Data Exfiltration Techniques Ssh Tryhackme Data Exfiltration
What Is Data Exfiltration At first i thought something didn't work but later found out the the ssh session was backgrounded with the f argument. now we can use two methods to connect to the local machine. An introduction to data exfiltration and tunneling techniques over various protocols. ready to learn cyber security? the data exfiltration room is only available for premium users. signup now to access more than 500 free rooms and learn cyber security through a fun, interactive learning environment. already have an account? log in.

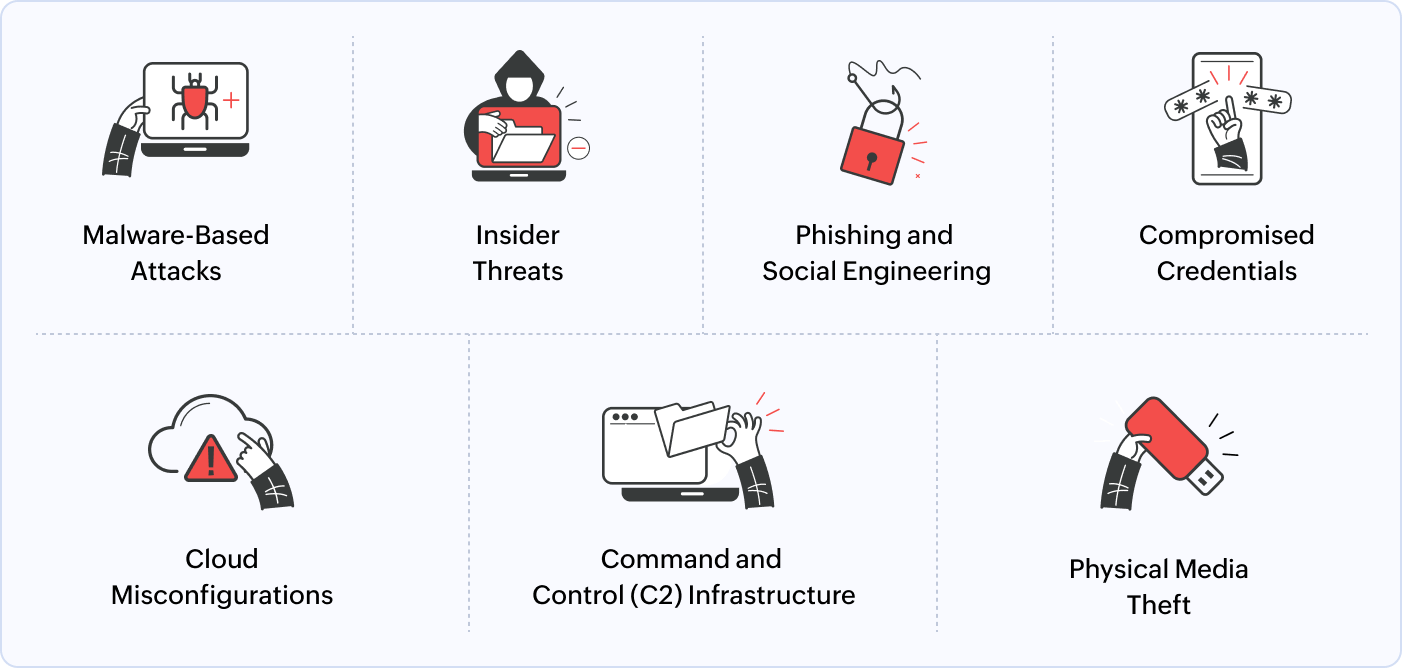
What Happens When Hackers Exfiltrate Data From Your Business Blackfog This writeup walks through the tryhackme data exfiltration room, where i analyzed packet captures and splunk logs to detect four distinct exfiltration channels. What’s the flag hidden inside the exfiltrated data? i tried to filter with the ip from the previous question, but the command didn’t work, so got help from the description explained and. Data exfiltration is a high impact threat activity defined by the unauthorized transfer of sensitive assets from an organization’s network. this process involves a combination of legitimate tools, opportunistic methods, and covert channels. Answers for the tryhackme data exfiltration room the tryhackme data exfiltration room shows how hackers can move data out of a network and ways to detect this movement of data.
Tryhackme Data Exfiltration Data exfiltration is a high impact threat activity defined by the unauthorized transfer of sensitive assets from an organization’s network. this process involves a combination of legitimate tools, opportunistic methods, and covert channels. Answers for the tryhackme data exfiltration room the tryhackme data exfiltration room shows how hackers can move data out of a network and ways to detect this movement of data. A curated list of hands on exercises (tryhackme htb home labs) that matter for the job, with instructions on how to document them for your portfolio. Complete walkthrough of tryhackme's data exfiltration detection room. learn ftp traffic analysis, wireshark forensics, and advanced cybersecurity techniques to detect data breaches. Today, we’re diving into the “data exfiltration” room on tryhackme. we’ll put on our soc analyst hats and use splunk and wireshark to hunt for attackers trying to smuggle data out using four different methods: dns, ftp, http, and icmp. let’s learn how to follow the data trail!. Learn how to detect data exfiltration attempts in various network channels.
Tryhackme Cyber Security Training A curated list of hands on exercises (tryhackme htb home labs) that matter for the job, with instructions on how to document them for your portfolio. Complete walkthrough of tryhackme's data exfiltration detection room. learn ftp traffic analysis, wireshark forensics, and advanced cybersecurity techniques to detect data breaches. Today, we’re diving into the “data exfiltration” room on tryhackme. we’ll put on our soc analyst hats and use splunk and wireshark to hunt for attackers trying to smuggle data out using four different methods: dns, ftp, http, and icmp. let’s learn how to follow the data trail!. Learn how to detect data exfiltration attempts in various network channels.

Data Exfiltration Detection Tryhackme Walkthrough The Masterminds Today, we’re diving into the “data exfiltration” room on tryhackme. we’ll put on our soc analyst hats and use splunk and wireshark to hunt for attackers trying to smuggle data out using four different methods: dns, ftp, http, and icmp. let’s learn how to follow the data trail!. Learn how to detect data exfiltration attempts in various network channels.
Comments are closed.