Computer Forensic Pdf

Computer Crime And Forensic Investigation Pdf Pdf Security Hacker The discipline that combines elements of law and computer science to collect and analyze data from computer systems, networks, wireless communications, and storage devices in a way that is admissible in a court of law. Computer forensic experts must understand how computer hard disks and floppy diskettes are structured and how computer evidence can reside at various levels within the structure of the disk.

Computer Forensics Fundamentals Pdf This chapter focuses on the essential components of report writing in computer forensics, including the significance of reports, guidelines for crafting them, and the integration of findings from forensic tools. Today, many computer forensics workshops have been created to familiarize investigators and security personnel with the basic techniques and tools necessary for a successful investigation of internet and computer related crimes. Esai tepat waktu. buku ini berisi tentang komputer forensik yang dijelask. n secara lengkap. komputer forensik merupakan cabang dari ilmu forensik yang fokus pada penyelidikan dan analisis data yang terkait dengan sistem komp. This document provides an introduction to computer forensics and digital investigation, illustrated through a case scenario of data theft in an organization.

01 Computer Forensics Fundamentals Pdf Computer Forensics Expert Esai tepat waktu. buku ini berisi tentang komputer forensik yang dijelask. n secara lengkap. komputer forensik merupakan cabang dari ilmu forensik yang fokus pada penyelidikan dan analisis data yang terkait dengan sistem komp. This document provides an introduction to computer forensics and digital investigation, illustrated through a case scenario of data theft in an organization. The computer forensics specialist should take several careful steps to identify and attempt toretrieve possible evidence that may exist on a subject’s computer system. The proposed research survey focuses on identifying the current state of the art digital forensics concepts in existing research, sheds light on research gaps, presents a detailed introduction of. Updated coverage includes new software and technologies as well as up to date reference sections, and content includes how to set up a forensics lab, how to acquire and evaluate the necessary tools, and how to conduct an investigation and subsequent digital analysis. Syllabus: introduction: computer forensics fundamentals – types of computer forensics technology – types of computer forensics systems – vendor and computer forensics services.

Module 02 Computer Forensics Investigation Process Pdf Computer The computer forensics specialist should take several careful steps to identify and attempt toretrieve possible evidence that may exist on a subject’s computer system. The proposed research survey focuses on identifying the current state of the art digital forensics concepts in existing research, sheds light on research gaps, presents a detailed introduction of. Updated coverage includes new software and technologies as well as up to date reference sections, and content includes how to set up a forensics lab, how to acquire and evaluate the necessary tools, and how to conduct an investigation and subsequent digital analysis. Syllabus: introduction: computer forensics fundamentals – types of computer forensics technology – types of computer forensics systems – vendor and computer forensics services.
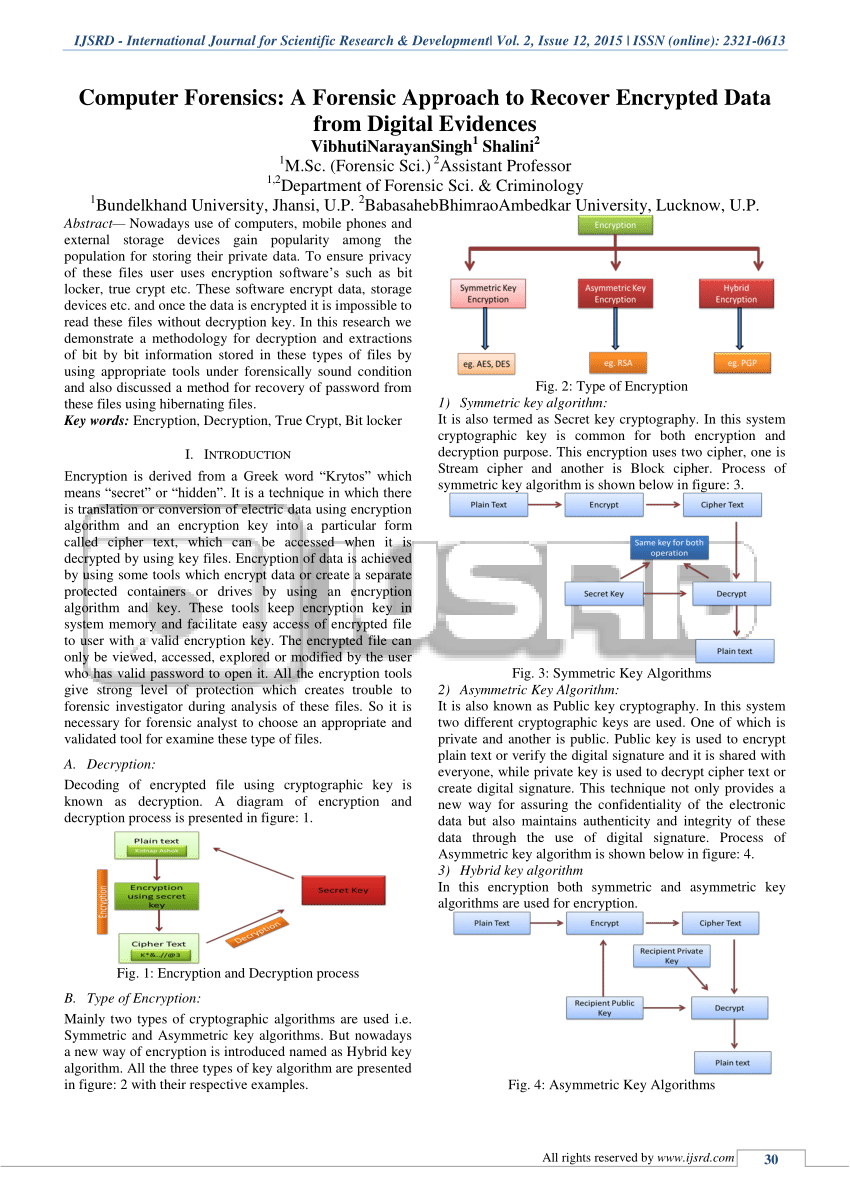
Pdf Computer Forensics A Forensic Approach To Recover Encrypted Data Updated coverage includes new software and technologies as well as up to date reference sections, and content includes how to set up a forensics lab, how to acquire and evaluate the necessary tools, and how to conduct an investigation and subsequent digital analysis. Syllabus: introduction: computer forensics fundamentals – types of computer forensics technology – types of computer forensics systems – vendor and computer forensics services.
Comments are closed.