Cyber Threat Intelligence Cti Analysis Reporting

Cyber Threat Intelligence Cti Echo Discover how cyber threat intelligence (cti) is collected, analyzed, and operationalized to power proactive, intelligence led defense. Ctid’s cti blueprints, specifically the word templates and pdf samples for cti reports is a resource worth looking into for anyone new or proficient in the cti space and especially important for those wanting to ensure their reports convey actionable outcomes.
Cyber Threat Intelligence Collection And Analysis Cti report writing is an essential threat intelligence skill. this guide will teach how to write a threat intelligence report with cti report examples. As an example, a recent microsoft report on zinc serves as a model of a well structured cti report. it not only includes a range of technical indicators but also provides extensive context for these indicators. Tailored threat intelligence reports that inform strategic, operational, and tactical security decisions. get actionable cyber threat intelligence reporting for your organisation with secalliance. Tips and frameworks for writing and briefing actionable cyber threat intelligence reports.

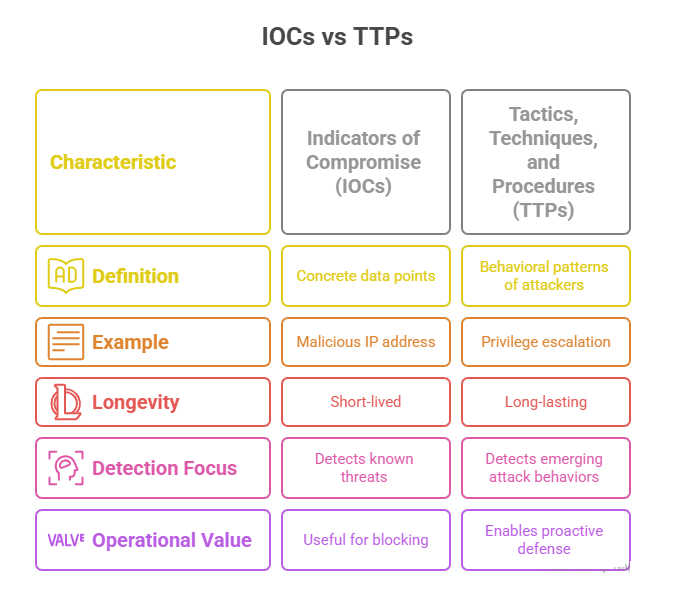
Cyber Threat Intelligence Collection And Analysis Tailored threat intelligence reports that inform strategic, operational, and tactical security decisions. get actionable cyber threat intelligence reporting for your organisation with secalliance. Tips and frameworks for writing and briefing actionable cyber threat intelligence reports. In recent years, cyber threat intelligence (cti) has become an integral part of many cybersecurity strategies. this guide will walk you through key definitions and concepts related to cti, the essential levels and lifecycle of a cti program, and its role in the context of new regulatory requirements. This project seeks to increase the operational relevance of reports through a standardized set of templates that help analysts answer specific analytic questions for common cyber security use cases. Cyberthreat intelligence is the process of collecting raw data and analysing it to enhance an organization‘s security posture. from the data collected, security professionals can create intelligence reports designed to overcome current and future threats within the threat landscape. Cyber threat intelligence (cti) represents evidence based knowledge (e.g., context, mechanisms, indicators, implications, and action oriented advice) about existing or emerging cyber threats.
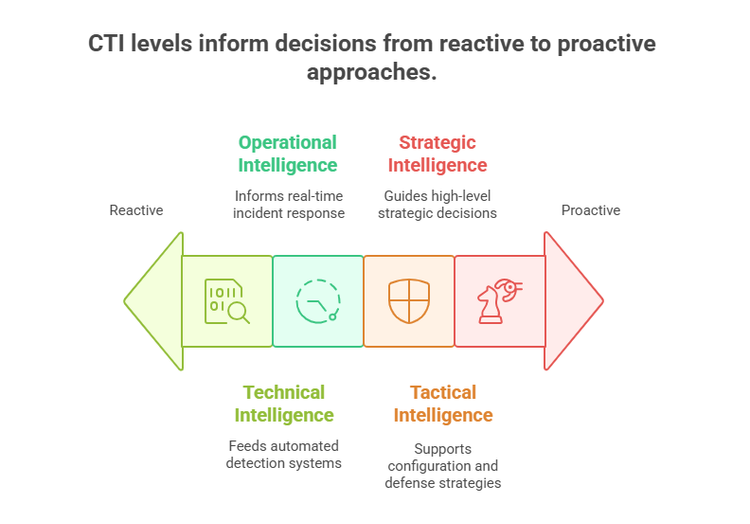
Cyber Threat Intelligence Collection And Analysis In recent years, cyber threat intelligence (cti) has become an integral part of many cybersecurity strategies. this guide will walk you through key definitions and concepts related to cti, the essential levels and lifecycle of a cti program, and its role in the context of new regulatory requirements. This project seeks to increase the operational relevance of reports through a standardized set of templates that help analysts answer specific analytic questions for common cyber security use cases. Cyberthreat intelligence is the process of collecting raw data and analysing it to enhance an organization‘s security posture. from the data collected, security professionals can create intelligence reports designed to overcome current and future threats within the threat landscape. Cyber threat intelligence (cti) represents evidence based knowledge (e.g., context, mechanisms, indicators, implications, and action oriented advice) about existing or emerging cyber threats.
Comments are closed.