Cyber Kill Chain Le Duy Duc
Cyber Kill Chain Le Duy Duc The cyber kill chain framework came from lockheed martin to describe the stages that a cyber attack would normally flow through. understanding this chain will help organizations and employees prepare ourselves across the trust gaps to proactive defense, improve incident response and conduct comprehensive risk assessments: ⚔ 1. Cyber kill chain the cyber kill chain framework came from lockheed martin to describe the stages that a cyber attack would normally flow through.

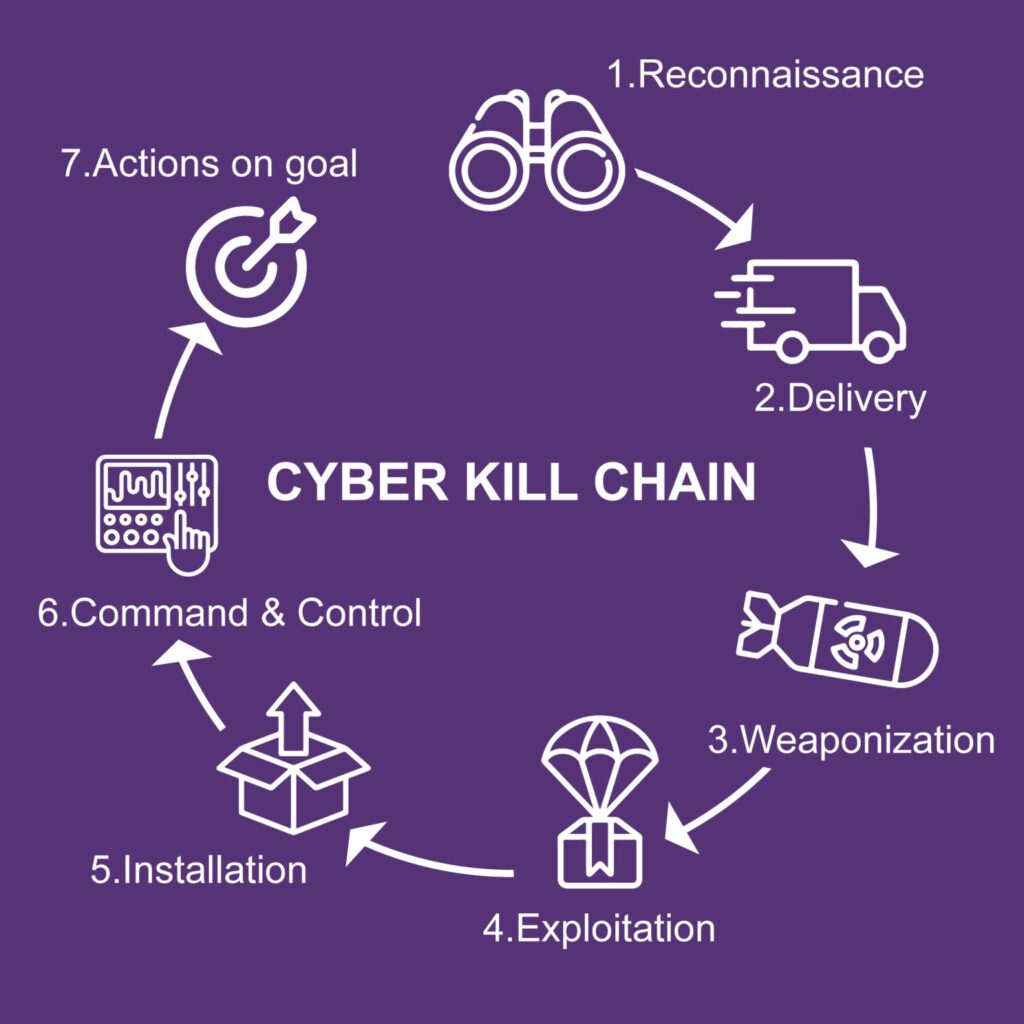
Cyber Kill Chain Developed by lockheed martin, the cyber kill chain® framework is part of the intelligence driven defense® model for identification and prevention of cyber intrusions activity. the model identifies what the adversaries must complete in order to achieve their objective. Grizzly steppe – russian malicious cyber activity. retrieved january 11, 2017. alperovitch, d (2016, june 15). bears in the midst: intrusion into the democratic national committee. retrieved august 3, 2016. uk gov. (2021, april 15). uk exposes russian involvement in solarwinds cyber compromise . retrieved april 16, 2021. A cyber kill chain reveals the phases of a cyberattack: from early reconnaissance to the goal of data exfiltration. [citation needed] the kill chain can also be used as a management tool to help continuously improve network defense. The kill chain model is designed in seven steps: defender’s goal: understand the aggressor’s actions understanding is intelligence intruder succeeds if, and only if, they can proceed through steps 1 6 and reach the final stage of the cyber kill chain®.
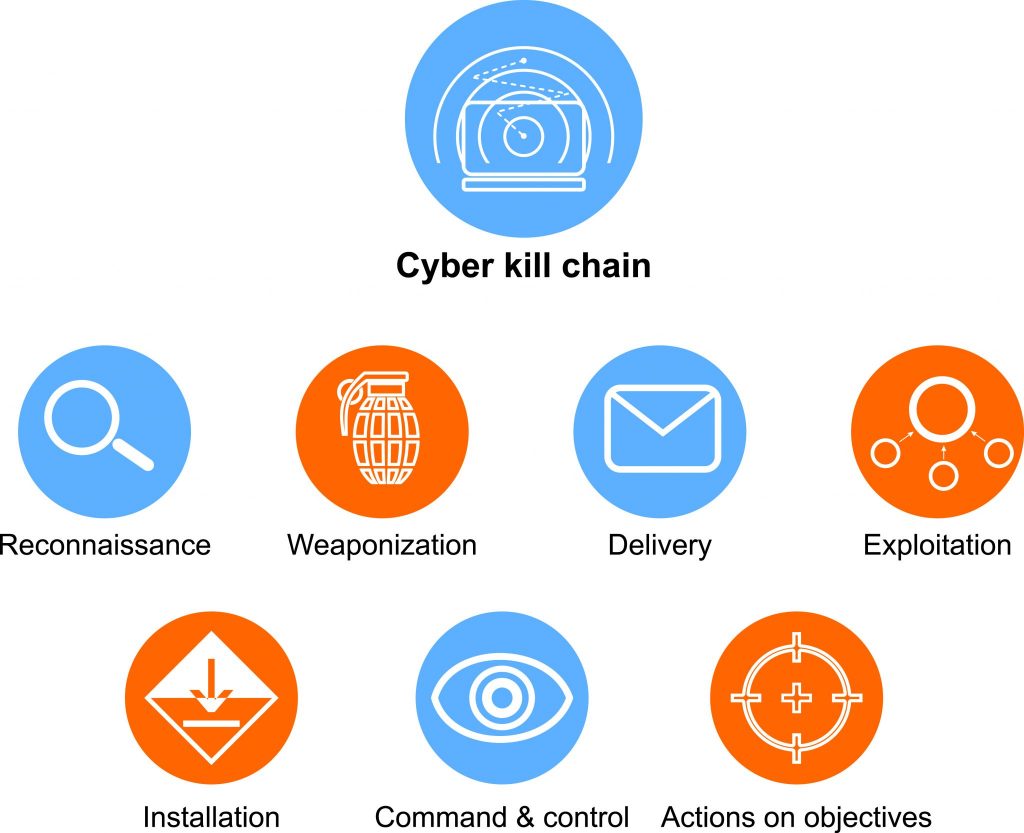
Cyber Kill Chain How Understanding What It Is Can Help You Stop A cyber kill chain reveals the phases of a cyberattack: from early reconnaissance to the goal of data exfiltration. [citation needed] the kill chain can also be used as a management tool to help continuously improve network defense. The kill chain model is designed in seven steps: defender’s goal: understand the aggressor’s actions understanding is intelligence intruder succeeds if, and only if, they can proceed through steps 1 6 and reach the final stage of the cyber kill chain®. This study focuses on analyzing the detection and defense of cyber attacks on companies, emphasizing the cyber kill chain (ckc) model. examining specialized articles reveals the widespread recognition and application of this structured methodology in cybersecurity. Cyber kill chain: lockheed martin's seven phase model mapping intrusion lifecycles from reconnaissance through weaponization, delivery, exploitation, installation, command and control, to. Driven defense® approach to computer network defense. section four outlines the seven ways an organization can apply the cyber . ill chain® framework in their environment using a tip. section five introduces the palisadetm solution, lockheed martin’s threat inte. li. ence platfor. In this article, i critically examine the ‘cyber kill chain’, a methodological framework for thought and action that shapes both contemporary cybersecurity practice and the discursive.

Cyber Kill Chain What Is It Examples And Prevention Storware This study focuses on analyzing the detection and defense of cyber attacks on companies, emphasizing the cyber kill chain (ckc) model. examining specialized articles reveals the widespread recognition and application of this structured methodology in cybersecurity. Cyber kill chain: lockheed martin's seven phase model mapping intrusion lifecycles from reconnaissance through weaponization, delivery, exploitation, installation, command and control, to. Driven defense® approach to computer network defense. section four outlines the seven ways an organization can apply the cyber . ill chain® framework in their environment using a tip. section five introduces the palisadetm solution, lockheed martin’s threat inte. li. ence platfor. In this article, i critically examine the ‘cyber kill chain’, a methodological framework for thought and action that shapes both contemporary cybersecurity practice and the discursive.

Cyberattack Decoding Kill Chain Unlocking Cyber Kill Chain To Track Driven defense® approach to computer network defense. section four outlines the seven ways an organization can apply the cyber . ill chain® framework in their environment using a tip. section five introduces the palisadetm solution, lockheed martin’s threat inte. li. ence platfor. In this article, i critically examine the ‘cyber kill chain’, a methodological framework for thought and action that shapes both contemporary cybersecurity practice and the discursive.
Comments are closed.