Cyber Kill Chain Defend Detect
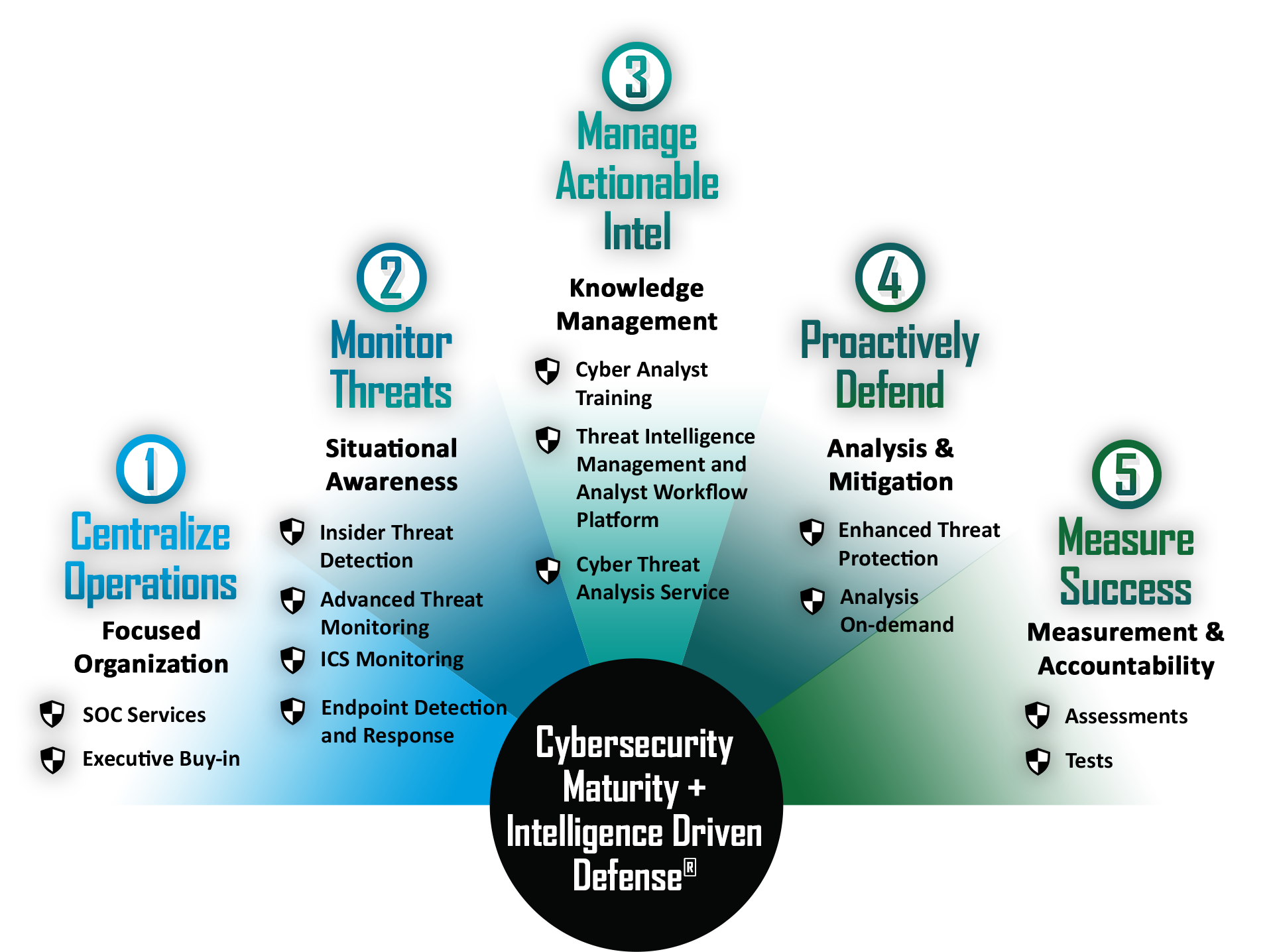
Cyber Kill Chain Detectx Cloud Security Expert Developed by lockheed martin, the cyber kill chain® framework is part of the intelligence driven defense® model for identification and prevention of cyber intrusions activity. the model identifies what the adversaries must complete in order to achieve their objective. Master the cyber kill chain process with ec council’s expert guide to the seven critical steps involved in a cyberattacks. learn how to detect & stop cyberattacks at every stage.

Cyber Kill Chain Defend Detect Originally developed by lockheed martin in 2011, the cyber kill chain outlines the various stages of several common cyberattacks and, by extension, the points at which the information security team can prevent, detect or intercept attackers. The cyber kill chain plays an important role in helping organizations strengthen their defenses against cyber threats. by breaking down an attack into distinct stages, it enables businesses to identify and mitigate attacks at every step before they can cause significant damage. The cyber kill chain operates on a straightforward principle: attackers must complete each stage in sequence to reach their objective. this linear progression creates natural chokepoints where defenders can detect, deny, disrupt, or contain adversary operations before damage occurs. Learn what the cyber kill chain is, how each stage works—from reconnaissance to data thief, and how to detect and stop attacks at every phase. includes real world examples.

Cyber Kill Chain The cyber kill chain operates on a straightforward principle: attackers must complete each stage in sequence to reach their objective. this linear progression creates natural chokepoints where defenders can detect, deny, disrupt, or contain adversary operations before damage occurs. Learn what the cyber kill chain is, how each stage works—from reconnaissance to data thief, and how to detect and stop attacks at every phase. includes real world examples. C2 channels are stealthier, more resilient, and harder to detect than ever. they use legitimate protocols, cloud services, and end to end encryption to evade traffic inspection. Explore the 2025 guide to the cyber kill chain. learn each phase, real world examples, and how to strengthen your defense strategy. Learn how the cyber kill chain helps you map controls, detect threats, and disrupt attacks across cloud and on prem environments. Cyber kill chains are used to build solid foundations and develop proactive defense strategies. they work great for organizations that use a mix of intrusion detection systems, firewalls, and modern security solutions.
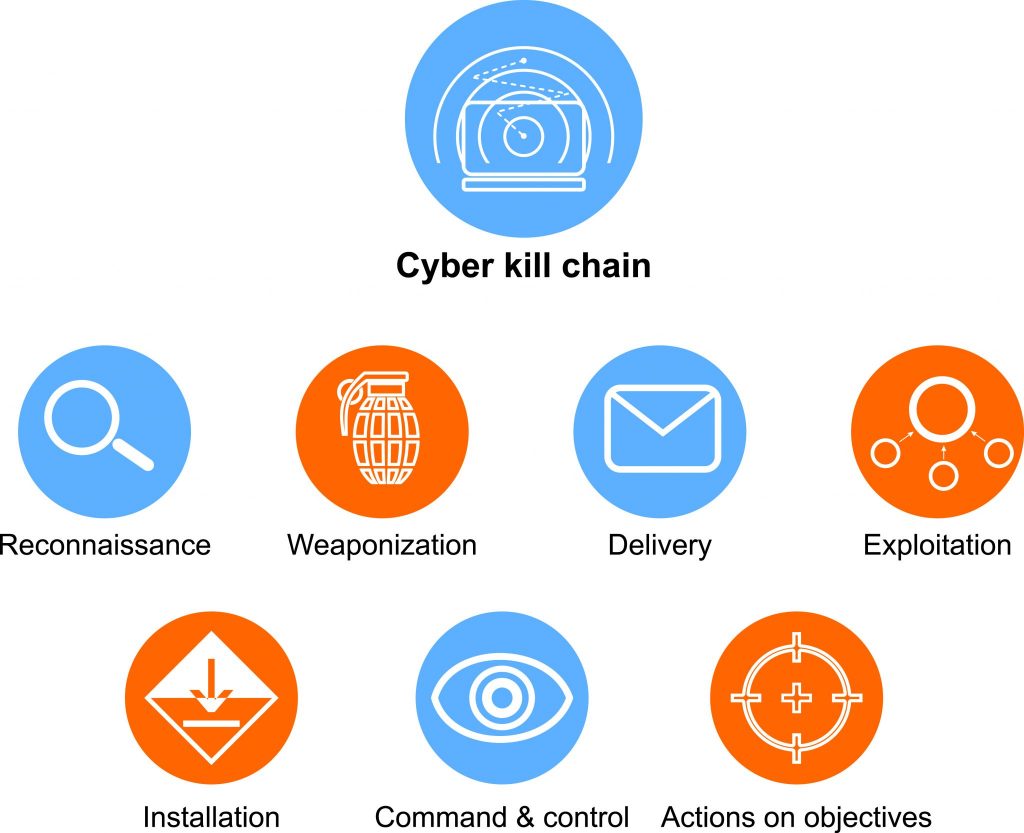
Cyber Kill Chain How Understanding What It Is Can Help You Stop C2 channels are stealthier, more resilient, and harder to detect than ever. they use legitimate protocols, cloud services, and end to end encryption to evade traffic inspection. Explore the 2025 guide to the cyber kill chain. learn each phase, real world examples, and how to strengthen your defense strategy. Learn how the cyber kill chain helps you map controls, detect threats, and disrupt attacks across cloud and on prem environments. Cyber kill chains are used to build solid foundations and develop proactive defense strategies. they work great for organizations that use a mix of intrusion detection systems, firewalls, and modern security solutions.
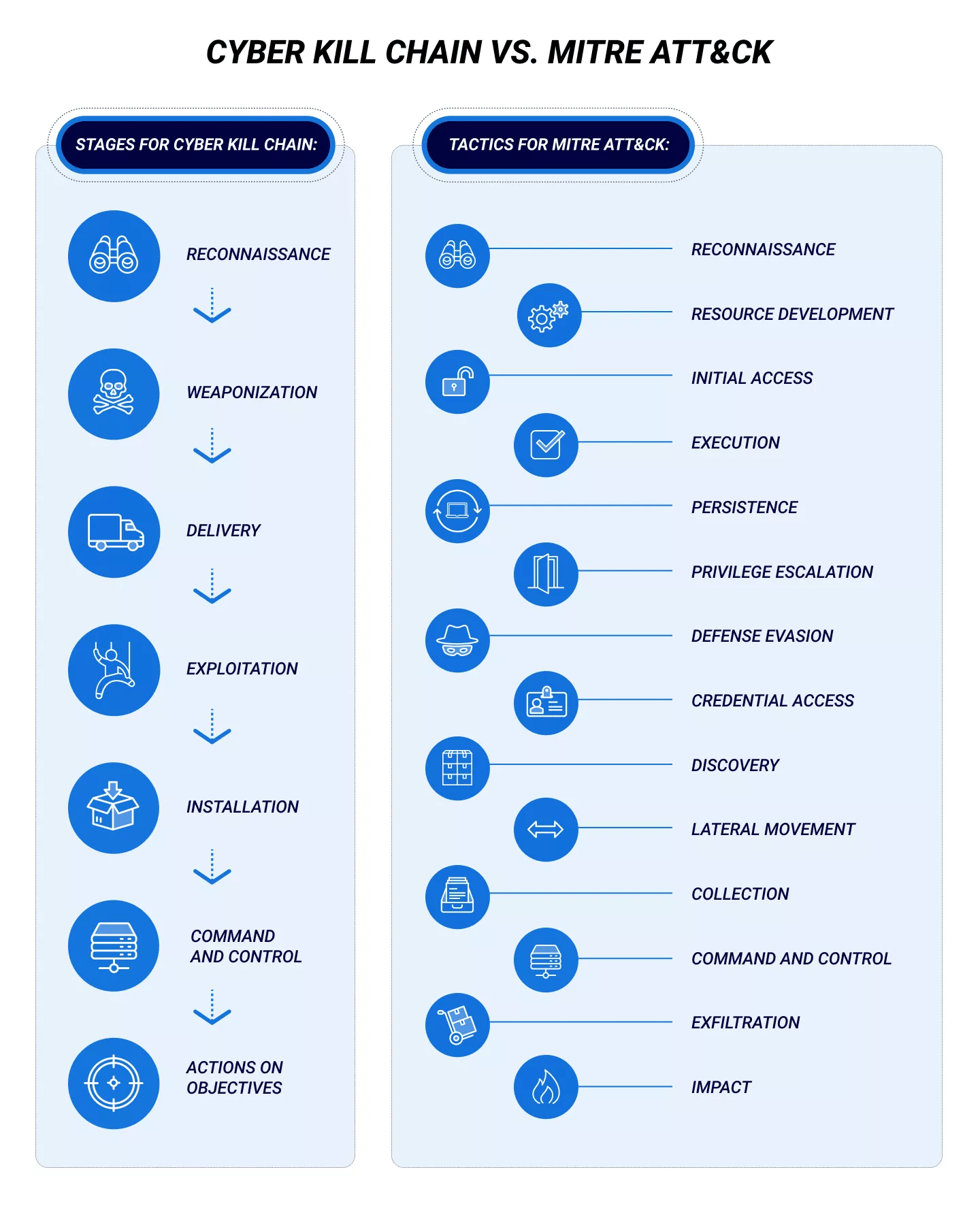
Cyber Attack Kill Chain Cyber Kill Chain Definition Fpyk Learn how the cyber kill chain helps you map controls, detect threats, and disrupt attacks across cloud and on prem environments. Cyber kill chains are used to build solid foundations and develop proactive defense strategies. they work great for organizations that use a mix of intrusion detection systems, firewalls, and modern security solutions.

Cyberattack Decoding Kill Chain Unlocking Cyber Kill Chain To Track
Comments are closed.