Common Hacking Techniques Technolush
Top 5 Common Hacking Techniques And How To Defend Against Them This post provides the list of commonly used hacking techniques used by hackers to exploit internet users. it's not an exhaustive list and covers only the most common attacks. Understanding the different types of hackers and the common techniques they use—like viruses, phishing, and ransomware—can help you stay alert and take simple steps to protect your data.

30 The Most Common Hacking Techniques And How To Deal With Them There are many types of cyberattacks, and as technology advances, more types emerge. however, there are some hacking techniques that are the most common and used by cybercriminals, as they are the most effective for achieving their objectives. Ui redress, dns spoofing, brute force are among the common hacking techniques. read this article by techfunnel to know more such latest hacking techniques. In the digital age, understanding hacking techniques is crucial for ethical hackers and security professionals. this post will cover 40 popular hacking techniques, providing insights into their methods, notable examples, and tools that can be used to combat them. Hacking techniques are methods used to exploit vulnerabilities in systems, networks, or human behavior to gain unauthorized access. these can range from basic password guessing to sophisticated nation state attacks.

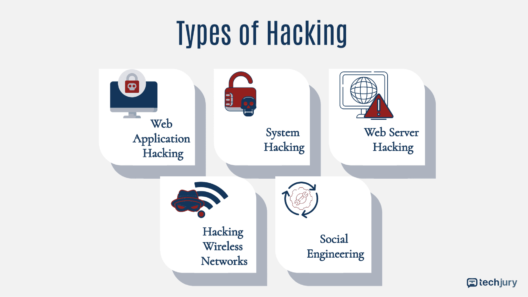
Common Hacking Techniques Understanding Types Of Hackers In the digital age, understanding hacking techniques is crucial for ethical hackers and security professionals. this post will cover 40 popular hacking techniques, providing insights into their methods, notable examples, and tools that can be used to combat them. Hacking techniques are methods used to exploit vulnerabilities in systems, networks, or human behavior to gain unauthorized access. these can range from basic password guessing to sophisticated nation state attacks. Understanding the common ttps employed by hackers helps security professionals implement defensive measures. let’s take a closer look at some of the most frequently used tactics, techniques, and procedures in modern cyberattacks. As cyberattacks become more sophisticated, it‘s critical to understand the different hacking techniques hackers use and how to guard against them. this article provides an overview of 15 common hacking types, real world examples of each, and tips to help you boost your cybersecurity. Explore the realm of ethical hacking, its tools, techniques used, dive into real life case studies, and the future of this security focused discipline. The most common hacking techniques include fake wap, bait and switch, credential reuse, browser locker, and sql injection. other common hacking methods may include phishing, session hijacking, and ddos attacks.

Top Hacking Techniques Explained For Beginners 2026 Guide Understanding the common ttps employed by hackers helps security professionals implement defensive measures. let’s take a closer look at some of the most frequently used tactics, techniques, and procedures in modern cyberattacks. As cyberattacks become more sophisticated, it‘s critical to understand the different hacking techniques hackers use and how to guard against them. this article provides an overview of 15 common hacking types, real world examples of each, and tips to help you boost your cybersecurity. Explore the realm of ethical hacking, its tools, techniques used, dive into real life case studies, and the future of this security focused discipline. The most common hacking techniques include fake wap, bait and switch, credential reuse, browser locker, and sql injection. other common hacking methods may include phishing, session hijacking, and ddos attacks.

Top Hacking Techniques Explained For Beginners 2026 Guide Explore the realm of ethical hacking, its tools, techniques used, dive into real life case studies, and the future of this security focused discipline. The most common hacking techniques include fake wap, bait and switch, credential reuse, browser locker, and sql injection. other common hacking methods may include phishing, session hijacking, and ddos attacks.
Top Hacking Techniques Explained For Beginners 2025 Guide
Comments are closed.