Cybersecurity In 60 Second Septa Cyber Attack Case Study

Case Study Ics Cyber Attack 1699334568 Pdf Security Computer Security In this in depth article by digitaldefynd, we explore 10 of the most significant and recent cybersecurity case studies from across the globe, each revealing critical insights into evolving threats, response mechanisms, and long term implications. Discussion on the aftermath of the septa cyber attack. still not up.

Case Study Of Cosmos Bank Cyber Attack Pdf Ransomware Cybercrime The center for strategic and international studies estimates that the cost of cybercrime to the global economy is more than $600 billion annually. in this lab, you will study four high profile cyberattacks and be prepared to discuss the who, what, why and how of each attack. This blog explores the top 10 real world case studies on cybersecurity incidents to give a broad understanding of how the threat landscape is evolving and what threats could reach you or your business organization in today's digitally advanced ecosystem. Cybersecurity breaches and attacks have become an all too common occurrence in today’s interconnected world. from high profile data breaches affecting millions of users to ransomware attacks crippling entire industries, the implications of cyber incidents are far reaching. Explore top cybersecurity case studies, including global data breaches and ransomware attacks. learn the causes, impacts, and security strategies that can protect organizations from cyber threats.

Case Study A Major Cyber Attack And Its Aftermath Cybersecurity breaches and attacks have become an all too common occurrence in today’s interconnected world. from high profile data breaches affecting millions of users to ransomware attacks crippling entire industries, the implications of cyber incidents are far reaching. Explore top cybersecurity case studies, including global data breaches and ransomware attacks. learn the causes, impacts, and security strategies that can protect organizations from cyber threats. This timeline records significant cyber incidents since 2006. we focus on cyber attacks on government agencies, defense and high tech companies, or economic crimes with losses of more than a million dollars. if you think we’ve missed something, please send an email to [email protected]. Explore real world cybersecurity case studies from asia. see how blackpanda’s elite responders contained ransomware, breaches, data leaks, and more — protecting organizations from major losses. This document is a comprehensive study of major cybersecurity incidents from 1988 to 2025, detailing significant events and their impacts on organizations, governments, and individuals. Our high quality cyber security case studies are produced by a team of experienced risk managers focused on providing a balanced perspective of cyber security failures to help organisations navigate the cyber security labyrinth.

Wazirx Cyber Attack Case Study 2024 Pdf Computer Security Security This timeline records significant cyber incidents since 2006. we focus on cyber attacks on government agencies, defense and high tech companies, or economic crimes with losses of more than a million dollars. if you think we’ve missed something, please send an email to [email protected]. Explore real world cybersecurity case studies from asia. see how blackpanda’s elite responders contained ransomware, breaches, data leaks, and more — protecting organizations from major losses. This document is a comprehensive study of major cybersecurity incidents from 1988 to 2025, detailing significant events and their impacts on organizations, governments, and individuals. Our high quality cyber security case studies are produced by a team of experienced risk managers focused on providing a balanced perspective of cyber security failures to help organisations navigate the cyber security labyrinth.
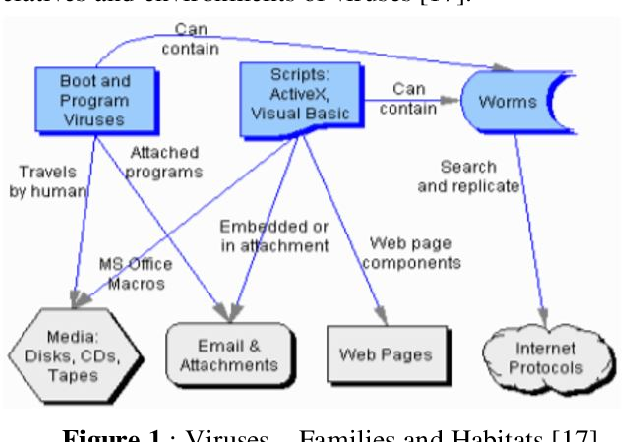
Figure 1 From Cyber Attacks And Impacts A Case Study In Saudi Arabia This document is a comprehensive study of major cybersecurity incidents from 1988 to 2025, detailing significant events and their impacts on organizations, governments, and individuals. Our high quality cyber security case studies are produced by a team of experienced risk managers focused on providing a balanced perspective of cyber security failures to help organisations navigate the cyber security labyrinth.
Comments are closed.