Contrast Assess Application Code Security Contrast
Assess Contrast assess secures every line of code and identifies hidden application vulnerabilities in real time with industry leading accuracy. Contrast assess empowers teams to ship code faster and more securely by continuously and passively assessing their applications for security issues across all software development and delivery pipelines.
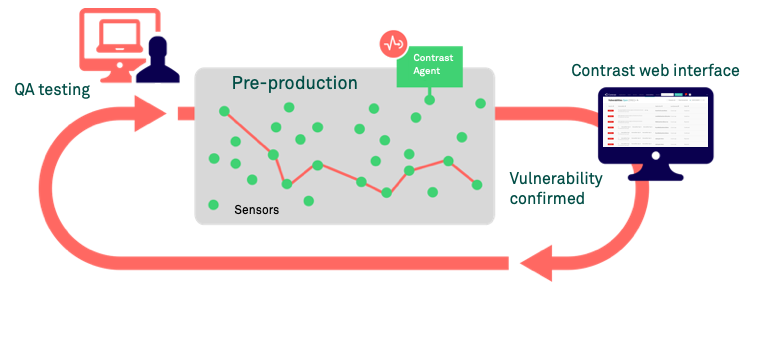
Contrast Assess Application Code Security Contrast Contrast provides automated tools that work on or in your code to find security flaws at different stages of development. during testing, a monitoring agent works inside the application to gather accurate security information from running apis. How is contrast assess different than dast? traditional dast tools try to exploit the running application with attacks, and detect vulnerabilities by analyzing http responses – but dast is blind to what occurs within the application, and provides only limited coverage of an application. Contrast assess is an innovative, automated application security testing solution that infuses software with vulnerability assessment capabilities so that security flaws are automatically identified. Contrast maps how your application processes data at runtime, showing the paths from http request through business logic to back end connections. this visualization helps both security teams and developers understand the application’s real attack surface.

Contrast Assess Application Code Security Contrast Contrast assess is an innovative, automated application security testing solution that infuses software with vulnerability assessment capabilities so that security flaws are automatically identified. Contrast maps how your application processes data at runtime, showing the paths from http request through business logic to back end connections. this visualization helps both security teams and developers understand the application’s real attack surface. The contrast application security platform continuously identifies application vulnerabilities in custom and open source code—from left in development through release to production. The contrast application security platform continuously identifies application vulnerabilities in custom and open source code—from left in development through release to production. Script to help output contrast assess rules in json or yaml. rule defaults and application overrides are both written to disk. rule configuration is retrieved from contrast only, changes to the output contents will not be reflected back in contrast. The platform provides full stack security assessment covering custom code, third party applications, and all dependencies. contrast ast is built on the contrast graph, which provides runtime intelligence to build a unified, real time security model across the application and api security ecosystem.
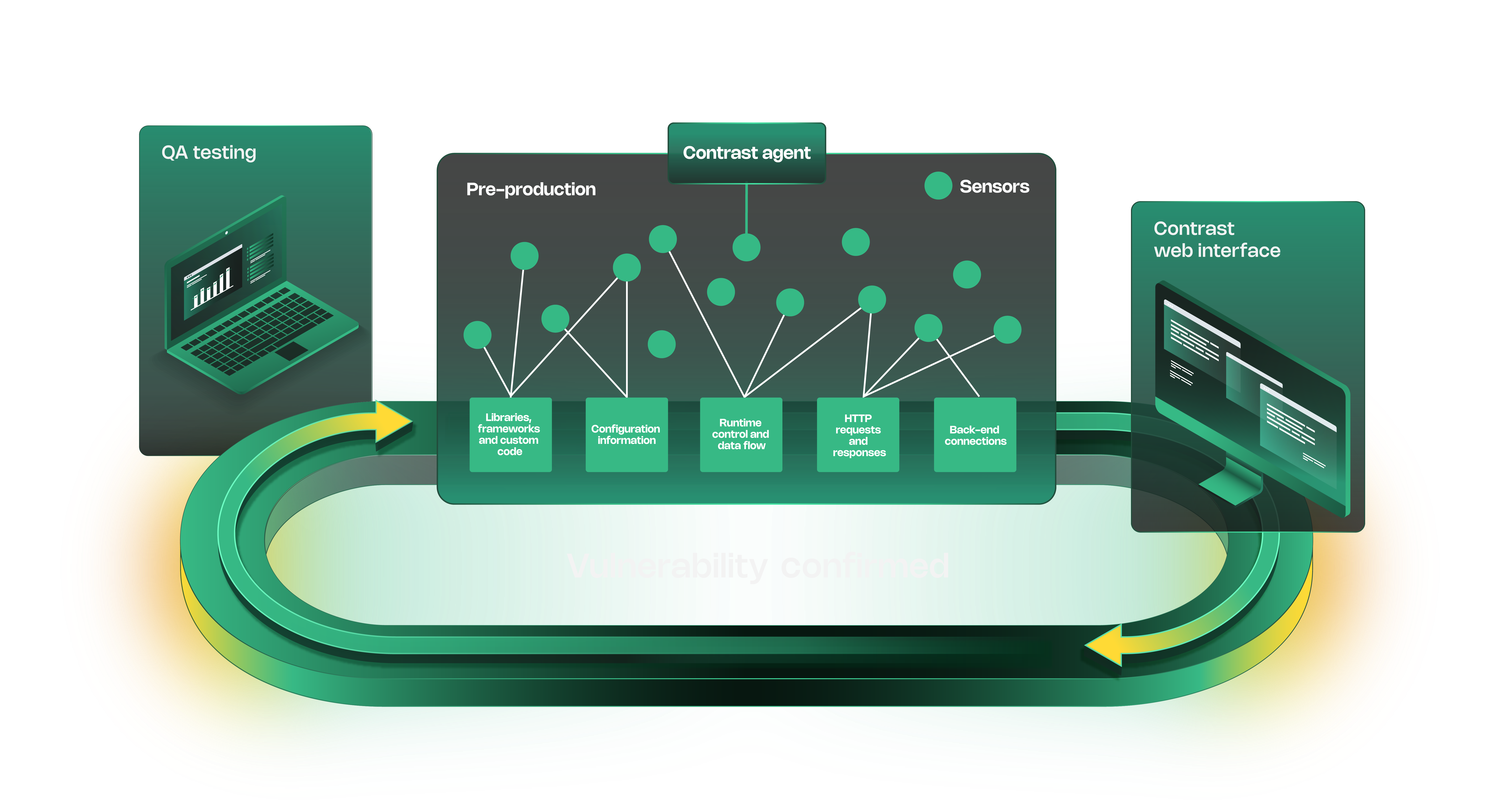
Contrast Assess Application Code Security Contrast The contrast application security platform continuously identifies application vulnerabilities in custom and open source code—from left in development through release to production. The contrast application security platform continuously identifies application vulnerabilities in custom and open source code—from left in development through release to production. Script to help output contrast assess rules in json or yaml. rule defaults and application overrides are both written to disk. rule configuration is retrieved from contrast only, changes to the output contents will not be reflected back in contrast. The platform provides full stack security assessment covering custom code, third party applications, and all dependencies. contrast ast is built on the contrast graph, which provides runtime intelligence to build a unified, real time security model across the application and api security ecosystem.
Comments are closed.