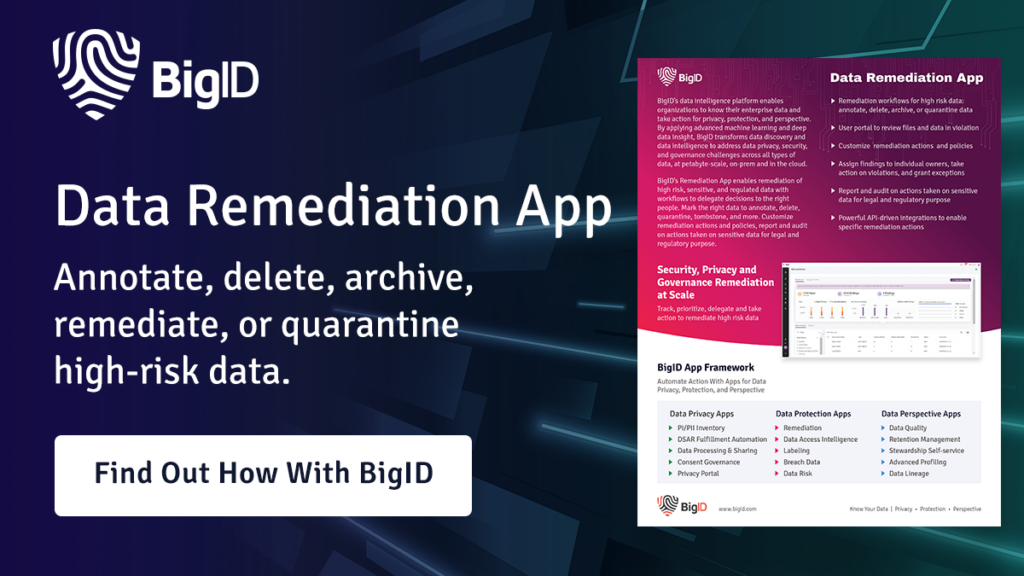
Streamlining Data Remediation Best Practices Guide Bigid After you establish the correct controls and data security posture for your data, monitor for any changes that can put your data at risk. see the recommendations in scenario 1. Vulnerability remediation best practices building on the process framework above, here are the practices that separate high performing remediation programs from those constantly fighting their backlog:. Ensure data quality and reliability in modern pipelines with effective data remediation. learn the key steps you should follow in the data remediation process. Explore what data remediation is, why it's critical for compliance, and key strategies to fix and manage data issues.
A Guide To Secret Remediation Best Practices Ensure data quality and reliability in modern pipelines with effective data remediation. learn the key steps you should follow in the data remediation process. Explore what data remediation is, why it's critical for compliance, and key strategies to fix and manage data issues.

Streamlining Data Remediation Best Practices Guide Bigid
Comments are closed.