Cyber Attack Simulation Reevo

A Cyber Attack Simulation For Teaching Cybersecurity 4 Pdf Computer If you are planning changes to your systems or any of its components, the reevo service allows you to simulate different what if scenarios and zero day vulnerability simulations, to assess any cyber risks associated with these changes in advance and eliminate threats in advance. Discover how reevo’s cyber resilience lifecycle is redefining cyber risk management with a continuous, adaptive model that prioritizes resilience over invulnerability.

Cyber Attack Simulation Reevo The platform supports over 120,000 attack simulations, sourced from real world attack strategies and encompasses the entire cybersecurity kill chain. with these simulations, users can test for threat detection and evaluate controls for effectiveness. Questo servizio crea un digital twin (gemello digitale) dell'infrastruttura e, valutate le sue vulnerabilità, simula milioni di attacchi su di essa, calcolando tutti i possibili percorsi di attacco che possono essere sfruttati da un attaccante. With our continuous threat exposure management (ctem) service, you can detect and mitigate exposures before they are exploited, continuously simulating attacker behavior to anticipate their impact. Advanced protection for it ot according to iso iec 62443 and eu cyber resilience act. learn about our industrial soc h24x7 and cyber attack simulations.
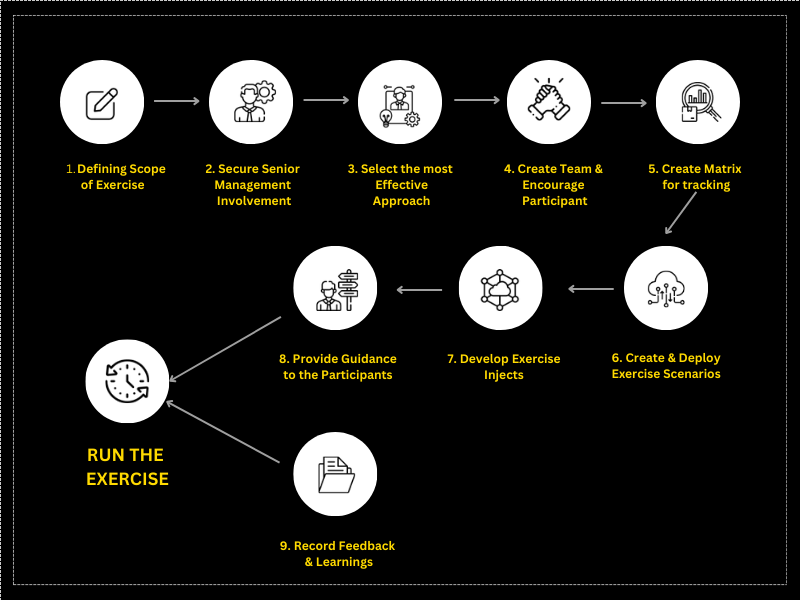
7 Steps To Perform A Cyber Attack Simulation With our continuous threat exposure management (ctem) service, you can detect and mitigate exposures before they are exploited, continuously simulating attacker behavior to anticipate their impact. Advanced protection for it ot according to iso iec 62443 and eu cyber resilience act. learn about our industrial soc h24x7 and cyber attack simulations. Raise your guard against phishing with reevo: simulation campaigns to assess and empower your users' attention. proactive security and ongoing training. Un gemelo digital para descubrir vulnerabilidades y todos los posibles escenarios de ataque de forma preventiva, sin comprometer tu infraestructura de producción. la solución de cyber attack simulation de reevo es esto y mucho más. Un jumeau numérique pour découvrir les vulnérabilités et tous les scénarios d'attaque possibles dans une perspective préventive, sans compromettre votre infrastructure de production. la solution de simulation des cyberattaques de reevo, c'est cela et bien plus encore. Train resilience with real world attack simulations. kymatio simulations reproduces phishing, smishing, vishing, qrshing, ransomware, and deepfake scenarios to measure alertness, identify vulnerabilities, and strengthen defenses across the organization.

Cybereason Attack Simulation Series Raise your guard against phishing with reevo: simulation campaigns to assess and empower your users' attention. proactive security and ongoing training. Un gemelo digital para descubrir vulnerabilidades y todos los posibles escenarios de ataque de forma preventiva, sin comprometer tu infraestructura de producción. la solución de cyber attack simulation de reevo es esto y mucho más. Un jumeau numérique pour découvrir les vulnérabilités et tous les scénarios d'attaque possibles dans une perspective préventive, sans compromettre votre infrastructure de production. la solution de simulation des cyberattaques de reevo, c'est cela et bien plus encore. Train resilience with real world attack simulations. kymatio simulations reproduces phishing, smishing, vishing, qrshing, ransomware, and deepfake scenarios to measure alertness, identify vulnerabilities, and strengthen defenses across the organization.
Cyber Attack Simulation Solutions Protect Your Network Edibbee Un jumeau numérique pour découvrir les vulnérabilités et tous les scénarios d'attaque possibles dans une perspective préventive, sans compromettre votre infrastructure de production. la solution de simulation des cyberattaques de reevo, c'est cela et bien plus encore. Train resilience with real world attack simulations. kymatio simulations reproduces phishing, smishing, vishing, qrshing, ransomware, and deepfake scenarios to measure alertness, identify vulnerabilities, and strengthen defenses across the organization.
Comments are closed.