Computer Mac Addresses Explained Hacker 10 Security Hacker
Computer Mac Addresses Explained Hacker 10 Security Hacker Dynamac: freeware application to view and change any computer mac address, including wireless cards, the user can specify the mac address that should be used, the old address can easily be reset to the original one with a single click. One of the key identifiers that the router will use is the unique mac address for each device. how can a hacker make use of this? if the hacker is able to obtain the mac address for any device on the network, they can use something called mac address spoofing.

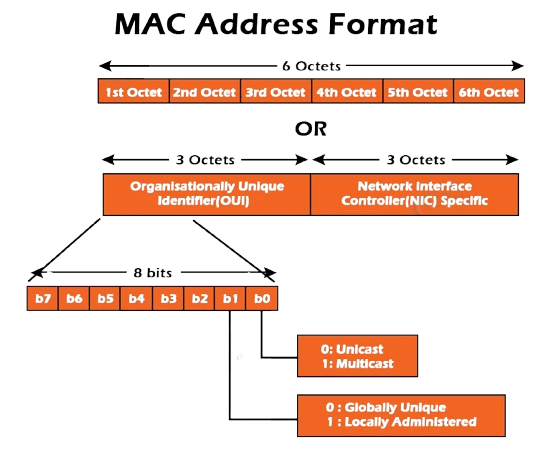
Computer Mac Addresses Explained Hacker 10 Security Hacker Discover how hackers use mac spoofing to bypass security and learn simple, effective ways to protect your network from these hidden threats. Various warning signs of a mac spoofing attack include duplicate ip addresses, unknown mac addresses, and any other unusual network activities. you can prevent mac spoofing attacks by implementing zero trust security principles in your network. Before diving into spoofing, it’s important to understand what a mac address is. a mac (media access control) address is a unique hardware identifier assigned to network interface cards (nics) in devices like laptops, smartphones, routers, and more. Fast and easy mac address lookup on ieee directory and wireshark manufacturer database. search vendor, manufacturer or organization of a device by mac oui address.
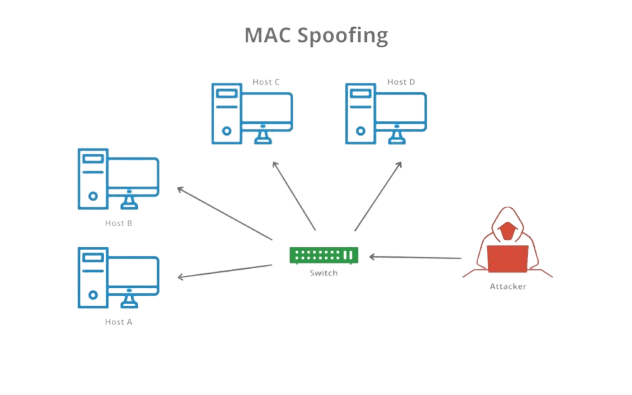
Mac Addresses Functions Risks And Management Updated 2025 Before diving into spoofing, it’s important to understand what a mac address is. a mac (media access control) address is a unique hardware identifier assigned to network interface cards (nics) in devices like laptops, smartphones, routers, and more. Fast and easy mac address lookup on ieee directory and wireshark manufacturer database. search vendor, manufacturer or organization of a device by mac oui address. However, despite being fundamental to networking, mac addresses are not infallible. attackers can exploit vulnerabilities associated with them, notably through a technique known as mac address spoofing. What role do mac addresses play in networking and security? learn about their uses in proxies, risks of mac spoofing, and the importance of anonymity and privacy. In layman’s terms, mac spoofing is when someone or something intercepts, manipulate or otherwise tampers with the control messages exchanged between a networked device and its unique mac address. To perform mac spoofing, the attacker needs to first find the mac address of the target device that they want to impersonate. they can do this by scanning the network for eligible mac addresses.
Mac Addresses Functions Risks And Management Updated 2025 However, despite being fundamental to networking, mac addresses are not infallible. attackers can exploit vulnerabilities associated with them, notably through a technique known as mac address spoofing. What role do mac addresses play in networking and security? learn about their uses in proxies, risks of mac spoofing, and the importance of anonymity and privacy. In layman’s terms, mac spoofing is when someone or something intercepts, manipulate or otherwise tampers with the control messages exchanged between a networked device and its unique mac address. To perform mac spoofing, the attacker needs to first find the mac address of the target device that they want to impersonate. they can do this by scanning the network for eligible mac addresses.
Comments are closed.