Cyber Security Needs Assessment It360
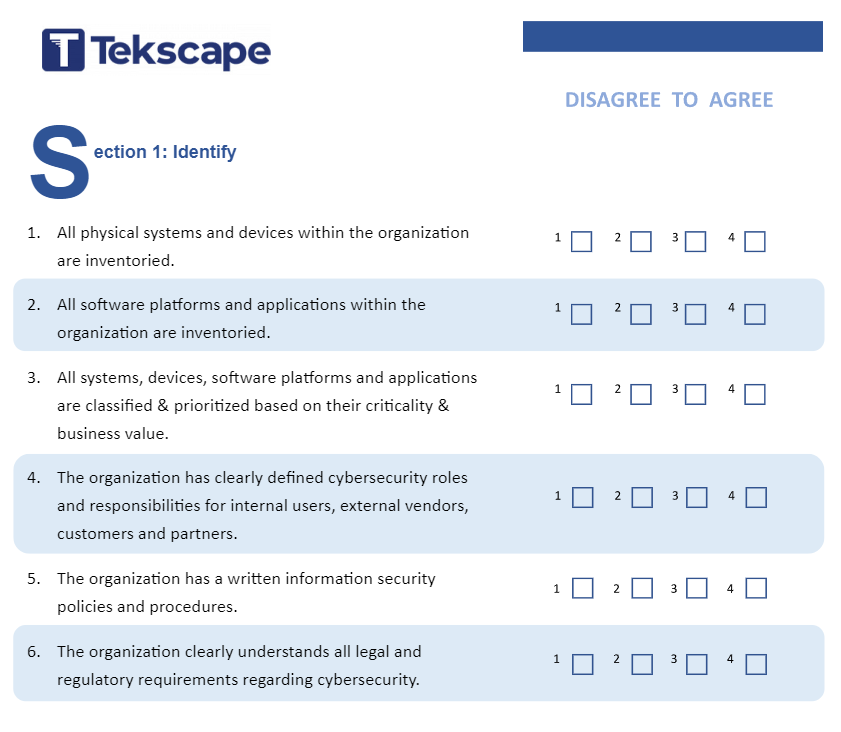
Cybersecurity Assessment Tekscape Understand your organisations current security posture and uncover your weak spots. our comprehensive cyber security needs assessment examines seven key areas to determine your current, as is state and how far along are you with a future, protected state. What is a cyber security assessment? a cyber security assessment is a process of evaluating security controls to examine the overall company’s security infrastructure. this includes validating the company’s preparedness against the known and unknown vulnerabilities.

Cyber Security Assessment Mki It Solutions Asia Pacific Pte Ltd An it security assessment is a process used to assess the security of your systems, networks, and data against cyber threats. it finds weak points like outdated software, weak passwords, or poor settings that attackers can use. this assessment reviews your entire it environment and measures how well your current security controls are working. A cybersecurity risk assessment is a systematic process for identifying, evaluating and prioritizing potential threats and vulnerabilities within an organization’s information technology (it) environment. This short quiz will provide a high level security risk assessment, identifying threats facing your information systems, networks and data, and assessing the potential consequences you’d face should adverse events occur. Understand your organisations current security posture and uncover your weak spots. our comprehensive cyber security needs assessment examines seven key areas to determine your current, as is state and how far along are you with a future, protected state.

Cybersecurity Assessment Ati Application Development System This short quiz will provide a high level security risk assessment, identifying threats facing your information systems, networks and data, and assessing the potential consequences you’d face should adverse events occur. Understand your organisations current security posture and uncover your weak spots. our comprehensive cyber security needs assessment examines seven key areas to determine your current, as is state and how far along are you with a future, protected state. Cyber security assessments and compliance audits for law firms, small to medium sized businesses and more. connect with us today. This guide provides a step by step approach to conducting a thorough cybersecurity assessment, enabling your organization to address risks and comply with regulations effectively. It measures the effectiveness and maturity of existing security controls, processes, and strategies against industry best practices and frameworks. the assessment helps identify gaps, prioritize improvements, and align security measures with business objectives and risk tolerance. Explore 10 best practices for cybersecurity assessment covering risk, compliance, vulnerability testing, and it security audit essentials.

Cyber Security Assessment By It360 Cyber security assessments and compliance audits for law firms, small to medium sized businesses and more. connect with us today. This guide provides a step by step approach to conducting a thorough cybersecurity assessment, enabling your organization to address risks and comply with regulations effectively. It measures the effectiveness and maturity of existing security controls, processes, and strategies against industry best practices and frameworks. the assessment helps identify gaps, prioritize improvements, and align security measures with business objectives and risk tolerance. Explore 10 best practices for cybersecurity assessment covering risk, compliance, vulnerability testing, and it security audit essentials.

Cyber Security Assessment By It360 It measures the effectiveness and maturity of existing security controls, processes, and strategies against industry best practices and frameworks. the assessment helps identify gaps, prioritize improvements, and align security measures with business objectives and risk tolerance. Explore 10 best practices for cybersecurity assessment covering risk, compliance, vulnerability testing, and it security audit essentials.

Cyber Security Assessment By It360
Comments are closed.