Cloud Armor Gcp Networking
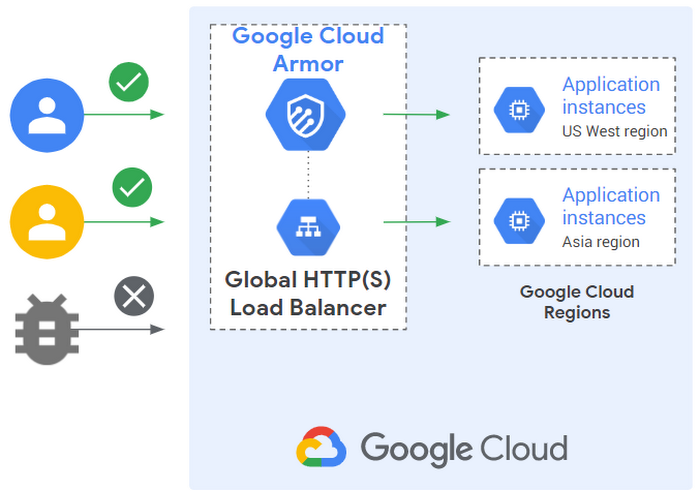
Google Cloud Networking In Depth Three Defense In Depth Principles For Google cloud armor is a network security service that provides defenses against ddos and application attacks, and offers a rich set of waf rules. Apply google cloud armor security policies to restrict access to cached objects on cloud cdn and cloud storage, and block the traffic before it reaches the load balanced backend services or buckets. mitigate some common vulnerabilities by using google cloud armor waf rules.
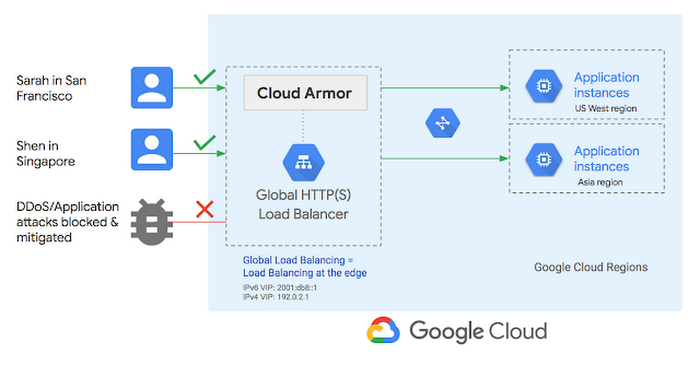
Getting To Know Cloud Armor Defense At Scale For Internet Facing Google cloud armor offers network layer protection for applications running on google cloud platform (gcp). it utilizes a range of powerful components to safeguard your applications from cyber threats and ensure high availability and performance. In this guide, we explore how to integrate google cloud armor and private service connect (psc) to create a unified, high reliability architecture that removes reliance on public ips and. Cloud armor provides always on protection from l3 and l4 volumetric and network protocol based ddos attacks, with automated inline mitigations in real time and with no latency impact. this. In a nutshell, gcp networking security tools like firewall rules, vpc service controls, and cloud armor are indispensable for creating a robust cloud security posture.
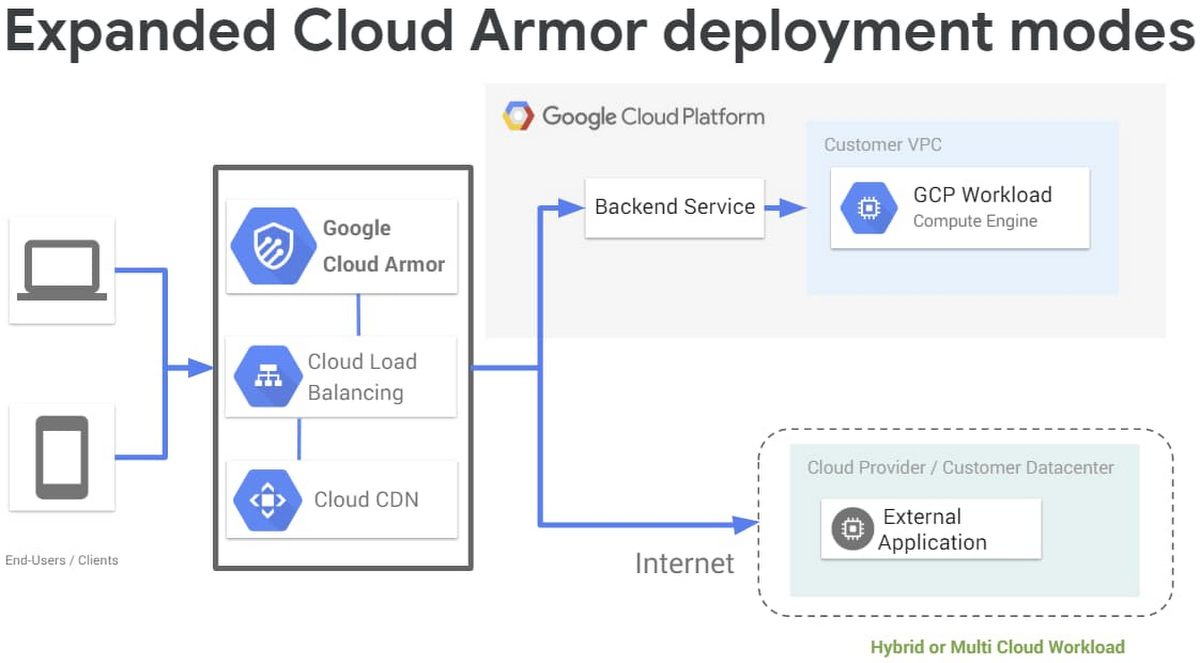
Cloud Armor Waf Web Application Firewall Protection For Workloads On Cloud armor provides always on protection from l3 and l4 volumetric and network protocol based ddos attacks, with automated inline mitigations in real time and with no latency impact. this. In a nutshell, gcp networking security tools like firewall rules, vpc service controls, and cloud armor are indispensable for creating a robust cloud security posture. Complete guide to setting up google cloud armor for web application security. covers waf policies, owasp top 10 protection, rate limiting, adaptive protection, and ddos mitigation for applications behind load balancers. Google cloud armor is google cloud’s managed edge application security service in the networking stack that protects internet facing apps behind supported load balancers and cdn configurations. Cloud armor works in the edge of gcp cloud, so applying security policies to lb backend prevents unauthorized traffic from entering vpc. Network architecture, waf policy design, ddos mitigation, bot management, and compliance validation. this article documents every decision, every trade off, and every lesson learned. the goal is.
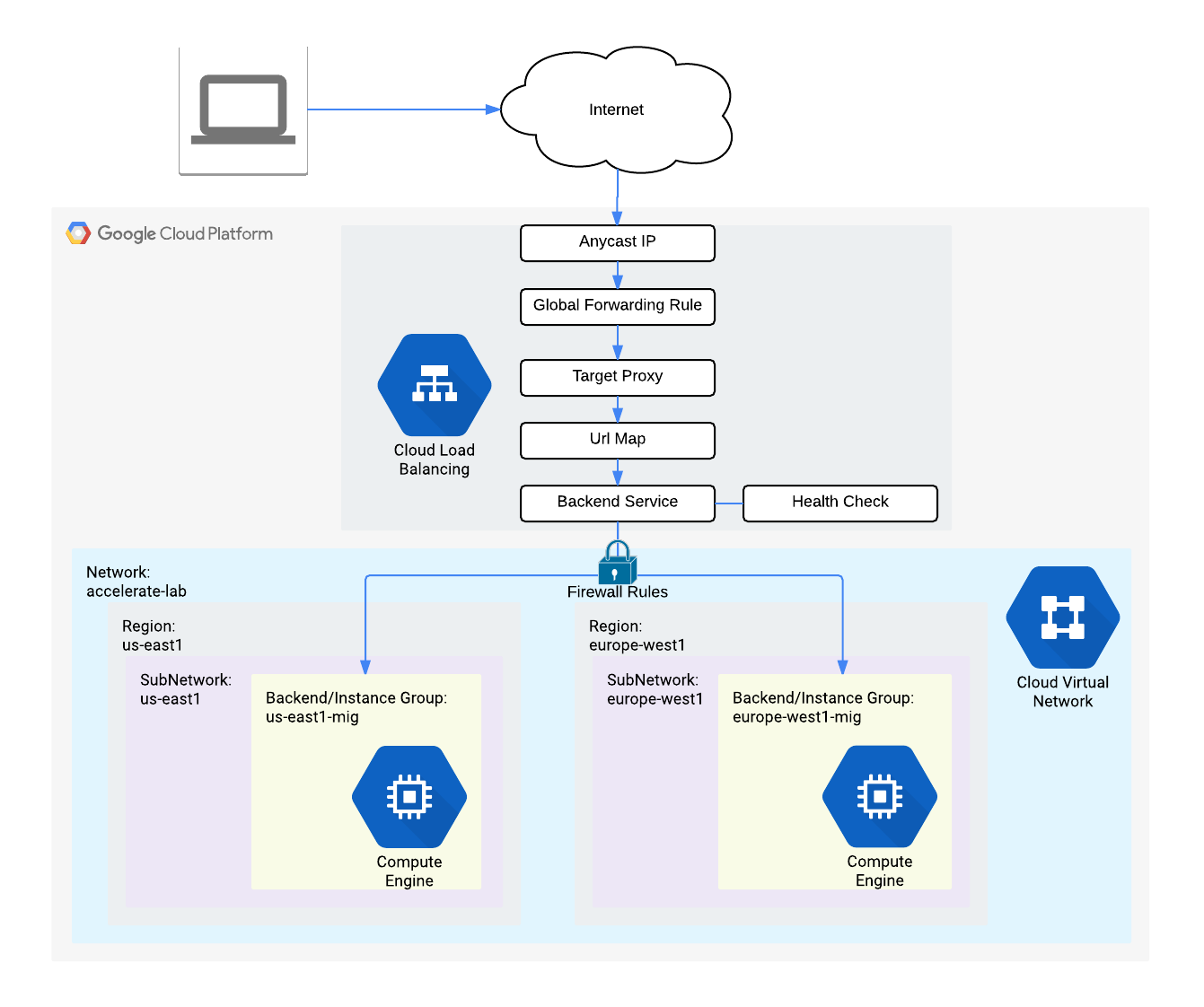
Rate Limiting With Cloud Armor Google Skills Complete guide to setting up google cloud armor for web application security. covers waf policies, owasp top 10 protection, rate limiting, adaptive protection, and ddos mitigation for applications behind load balancers. Google cloud armor is google cloud’s managed edge application security service in the networking stack that protects internet facing apps behind supported load balancers and cdn configurations. Cloud armor works in the edge of gcp cloud, so applying security policies to lb backend prevents unauthorized traffic from entering vpc. Network architecture, waf policy design, ddos mitigation, bot management, and compliance validation. this article documents every decision, every trade off, and every lesson learned. the goal is.
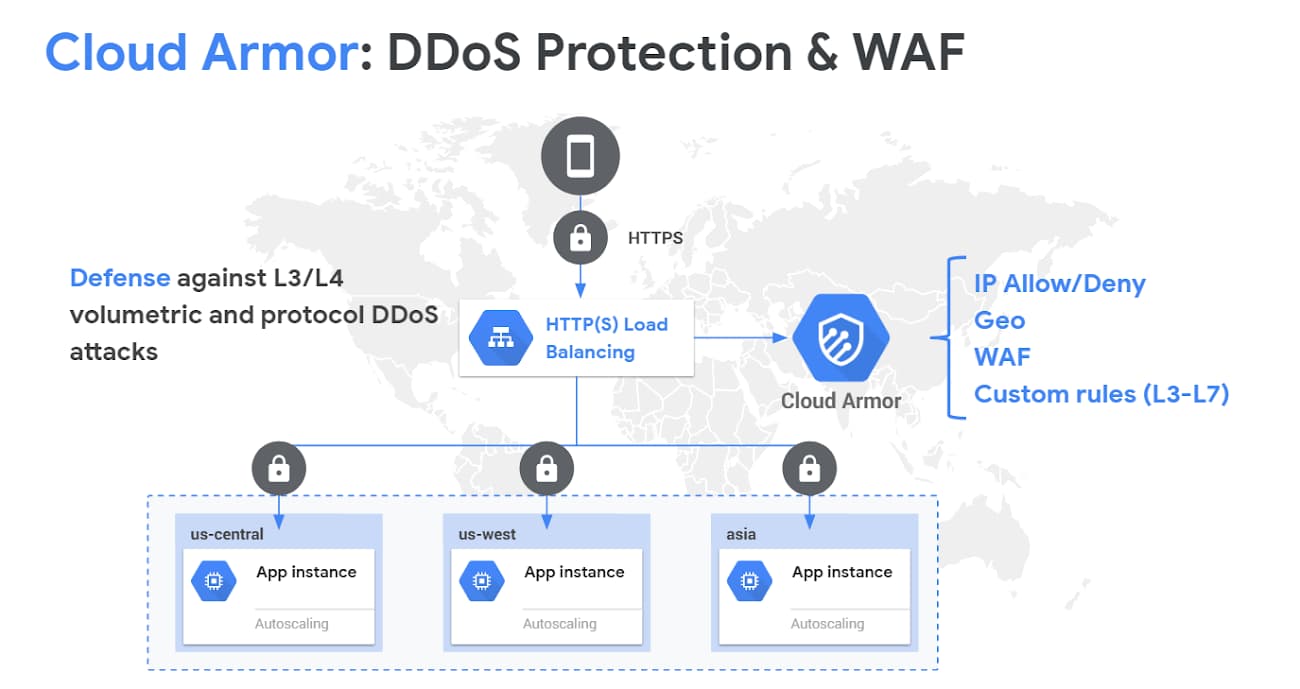
Google Cloud Armor Cloud armor works in the edge of gcp cloud, so applying security policies to lb backend prevents unauthorized traffic from entering vpc. Network architecture, waf policy design, ddos mitigation, bot management, and compliance validation. this article documents every decision, every trade off, and every lesson learned. the goal is.
Comments are closed.