Building Trust With Iot Security Steps To Implement Network
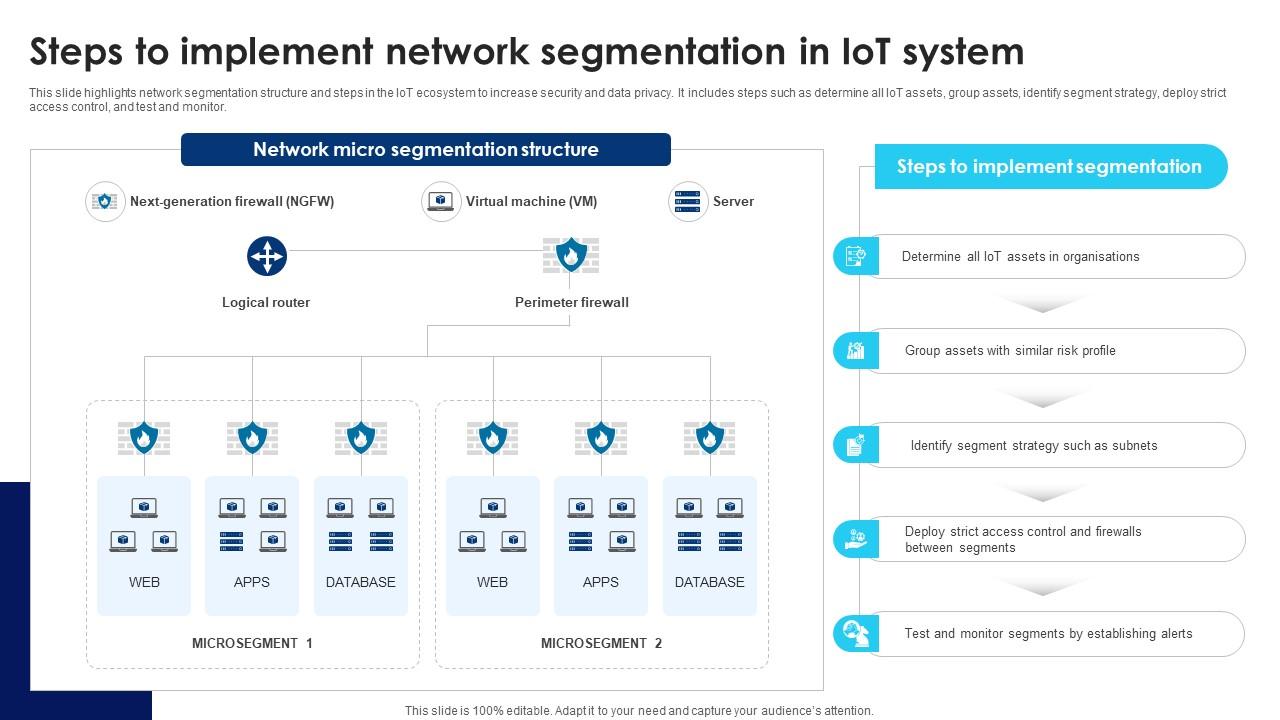
Building Trust With Iot Security Steps To Implement Network Device identities, rooted in silicon’s rot, are the foundation of iot security. from chip to network, they establish trust, verify authenticity, and enable resilience. This slide highlights network segmentation structure and steps in the iot ecosystem to increase security and data privacy. it includes steps such as determine all iot assets, group assets, identify segment strategy, deploy strict access control, and test and monitor.
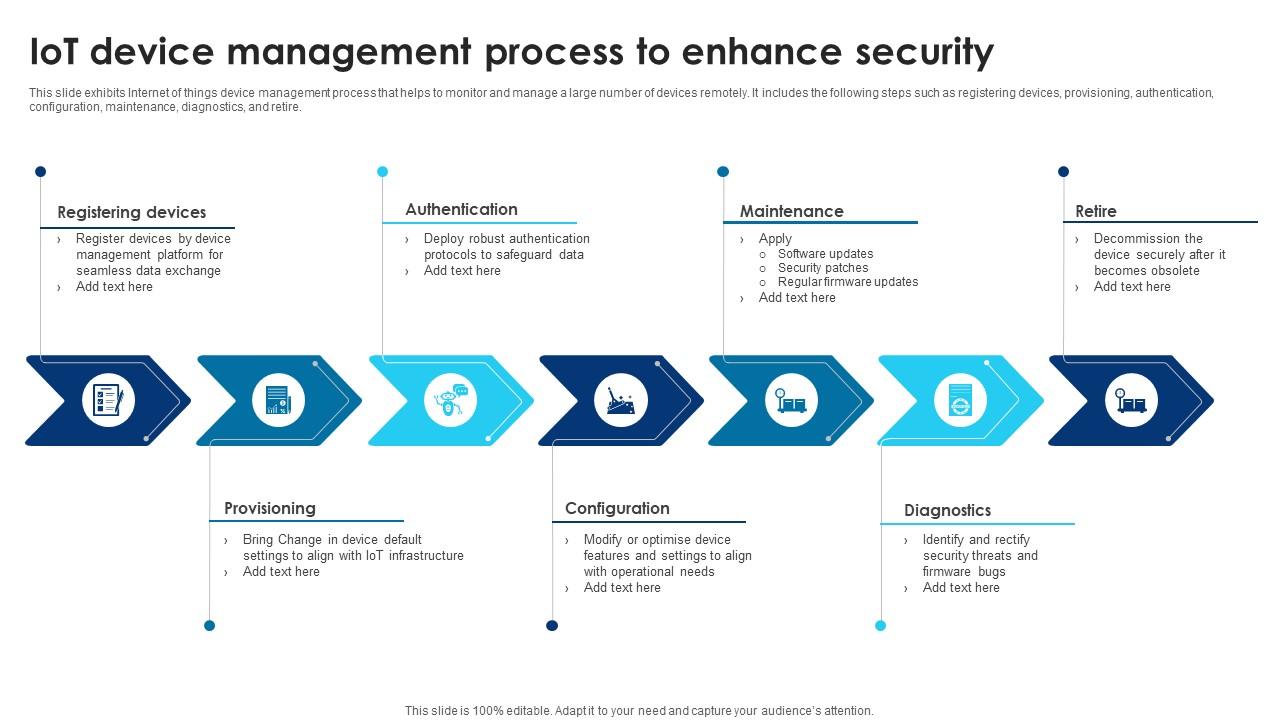
Building Trust With Iot Security Iot Device Management Process To Enhance S This document provides an overview of trusted internet of things (iot) device network layer onboarding—a capability for securely providing iot devices with their local network credentials in a manner that helps to ensure that the network is not put at risk as new iot devices are connected to it. That’s why security and trust must be at the foundation of every single iot deployment. in this q&a, we explore how thales helps protect the digital fabric of iot across industries – ensuring it remains reliable, resilient, and secure. Implementing network segmentation is the most impactful step you can take to secure your connected life. it shifts your security posture from reactive hope to proactive containment, directly applying the “protect” and “contain” functions of modern cybersecurity frameworks. Covering everything from device integrity to secure communications, these guidelines help organisations strengthen iot cybersecurity, reduce risk exposure, and build trust across the iot ecosystem.

Building Trust With Iot Security Overview Of Encryption Security Attacks In Implementing network segmentation is the most impactful step you can take to secure your connected life. it shifts your security posture from reactive hope to proactive containment, directly applying the “protect” and “contain” functions of modern cybersecurity frameworks. Covering everything from device integrity to secure communications, these guidelines help organisations strengthen iot cybersecurity, reduce risk exposure, and build trust across the iot ecosystem. Hence, this survey includes a discussion about security and privacy challenges as well as available solutions for iot based wireless sensor networks. this systematic literature review (slr) focuses particularly on a popular and applicable security approach known as trust management system (tms). One of the most promising approaches to protecting iot systems is the implementation of zero trust security solutions. in this article, we will discuss the advantages of using zero trust in iot and the key considerations you need to know to apply these principles to your systems. The result of the partnership between u blox and kudelski is an end to end security process that helps users design, test, and implement a security architecture that prepares iot devices for the diverse and constantly evolving threats they will face once deployed. The implementation of zero trust for iot requires integration with existing network infrastructure, security tools, and operational processes while maintaining compatibility with diverse device types and communication protocols.

Building Trust With Iot Security Iot Ecosystem Gateway Security Challenges Hence, this survey includes a discussion about security and privacy challenges as well as available solutions for iot based wireless sensor networks. this systematic literature review (slr) focuses particularly on a popular and applicable security approach known as trust management system (tms). One of the most promising approaches to protecting iot systems is the implementation of zero trust security solutions. in this article, we will discuss the advantages of using zero trust in iot and the key considerations you need to know to apply these principles to your systems. The result of the partnership between u blox and kudelski is an end to end security process that helps users design, test, and implement a security architecture that prepares iot devices for the diverse and constantly evolving threats they will face once deployed. The implementation of zero trust for iot requires integration with existing network infrastructure, security tools, and operational processes while maintaining compatibility with diverse device types and communication protocols.

Building Trust With Iot Security Understanding Physical Security Attacks In The result of the partnership between u blox and kudelski is an end to end security process that helps users design, test, and implement a security architecture that prepares iot devices for the diverse and constantly evolving threats they will face once deployed. The implementation of zero trust for iot requires integration with existing network infrastructure, security tools, and operational processes while maintaining compatibility with diverse device types and communication protocols.
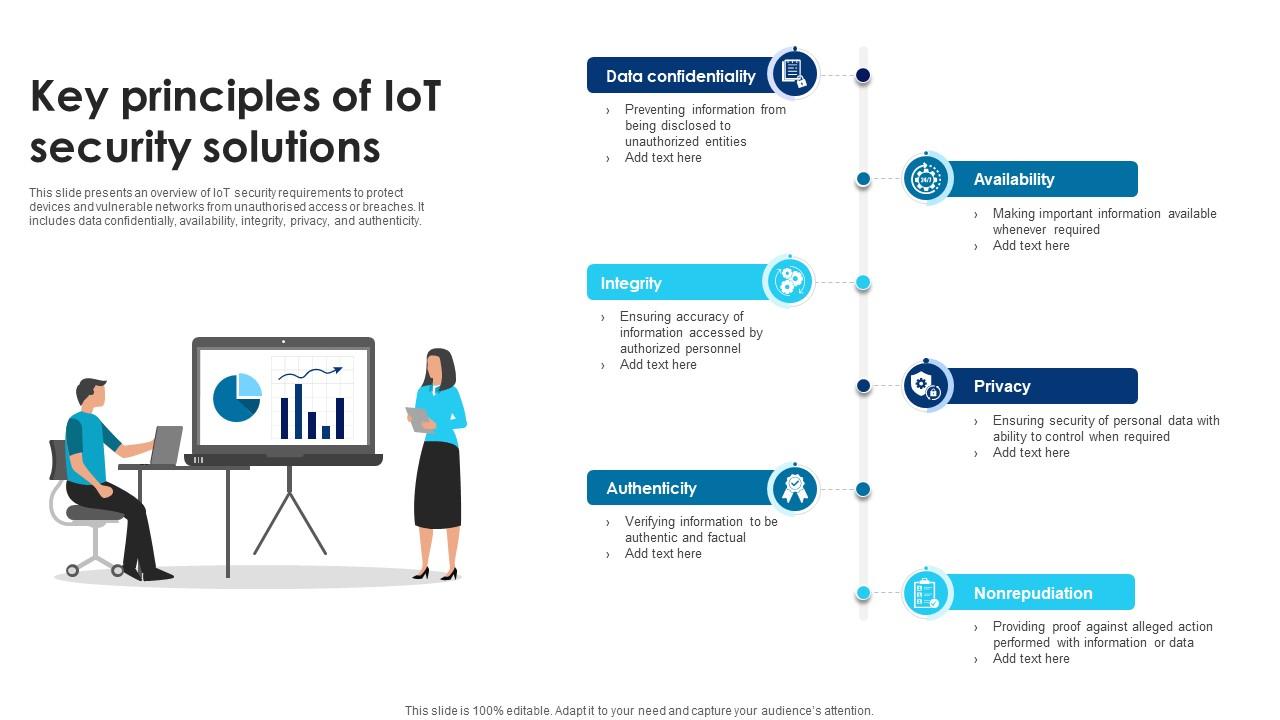
Building Trust With Iot Security Key Principles Of Iot Security
Comments are closed.