Command Injection Vulnerability In Create Mcp Server Stdio Tool Exposes

Mcp Vulnerability Case Study Sql Injection In The Postgres Mcp Server A critical command injection vulnerability in the create mcp server stdio's port monitoring tool allows attackers to execute arbitrary commands. learn how this system utility flaw threatens mcp server security. Prior to version 0.0.13, the mcp server is written in a way that is vulnerable to command injection vulnerability attacks as part of some of its mcp server tool definition and implementation.

Introduction To Command Injection Vulnerability Cve 2025 54994 @akoskm create mcp server stdio is vulnerable to mcp server command injection through `exec` api: user initiated and remote command injection on a running mcp server. An attacker provides specially crafted input containing shell metacharacters (;, |, &&, $ (), backticks) through mcp tool parameters. because the server concatenates this input directly into exec () calls, the injected commands execute with the server process's full privileges on the host system. As part of our security research in mcp, our application and threat intelligence (ati) team has uncovered an additional attack vector in mcp taxonomies command injection via mcp tool invocation which has limited attention so far. Description: litellm contains an authenticated remote command execution vulnerability in its mcp server creation functionality. the application allows users to add mcp servers via a json configuration specifying arbitrary command and args values.
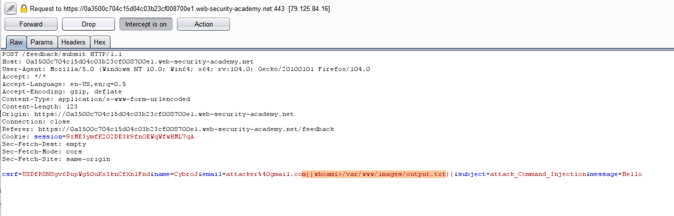
Introduction To Command Injection Vulnerability As part of our security research in mcp, our application and threat intelligence (ati) team has uncovered an additional attack vector in mcp taxonomies command injection via mcp tool invocation which has limited attention so far. Description: litellm contains an authenticated remote command execution vulnerability in its mcp server creation functionality. the application allows users to add mcp servers via a json configuration specifying arbitrary command and args values. The mcp server exposes the tool which app on port which relies on node.js child process api exec which is an unsafe and vulnerable api if concatenated with untrusted user input. Affected versions of this package are vulnerable to command injection via the which app on port tool, which executes exec on user input. an attacker can execute arbitrary commands on the host system by supplying specially crafted input containing shell metacharacters. The mcp server exposes the tool `which app on port` which relies on node.js child process api `exec` which is an unsafe and vulnerable api if concatenated with untrusted user input. version 0.0.13 contains a fix for the issue. The mcp server exposes the tool `which app on port` which relies on node.js child process api `exec` which is an unsafe and vulnerable api if concatenated with untrusted user input.

Introduction To Command Injection Vulnerability The mcp server exposes the tool which app on port which relies on node.js child process api exec which is an unsafe and vulnerable api if concatenated with untrusted user input. Affected versions of this package are vulnerable to command injection via the which app on port tool, which executes exec on user input. an attacker can execute arbitrary commands on the host system by supplying specially crafted input containing shell metacharacters. The mcp server exposes the tool `which app on port` which relies on node.js child process api `exec` which is an unsafe and vulnerable api if concatenated with untrusted user input. version 0.0.13 contains a fix for the issue. The mcp server exposes the tool `which app on port` which relies on node.js child process api `exec` which is an unsafe and vulnerable api if concatenated with untrusted user input.
Comments are closed.