Cyber Attack Trends 2019 Mid Year Report Check Point Research

2019 Cyber Attack Trends Report Pdf Computer Security Security With data drawn from check point’s threatcloud world cyber threat map between january and june 2019, combined with primary research performed by the company’s cyber security experts , the following report holds a comprehensive overview of the trends observed in the various categories of cryptominers, ransomware, botnet, banking trojans. The following list of top attacks is based on data collected by the check point intrusion prevention system (ips) sensor net and details some of the most popular and interesting attack techniques and exploits observed by check point researchers in the first half of 2019.

Cyber Attack Trends Report Pdf Ransomware Security In this first installment of the 2019 security report we review the latest threats facing organizations in the fifth generation of the cyber landscape and provide you with our observations and insights from the past year. Check point research released its 2019 mid year report on cyber attack trends last month. the report puts targeted ransomware attacks at the top of its list of dominant ongoing trends in 2019. The document discusses rising trends in cyber attacks during the first half of 2019. it covers increased software supply chain attacks, evolving email scams, attacks on cloud environments, the mobile threat landscape, and ongoing ransomware and cryptomining attacks. With data drawn from check point's threatcloud world cyber threat map between january and june 2019, combined with primary research performed by the company's cyber security experts, the following report holds a comprehensive overview of the trends observed in the various categories of cryptominers, ransomware, botnet, banking trojans, data.
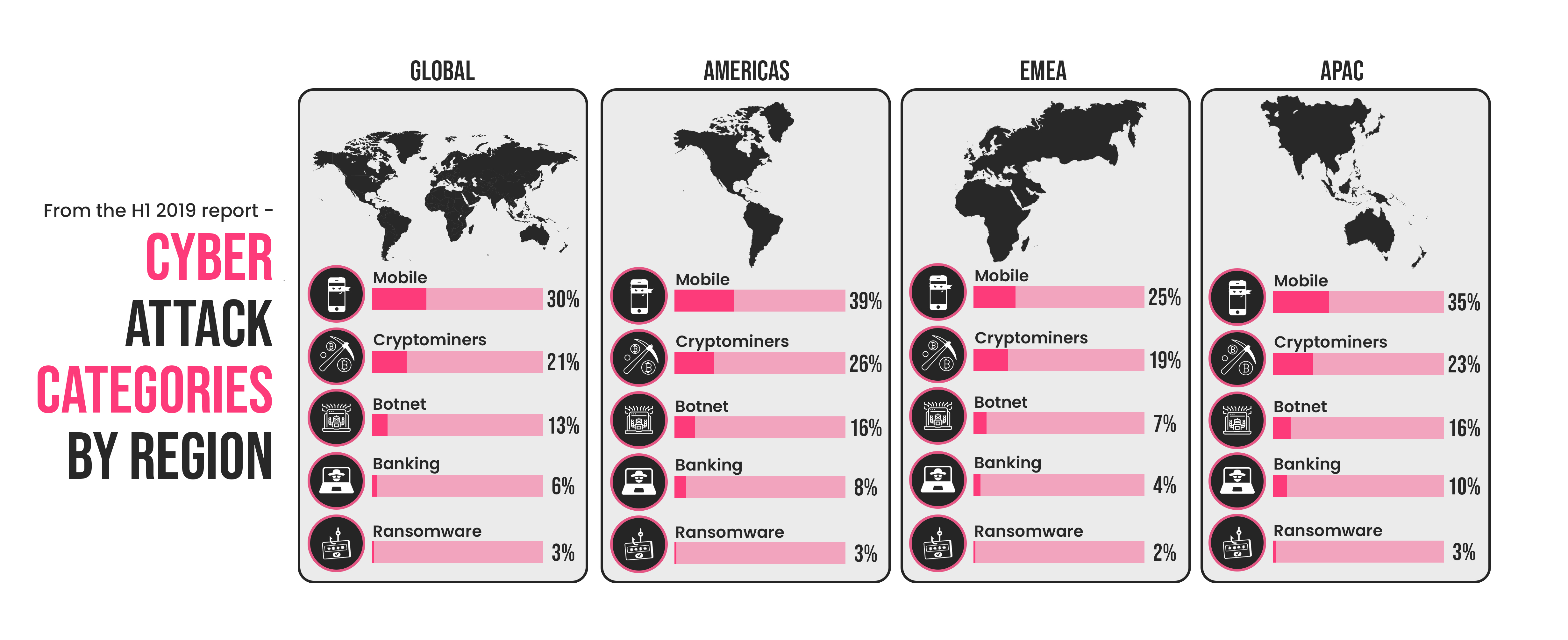
Cyber Attack Trends 2019 Mid Year Report Check Point Research The document discusses rising trends in cyber attacks during the first half of 2019. it covers increased software supply chain attacks, evolving email scams, attacks on cloud environments, the mobile threat landscape, and ongoing ransomware and cryptomining attacks. With data drawn from check point's threatcloud world cyber threat map between january and june 2019, combined with primary research performed by the company's cyber security experts, the following report holds a comprehensive overview of the trends observed in the various categories of cryptominers, ransomware, botnet, banking trojans, data. Read 3 answers by scientists to the question asked by alaa al zyadat on aug 23, 2019. Check point software technologies ltd. released its “cyber attack trends: 2019 mid year report”, revealing that no environment is immune to cyber attacks. Results in the cyber attack trends 2019 mid year report reveals threat actors have developed new tools and techniques in 2019. The “cyber attack trends: 2019 mid year report” conducted by checkpoint provides a detailed overview of the cyber threat landscape.

Cyber Attack Trends 2019 Mid Year Report Check Point Research Read 3 answers by scientists to the question asked by alaa al zyadat on aug 23, 2019. Check point software technologies ltd. released its “cyber attack trends: 2019 mid year report”, revealing that no environment is immune to cyber attacks. Results in the cyber attack trends 2019 mid year report reveals threat actors have developed new tools and techniques in 2019. The “cyber attack trends: 2019 mid year report” conducted by checkpoint provides a detailed overview of the cyber threat landscape.

Cyber Attack Trends 2019 Mid Year Report Check Point Research Results in the cyber attack trends 2019 mid year report reveals threat actors have developed new tools and techniques in 2019. The “cyber attack trends: 2019 mid year report” conducted by checkpoint provides a detailed overview of the cyber threat landscape.

Check Point S 2022 Mid Year Cyber Attack Trends Report Check Point
Comments are closed.