Common Secrets Security Misconfiguration That Create Vulnerabilities

Common Secrets Security Misconfiguration That Create Vulnerabilities Understanding secrets security misconfigurations requires a keen understanding of where vulnerabilities typically arise, especially concerning secrets management, api interactions, and credentials handling. here are some of the common secrets security misconfigurations:. Understanding secrets security misconfigurations requires a keen understanding of where vulnerabilities typically arise, especially concerning secrets management, api interactions, and credentials handling. here are some of the common secrets security misconfigurations:.

Common Secrets Security Misconfiguration That Create Vulnerabilities Moving up from #5 in the previous edition, 100% of the applications tested were found to have some form of misconfiguration, with an average incidence rate of 3.00%, and over 719k occurrences of a common weakness enumeration (cwe) in this risk category. Security misconfigurations are a top cyber risk. experts reveal the most common setup errors they see and how teams can fix them before attackers take advantage. In this article, we will discuss in detail security misconfigurations and their impacts on cybersecurity. we will begin to define what security misconfiguration is, discuss its causes, and deepen our analysis of its impacts on organizations. Common security misconfiguration examples include unpatched systems, weak access controls and exposed cloud services. impacts of security misconfiguration can range from data breaches and regulatory fines to reputational loss.
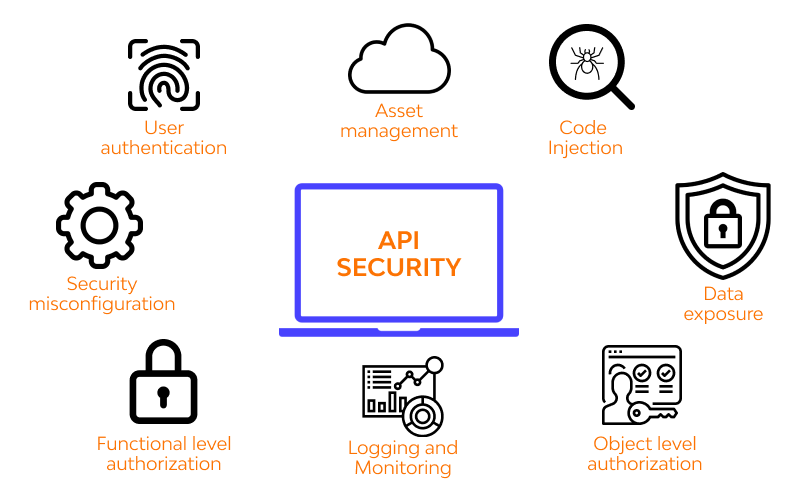
5 Most Common Security Misconfiguration Vulnerabilities And Their In this article, we will discuss in detail security misconfigurations and their impacts on cybersecurity. we will begin to define what security misconfiguration is, discuss its causes, and deepen our analysis of its impacts on organizations. Common security misconfiguration examples include unpatched systems, weak access controls and exposed cloud services. impacts of security misconfiguration can range from data breaches and regulatory fines to reputational loss. Bright automates the detection of security misconfiguration and hundreds of other vulnerabilities. the reports come with zero false positives and clear remediation guidelines for the whole team. When the options, permissions, and modes of all assets in your environment are configured securely, the chance of a successful security breach declines significantly. this guide highlights ten of the most common types of security misconfigurations and explains how scm can help with some. Many cloud security breaches can be traced to misconfigurations related to managing secrets, api interactions, and credentials handling. these vulnerabilities lead to unauthorized access, data breaches, and other security issues. What are the most common security misconfigurations in it systems and how can you prevent them? security misconfigurations remain one of the leading causes of data breaches and system vulnerabilities in modern it environments.
Comments are closed.