Cyber Forensics Notes Pdf

Cyber Forensics Notes Pdf Cyber forensics notes free download as pdf file (.pdf), text file (.txt) or read online for free. cyber forensics is the process of extracting digital evidence from electronic devices to solve crimes. These crimes include cyber harassment and stalking, distribution of child pornography, credit card fraud, human trafficking, spoofing, identity theft, and online libel or slander.

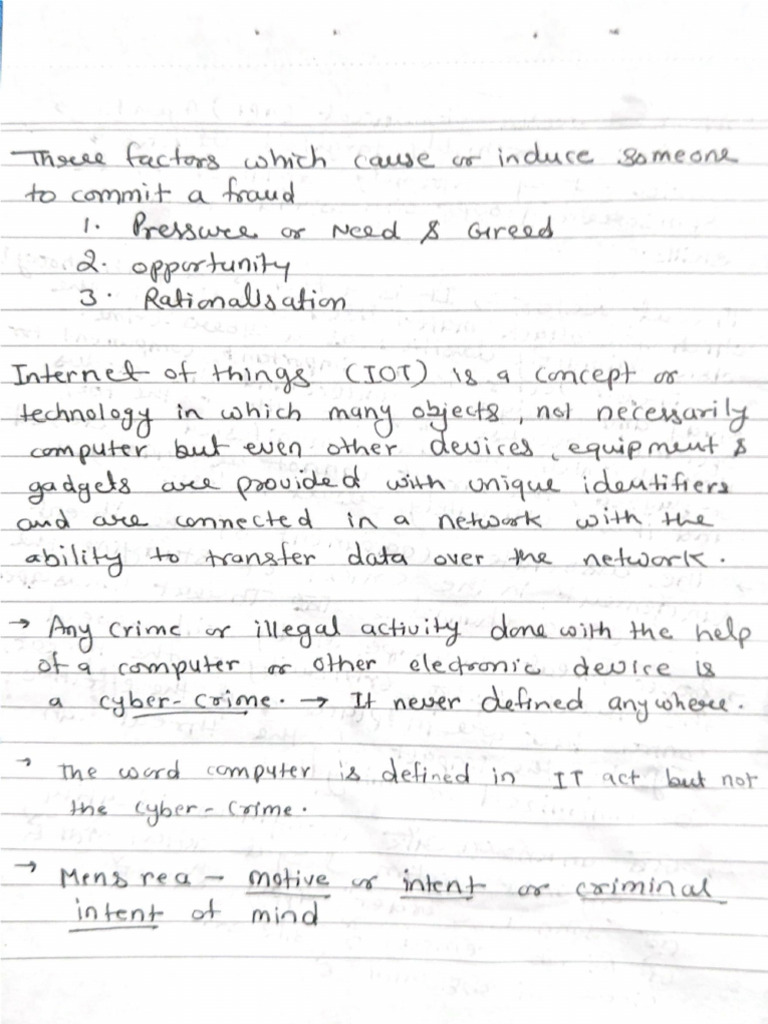
Digital Forensics Notes Pdf Key objectives of cyber forensics include rapid discovery of evidence, estimation of potential impact of the malicious activity on the victim, and assessment of the intent and identity of the perpetrator. Computer forensics is the application of investigation and analysis techniques to gather and preserve evidence. Cyber crime is defined as a crime in which a computer is the object of the crime (hacking, phishing, spamming) or is used as a tool to commit an offense (child pornography, hate crimes). Syllabus: introduction: computer forensics fundamentals – types of computer forensics technology – types of computer forensics systems – vendor and computer forensics services.

Fundamentals Of Cyber Forensics Pdf Cyber crime is defined as a crime in which a computer is the object of the crime (hacking, phishing, spamming) or is used as a tool to commit an offense (child pornography, hate crimes). Syllabus: introduction: computer forensics fundamentals – types of computer forensics technology – types of computer forensics systems – vendor and computer forensics services. Network forensics is used to determine how a security breach occurred; however, steps must betaken to harden networks before a security breach happens, particularly with recent increases innetwork attacks, viruses, and other security incidents. Cyber forensics encompasses a range of essential concepts that guide the investigation and analysis of digital evidence. these include data acquisition, which involves securely collecting and preserving data from various electronic devices. Cyber threats cyber warfare:cyber warfare refers to the use of digital attacks like computer viruses and hacking by one country to disrupt the vital computer systems of another, with the aim of creating damage, death and destruction. This lecture on digital and cyber forensics covers key principles, branches, and methodologies. it explores the classification of cybercrimes (individual, property, organizational, and societal), technical forensic methods, and real world examples.

Cyber Forensics Module 1 2 3 4 Pdf Network forensics is used to determine how a security breach occurred; however, steps must betaken to harden networks before a security breach happens, particularly with recent increases innetwork attacks, viruses, and other security incidents. Cyber forensics encompasses a range of essential concepts that guide the investigation and analysis of digital evidence. these include data acquisition, which involves securely collecting and preserving data from various electronic devices. Cyber threats cyber warfare:cyber warfare refers to the use of digital attacks like computer viruses and hacking by one country to disrupt the vital computer systems of another, with the aim of creating damage, death and destruction. This lecture on digital and cyber forensics covers key principles, branches, and methodologies. it explores the classification of cybercrimes (individual, property, organizational, and societal), technical forensic methods, and real world examples.
Cyber Security Notes Iibf Pdf Cyber threats cyber warfare:cyber warfare refers to the use of digital attacks like computer viruses and hacking by one country to disrupt the vital computer systems of another, with the aim of creating damage, death and destruction. This lecture on digital and cyber forensics covers key principles, branches, and methodologies. it explores the classification of cybercrimes (individual, property, organizational, and societal), technical forensic methods, and real world examples.

Cyber Security Module2 Notes Pdf Ransomware Cybercrime
Comments are closed.