Cryptography Unit 1 Notes Cryptography Cryptography Cryptography Is
Cryptography Notes Pdf Cryptography Encryption Cryptography is the art of secure communication in the presence of adversaries. it involves transforming plaintext into ciphertext using encryption algorithms and keys, with applications ranging from ancient ciphers to modern digital security. Cryptography cryptography is technique of securing information and communications through use of codes so that only that person for whom the information is intended can understand it and process it.

Unit 4 Notes Pdf Cryptography Encryption Cryptography is the science of securing information through transformation into unreadable formats, focusing on confidentiality, integrity, authentication, and non repudiation. This document provides information about the cs8792 cryptography & network security course. it discusses cryptography, the course outcomes, syllabus, and key concepts in cryptography including symmetric encryption, asymmetric encryption, data integrity algorithms, and authentication protocols. By the end of this unit, you should be able to comprehend cryptography's fundamental principles, recognize the importance of cryptographic building blocks, and apply mathematical concepts to secure communication and data protection. Explain the importance and application of each of confidentiality, integrity, authentication and availability and to understand various cryptographic algorithms. generate and distribute a pgp key pair and use the pgp package to send an encrypted e mail message. unit i.

Unit 1 Pdf Cryptography Encryption By the end of this unit, you should be able to comprehend cryptography's fundamental principles, recognize the importance of cryptographic building blocks, and apply mathematical concepts to secure communication and data protection. Explain the importance and application of each of confidentiality, integrity, authentication and availability and to understand various cryptographic algorithms. generate and distribute a pgp key pair and use the pgp package to send an encrypted e mail message. unit i. Cryptography and free speech: the cryptography involve not just products, it involves ideas too, although governments effectively control the flow of products across borders, controlling the floe ideas either head or on the internet, is also impossible. The design and analysis of today’s cryptographic algorithms is highly mathematical. do not try to design your own algorithms. i repeat: do not try to design your own algorithms; with rare exceptions, r avoid any product that brags of their own, “highly secure” encryption algorithms. Understand the basic concepts of cryptography, its goals, terminology, and how cryptographic systems work. this section explains the fundamentals of securing information and the basic components of cryptographic systems. Replay passive capture of a data unit and its subsequent retransmission to produce an unauthorized effect.

Unit Ii Pdf Public Key Cryptography Cryptography Cryptography and free speech: the cryptography involve not just products, it involves ideas too, although governments effectively control the flow of products across borders, controlling the floe ideas either head or on the internet, is also impossible. The design and analysis of today’s cryptographic algorithms is highly mathematical. do not try to design your own algorithms. i repeat: do not try to design your own algorithms; with rare exceptions, r avoid any product that brags of their own, “highly secure” encryption algorithms. Understand the basic concepts of cryptography, its goals, terminology, and how cryptographic systems work. this section explains the fundamentals of securing information and the basic components of cryptographic systems. Replay passive capture of a data unit and its subsequent retransmission to produce an unauthorized effect.
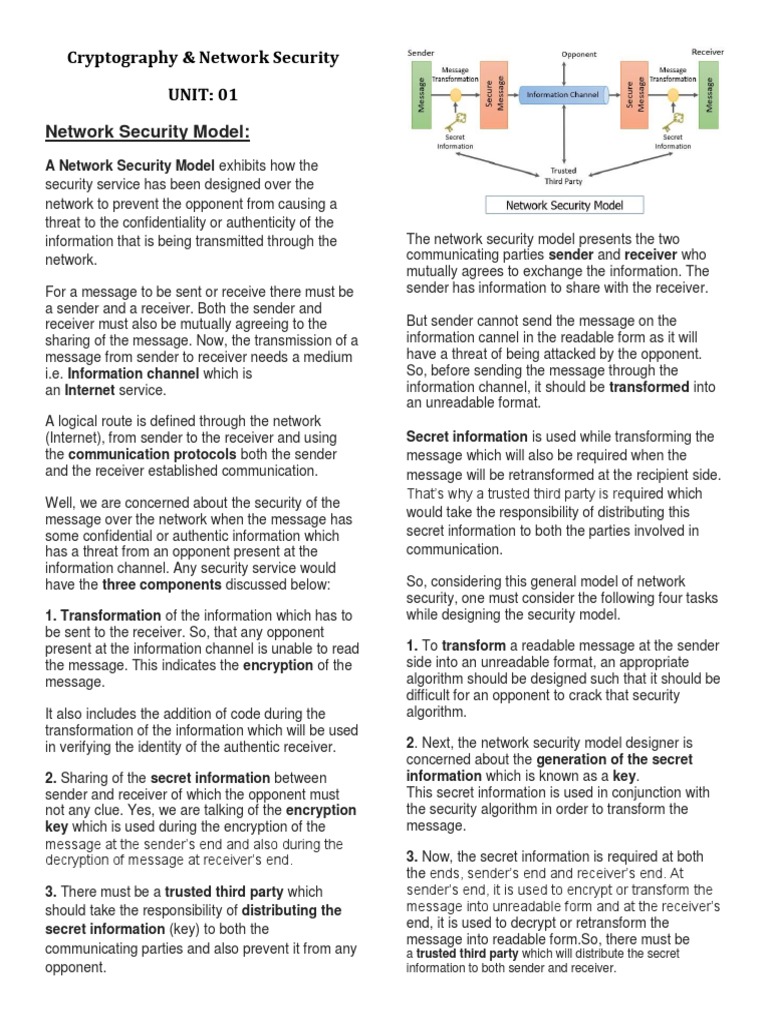
Cryptography Notes Pdf Cryptography Key Cryptography Understand the basic concepts of cryptography, its goals, terminology, and how cryptographic systems work. this section explains the fundamentals of securing information and the basic components of cryptographic systems. Replay passive capture of a data unit and its subsequent retransmission to produce an unauthorized effect.
Comments are closed.