Ccna Security Chapter 2 Lecture

Ccna Security Chapter 2 Exam V2 Ccna Exam 2016 Pdf Cisco Network security involves protocols, technologies, devices, tools, and techniques to secure data and mitigate …. The document covers various aspects of network security, specifically focusing on authentication, authorization, and accounting (aaa) processes essential for effective network management.

Ccna Security Chapter 2 Securing Network Devices Pdf Computer Ccna security chapter 2 lecture 3.9k views 13 years ago. This is my repository of my personal notes taken during jeremy's it lab complete ccna 200 300 course. each "day" is broken down into individual chapters. jeremy's it lab complete course for the ccna 200 300. i've also created a separate custom playlist of just the course labs for easy access. Access ccna lectures and study materials on google drive for networking certification preparation. Ccna security chapter 2 free download as pdf file (.pdf) or view presentation slides online. this the second chapter of ccna security.

Ccna2 Chapter1 Pdf Routing Router Computing Access ccna lectures and study materials on google drive for networking certification preparation. Ccna security chapter 2 free download as pdf file (.pdf) or view presentation slides online. this the second chapter of ccna security. Secure shell (ssh) is a protocol that provides a secure (encrypted), command line based connection to a remote device. ssh is commonly used in unix based systems. the cisco ios software also supports ssh. In the ccna course of study, students learn to configure both devices that connect to the network (end devices such as pcs) and devices that connect networks together (intermediary devices like routers and switches). This document provides an overview of securing network devices by configuring router hardening, secure administrative access, and network monitoring techniques. Welcome to the second lecture in the ccna security v2.0 netacad course. we cover chapter 2 today.i will add more notes here closer to premier.if this video w.

Ccna Security V2 0 Chapter 2 Test Online Download Free Pdf Cisco Secure shell (ssh) is a protocol that provides a secure (encrypted), command line based connection to a remote device. ssh is commonly used in unix based systems. the cisco ios software also supports ssh. In the ccna course of study, students learn to configure both devices that connect to the network (end devices such as pcs) and devices that connect networks together (intermediary devices like routers and switches). This document provides an overview of securing network devices by configuring router hardening, secure administrative access, and network monitoring techniques. Welcome to the second lecture in the ccna security v2.0 netacad course. we cover chapter 2 today.i will add more notes here closer to premier.if this video w.

Ccna Security Chapter Two Securing Network Devices Pdf Secure This document provides an overview of securing network devices by configuring router hardening, secure administrative access, and network monitoring techniques. Welcome to the second lecture in the ccna security v2.0 netacad course. we cover chapter 2 today.i will add more notes here closer to premier.if this video w.
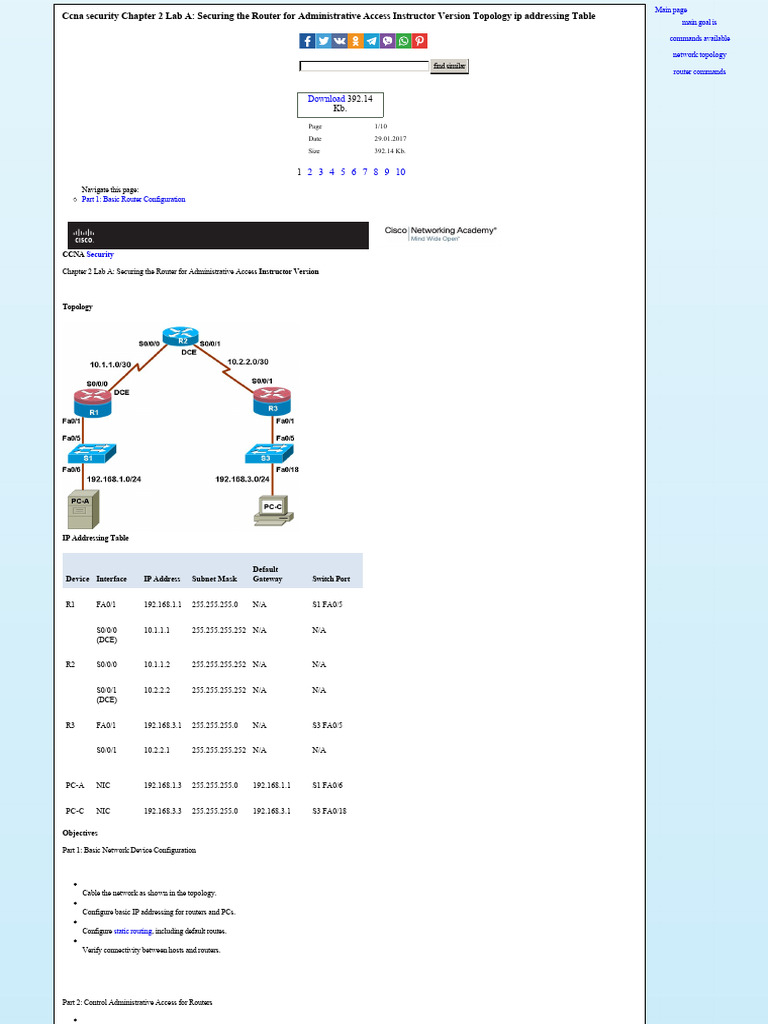
Ccna Security Chapter 2 Lab A Securing The Router For Administrative
Comments are closed.