Cyber Attacks Defending Against Social Engineering Systemagic

Defending Against Social Engineering Attacks A Comprehensive Guide Understand the different types of attacks and attack vectors that occur with social engineering. carefully examine existing cybersecurity controls to identify points of failure. In this article, we’ll discuss 13 of the most common types of social engineering attacks, explain how they work, provide real life examples, and share best practices for preventing them.

Cyber Attacks Defending Against Social Engineering Systemagic This paper provides a comprehensive exploration of social engineering attacks, encompassing their phases, types, and associated tools for simulation and defense across windows and linux. This blog explores what social engineering is, common attack types like phishing, baiting, pretexting, and tailgating, along with real life examples and defense strategies. Protect yourself from social engineering attacks like phishing, vishing, and baiting. learn expert tips to identify tactics, prevent breaches, and respond effectively to threats. This article explores what social engineering attacks are, the different types, how they’re executed, and how one can recognize and defend against them. it’s a critical read for anyone who’s online and wants to stay safe in the face of this growing threat.

Defending Against Social Engineering Attacks A Comprehensive Guide Protect yourself from social engineering attacks like phishing, vishing, and baiting. learn expert tips to identify tactics, prevent breaches, and respond effectively to threats. This article explores what social engineering attacks are, the different types, how they’re executed, and how one can recognize and defend against them. it’s a critical read for anyone who’s online and wants to stay safe in the face of this growing threat. The proposed survey starts by discovering the rq that motivates the authors to examine different aspects of social engineering attacks, preventive measures, and acknowledging technologies, such as ai and blockchain, in tackling social engineering attacks. Social engineering attacks leverage human interaction and emotions to manipulate the target. learn what social engineering is, its techniques, examples and how to protect against it. Learn what social engineering attacks are, how ai is shaping them. know effective strategies to defend your organization from human targeted cyber threats. Fortifying your business against social engineering attacks is crucial in today’s digital world. explore the 10 most essential strategies and major real life examples to bolster your security.

Defending Against Social Engineering Attacks The proposed survey starts by discovering the rq that motivates the authors to examine different aspects of social engineering attacks, preventive measures, and acknowledging technologies, such as ai and blockchain, in tackling social engineering attacks. Social engineering attacks leverage human interaction and emotions to manipulate the target. learn what social engineering is, its techniques, examples and how to protect against it. Learn what social engineering attacks are, how ai is shaping them. know effective strategies to defend your organization from human targeted cyber threats. Fortifying your business against social engineering attacks is crucial in today’s digital world. explore the 10 most essential strategies and major real life examples to bolster your security.

Defending Against Social Engineering Attacks Learn what social engineering attacks are, how ai is shaping them. know effective strategies to defend your organization from human targeted cyber threats. Fortifying your business against social engineering attacks is crucial in today’s digital world. explore the 10 most essential strategies and major real life examples to bolster your security.
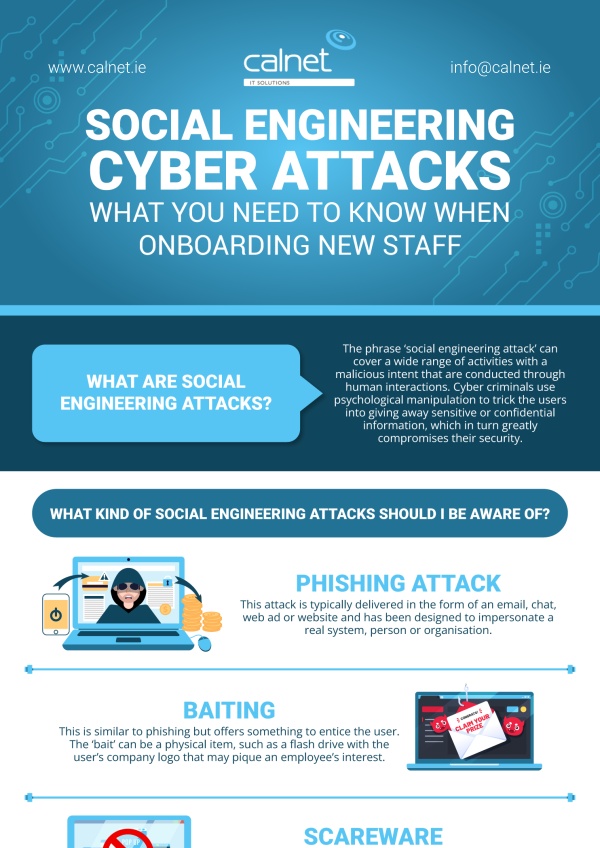
Social Engineering Cyber Attacks Infographic Calnet It Solutions
Comments are closed.