Cryptography For Beginners Rsa Algorithm Explained Simply

An Example Of The Rsa Algorithm Pdf Cryptography Key Cryptography Public key cryptography: rsa algorithm is a public key cryptography algorithm, which means that it uses two different keys for encryption and decryption. the public key is used to encrypt the data, while the private key is used to decrypt the data. Rsa (rivest–shamir–adleman) is one of the most widely used public key cryptosystems. it’s based on asymmetric encryption, where two keys are used: a public key (shared with everyone) and a.

Rsa Algorithm Simple English Wikipedia The Free Encyclopedia Pdf Learn why factoring large numbers is so challenging and how this difficulty forms the backbone of modern encryption. 🤔 this video breaks down the rsa algorithm step by step, from key. Here you can see how to encrypt and decrypt using the rsa procedure step by step. the security of rsa is based on the fact that it is easy to calculate the product n n of two large prime numbers p p and q q. however, it is very difficult to determine the two primes only from the product n n. Rsa works by creating a pair of “commutative keys” — meaning if you encrypt with one, you can decrypt with the other. in rsa, if you use the public key to encrypt, you must use the private key to decrypt (and vice versa). Learn about the rsa algorithm, a crucial public key encryption method. discover how it secures data, its workings, and its applications in modern cryptography.
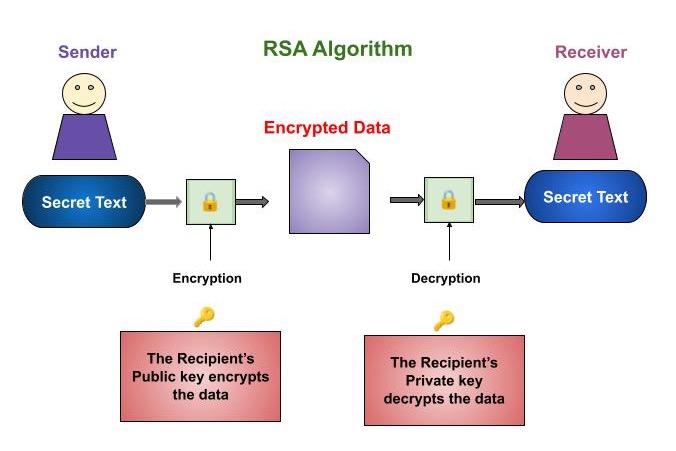
Cryptography Rsa Algorithm Rsa works by creating a pair of “commutative keys” — meaning if you encrypt with one, you can decrypt with the other. in rsa, if you use the public key to encrypt, you must use the private key to decrypt (and vice versa). Learn about the rsa algorithm, a crucial public key encryption method. discover how it secures data, its workings, and its applications in modern cryptography. Rsa (rivest shamir adleman) is a famous encryption scheme that makes use of a combination of public and private keys. this means you have a non public key and one that can be shared publicly. each key can be used to encrypt data, but only the opposite can be decrypted. In this blog, we’ll break down how the rsa algorithm works in a simple, step by step way. you’ll see a real example, learn where rsa is used in real life, understand the types of attacks it can face, and how it compares to other methods like aes. This guide breaks down rsa into clear, understandable components without sacrificing mathematical rigor. whether you're a student, developer, or simply curious about the technology that secures our digital world, this resource will help you grasp both the "how" and "why" behind rsa encryption. Reading and writing encrypted messages is called cryptography. there are different kinds of cryptography. cryptography that uses two numbers (keys), like rsa, is called asymmetric cryptography and public key cryptography. usually only reading encrypted messages is important. anyone may write them.

Cryptography Rsa Algorithm Rsa Examples Pptx Rsa (rivest shamir adleman) is a famous encryption scheme that makes use of a combination of public and private keys. this means you have a non public key and one that can be shared publicly. each key can be used to encrypt data, but only the opposite can be decrypted. In this blog, we’ll break down how the rsa algorithm works in a simple, step by step way. you’ll see a real example, learn where rsa is used in real life, understand the types of attacks it can face, and how it compares to other methods like aes. This guide breaks down rsa into clear, understandable components without sacrificing mathematical rigor. whether you're a student, developer, or simply curious about the technology that secures our digital world, this resource will help you grasp both the "how" and "why" behind rsa encryption. Reading and writing encrypted messages is called cryptography. there are different kinds of cryptography. cryptography that uses two numbers (keys), like rsa, is called asymmetric cryptography and public key cryptography. usually only reading encrypted messages is important. anyone may write them.
Comments are closed.