Cryptography 5 Exercises Computer Science Docsity

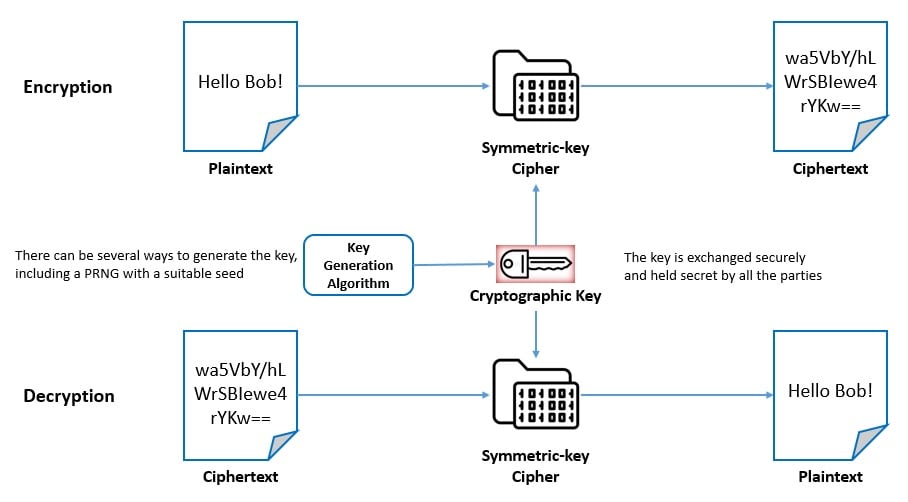
Cryptography 5 Exercises Computer Science Docsity Looking for exercises in cryptography and system security? download now thousands of exercises in cryptography and system security on docsity. Modern encryption techniques (e.g., rsa and aes) are much more sophisticated than the shift ciphers we’ve looked at in this exercise. but the idea is the same: you apply a “key” to some plaintext and transmit the resulting ciphertext.

Cs402 Cryptography Worksheet Exercises Cryptography And System Exercise 12: your opponent has invented a new stream cipher mode of operation for 128 bit key aes. he thinks that ofb could be improved by feeding back into the key port rather than the data port of the aes chip. Cryptography homework 5 free download as pdf file (.pdf), text file (.txt) or read online for free. Homework exercises from the "understanding cryptography" textbook and accompanying lecture series. Exercise 1 (shift cipher). a secret message m is encrypted with the shift cipher using a secret key k.
Introduction To Cryptography Baeldung On Computer Science Homework exercises from the "understanding cryptography" textbook and accompanying lecture series. Exercise 1 (shift cipher). a secret message m is encrypted with the shift cipher using a secret key k. (reducing the error of randomized algorithms) suppose we have randomized algorithm for computing a function f which gives an incorrect answer with probability ≤ 1 3, and we want to reduce its error by repeating it several times and taking a majority vote. Cryptography 3, exercises computer science, exercises for cryptography and system security. Looking for assignments in cryptography and system security? download now thousands of assignments in cryptography and system security on docsity. Cryptography 4, exercises computer science, exercises for cryptography and system security.

Ks3 Computing Cryptography Cover Lesson Teaching Resources (reducing the error of randomized algorithms) suppose we have randomized algorithm for computing a function f which gives an incorrect answer with probability ≤ 1 3, and we want to reduce its error by repeating it several times and taking a majority vote. Cryptography 3, exercises computer science, exercises for cryptography and system security. Looking for assignments in cryptography and system security? download now thousands of assignments in cryptography and system security on docsity. Cryptography 4, exercises computer science, exercises for cryptography and system security.
Comments are closed.