Cryptography Pptx Programming Languages Computing
Cryptography Pptx Programming Languages Computing The document is a presentation on cryptography fundamentals, covering topics such as types of cryptography, mechanisms like symmetric and asymmetric encryption, and historical methods including steganography and ciphers. Two main parts 1. handshake protocol: establish shared secret key using public key cryptography 2. record layer: transmit data using negotiated key our starting point: using a key for encryption and integrity.

Cryptography Pptx Programming Languages Computing It covers practical applications in programming languages such as python, java, and javascript, while emphasizing secure practices for cryptographic implementation. the conclusion stresses the necessity for programmers to understand cryptography to effectively address security challenges. This browser version is no longer supported. please upgrade to a supported browser. Explore our fully editable and customizable powerpoint presentations on cryptography, designed to enhance your understanding of this essential field in information security. perfect for educators, students, and professionals alike. They can use cryptographic approaches to ensure secrecy, and do not rely only on secrecy of method. think about the security objective and adversary model in these examples.

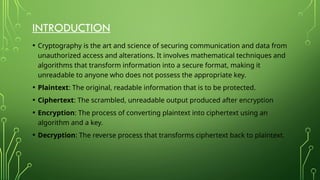
Computing Cryptography Powerpoint Templates Slides And Graphics Explore our fully editable and customizable powerpoint presentations on cryptography, designed to enhance your understanding of this essential field in information security. perfect for educators, students, and professionals alike. They can use cryptographic approaches to ensure secrecy, and do not rely only on secrecy of method. think about the security objective and adversary model in these examples. Course goal: realize when to consult an expert! cryptography (historically) “…the art of writing or solving codes…” historically, cryptography focused exclusively on ensuring private communication between two parties sharing secret information in advance using “codes” (aka private key encryption. Examine ciphertext, correlate properties with the assumptions. The document presents a technical paper on cryptography. it begins with definitions of cryptography and describes its main purposes as authentication, privacy, integrity, and non repudiation. Explore the fundamentals of cryptography, including secret key and public key functions, hash functions, security uses, and more. learn about security attacks, objectives of information security, and the types and uses of cryptographic functions.
Comments are closed.