Create And Improve Tutorial For Gpg Files After Ubuntu Upgrade
Create And Improve Tutorial For Gpg Files After Ubuntu Upgrade This warning you see if because of the changes being bring in the newer ubuntu and debian versions. the apt key command is being deprecated and there is new guideline on how to handle the keys. Learn how to manage gpg keys on ubuntu, including generating key pairs, key servers, subkeys, revocation certificates, and security best practices for long term key management.
Create And Improve Tutorial For Gpg Files After Ubuntu Upgrade You’ll learn the modern gpg based approach to repository management, understand why the old methods are being phased out, and get hands on with practical examples that work reliably on ubuntu 24.04 and beyond. Master the gpg command in linux for file encryption, digital signatures, and secure communication. complete guide with practical examples and best practices. In this article, we'll walk you through adding the repositories, importing the signing key, and installing gnupg cleanly on your system. the repositories listed below provide either the latest stable release (currently 2.4.x) or the latest development version (2.5.x). By following these steps, you’ve successfully integrated a new ppa with a gpg key into your system, adopting the newer, more secure method recommended for debian and ubuntu systems.
How To Fix Ubuntu Apt Update Gpg Errors Cicdtrail Technology In this article, we'll walk you through adding the repositories, importing the signing key, and installing gnupg cleanly on your system. the repositories listed below provide either the latest stable release (currently 2.4.x) or the latest development version (2.5.x). By following these steps, you’ve successfully integrated a new ppa with a gpg key into your system, adopting the newer, more secure method recommended for debian and ubuntu systems. When working with secret keys it’s generally preferable not to write them to files and, instead, use ssh to copy them directly between machines using only gpg and a pipe:. Gpg (gnu privacy guard) is a powerful tool for creating cryptographic keys, encrypting and decrypting data, and digitally signing content. this tutorial will guide you through generating gpg keys, exporting and managing them, and using gpg to encrypt, decrypt, and sign messages. Installing and using gpg on ubuntu is a powerful way to enhance your data security. by following the steps outlined in this blog, you can generate key pairs, encrypt and decrypt data, and sign and verify files. In the following, we'll review the old and new ways of managing repository keys, and why the signed by directive is a more secure solution than before.
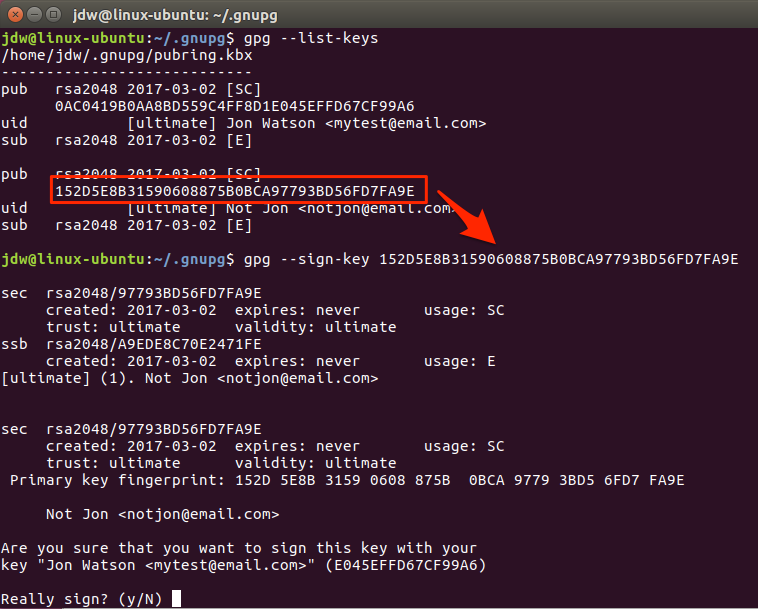
21 Generate Gpg Key Ubuntu Generatekey When working with secret keys it’s generally preferable not to write them to files and, instead, use ssh to copy them directly between machines using only gpg and a pipe:. Gpg (gnu privacy guard) is a powerful tool for creating cryptographic keys, encrypting and decrypting data, and digitally signing content. this tutorial will guide you through generating gpg keys, exporting and managing them, and using gpg to encrypt, decrypt, and sign messages. Installing and using gpg on ubuntu is a powerful way to enhance your data security. by following the steps outlined in this blog, you can generate key pairs, encrypt and decrypt data, and sign and verify files. In the following, we'll review the old and new ways of managing repository keys, and why the signed by directive is a more secure solution than before.

How To Set Up And Use Gpg For Ubuntu With Pictures Wikihow Installing and using gpg on ubuntu is a powerful way to enhance your data security. by following the steps outlined in this blog, you can generate key pairs, encrypt and decrypt data, and sign and verify files. In the following, we'll review the old and new ways of managing repository keys, and why the signed by directive is a more secure solution than before.
Comments are closed.