Continuous Hacking Methodology Fluid Attacks Help

Fluid Attacks Fluidattacks Instagram Photos And Videos Fluid attacks helps you develop secure software and have secure deployments into production. to ensure secure development, fluid attacks performs tests during the entire sdlc. Fluid attacks provides continuous security testing throughout the development process, with support from security experts and genai assistance. the platform is designed to help organizations identify attack surfaces early in development and encourage rapid vulnerability remediation without delaying software delivery.

Fluid Attacks Achieves Crest Accreditation For Penetration Testing What is fluid attacks continuous hacking? fluid attacks helps teams prevent, detect, manage, and remediate vulnerabilities with precision by combining our ai native scanners, deterministic scanners, and certified penetration testers. Fluid attacks helps you develop secure software and have secure deployments into production. to ensure secure development, fluid attacks performs tests during the entire sdlc. Fluid attacks' continuous hacking combines tools, ai and pentesters across the sdlc to detect and help remediate security vulnerabilities in software products. Learn about the scope, requirements, and workflow of the proof of value (a replacement for the poc) of fluid attacks' continuous hacking advanced plan.
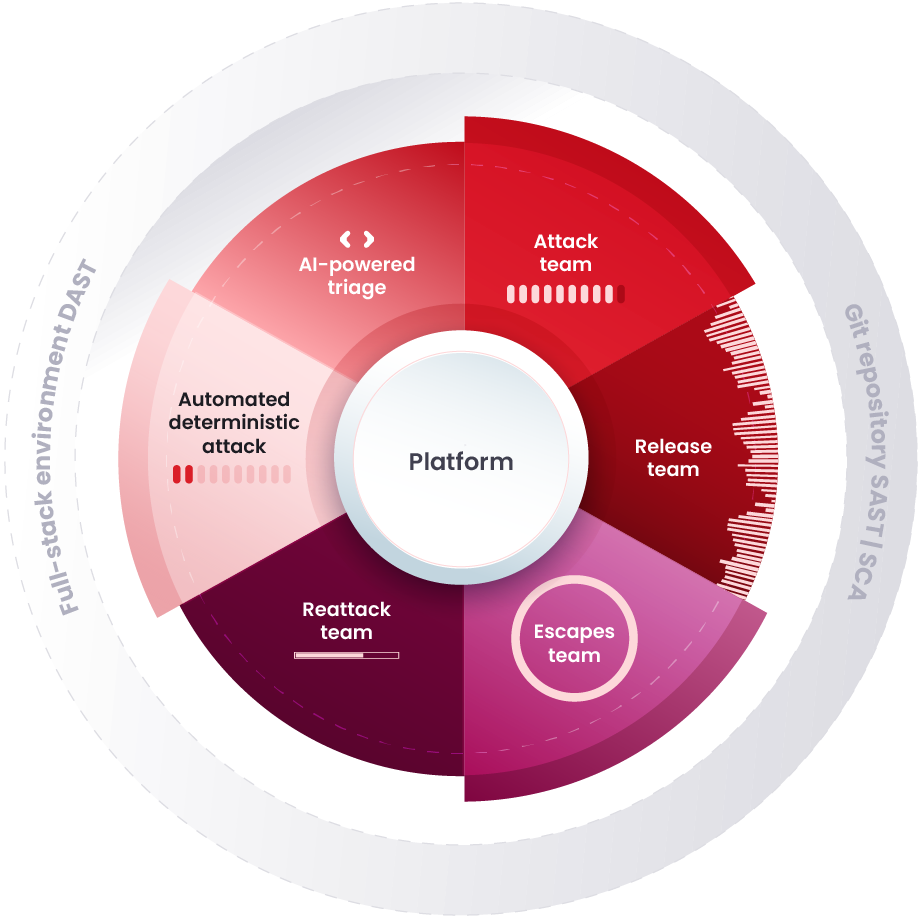
Continuous Hacking Methodology Fluid Attacks Help Fluid attacks' continuous hacking combines tools, ai and pentesters across the sdlc to detect and help remediate security vulnerabilities in software products. Learn about the scope, requirements, and workflow of the proof of value (a replacement for the poc) of fluid attacks' continuous hacking advanced plan. What is sast? what is dast? still can’t find an answer? send us a ticket and we will get back to you. Learn about the scope, requirements, and workflow of the proof of value (a replacement for the poc) of fluid attacks' continuous hacking advanced plan. Our continuous hacking detects and reports vulnerabilities and security issues during the whole software development lifecycle. Implement fluid attacks' comprehensive, ai powered solution into your sdlc and develop secure software without delays. as an all in one solution, fluid attacks accurately finds and helps you remediate vulnerabilities throughout the sdlc and ensures secure software development.
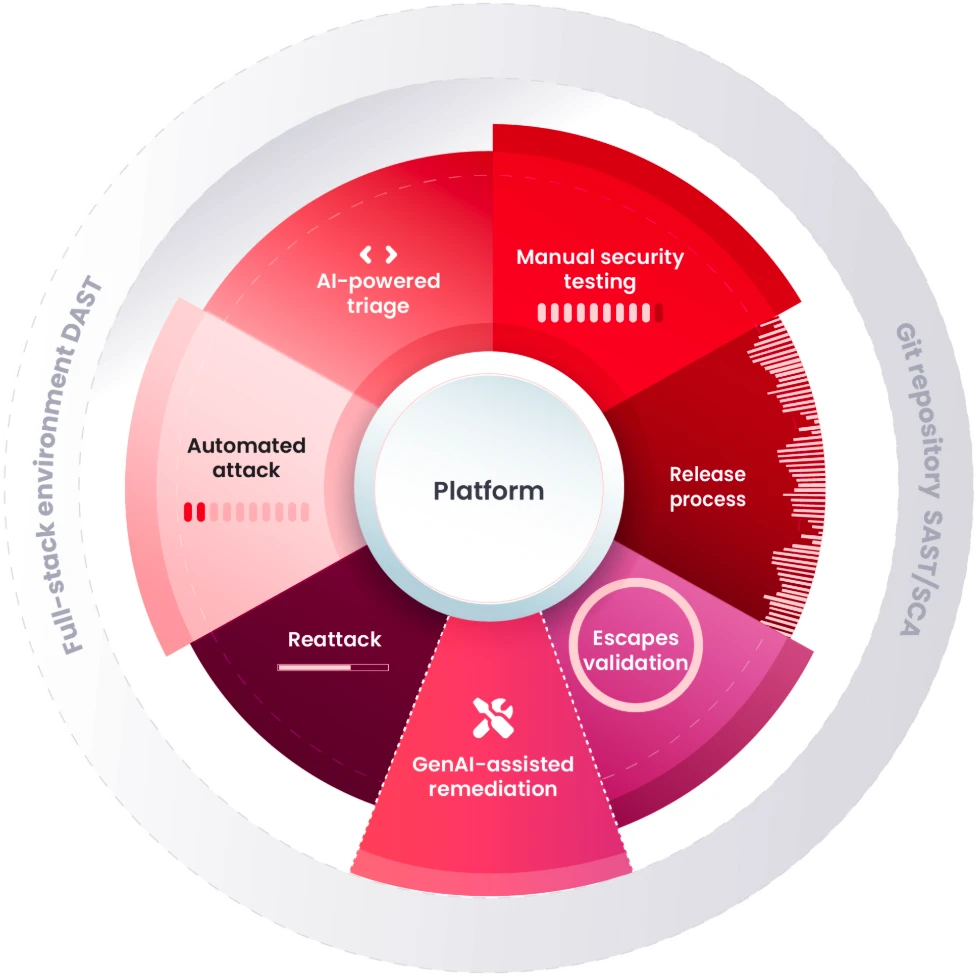
Continuous Hacking Methodology Fluid Attacks Help What is sast? what is dast? still can’t find an answer? send us a ticket and we will get back to you. Learn about the scope, requirements, and workflow of the proof of value (a replacement for the poc) of fluid attacks' continuous hacking advanced plan. Our continuous hacking detects and reports vulnerabilities and security issues during the whole software development lifecycle. Implement fluid attacks' comprehensive, ai powered solution into your sdlc and develop secure software without delays. as an all in one solution, fluid attacks accurately finds and helps you remediate vulnerabilities throughout the sdlc and ensures secure software development.
Comments are closed.