Building A Memory Layout Part 1

Memory Layout Pdf Enjoy the videos and music you love, upload original content, and share it all with friends, family, and the world on . Understand drc & lvs reports before exploring post layout parasitic extraction. 💬 let’s make memory layout simple and practical for every vlsi learner!.
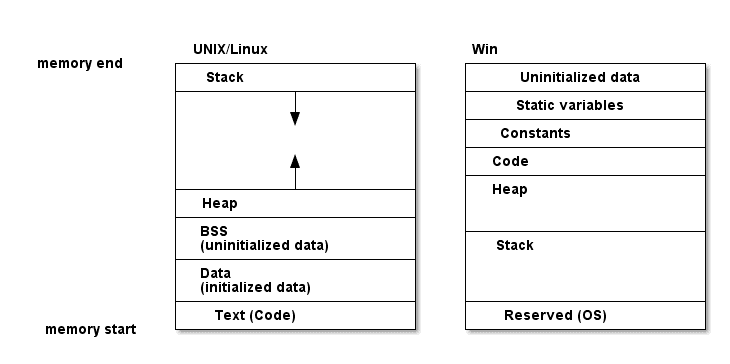
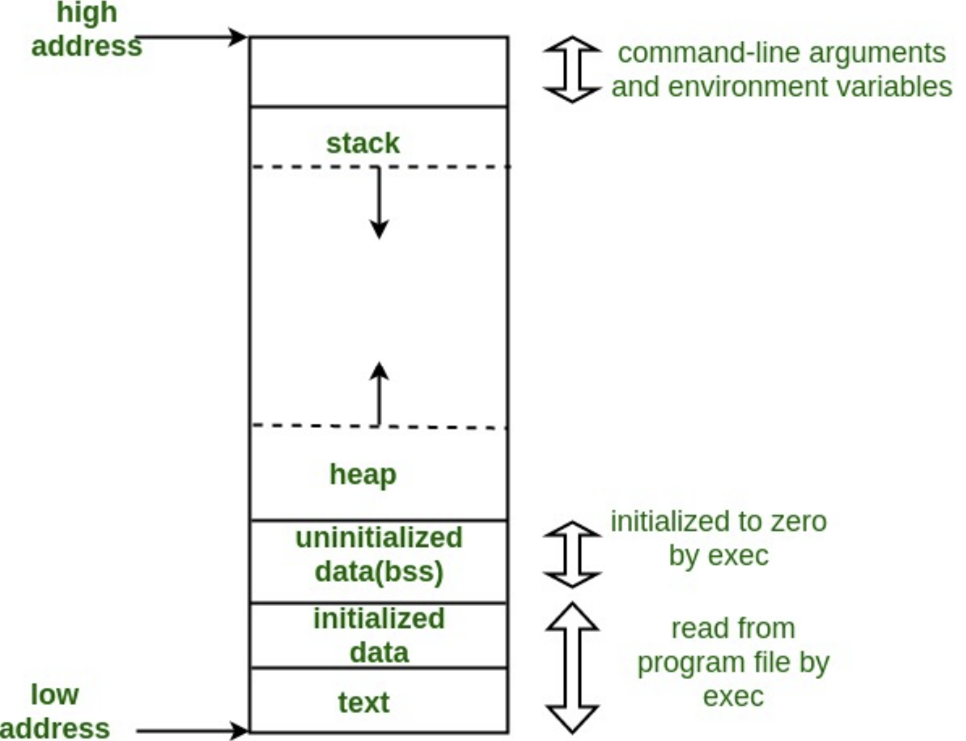
Memory Layout Semiconductor memory classification, memory timing: definitions, memory architecture, array structured memory architecture, hierarchical memory architecture, 6t sram, 3 transistor dram cell, 1 transistor dram cell, read only memory, programming the rom, programming the rom, fuse (prom). This post explores the journey from c source code to flash memory, covering memory sections (.text, .data, .bss), memory layout, and how linker scripts orchestrate the entire process on arm cortex m microcontrollers. Consider example of nxp s32k144 linker file as an example. there are two commands generally used in linker script, those are memory and section. When developing embedded firmware, it’s not enough to just write working code — you must also understand where your code and data live in memory. a solid grasp of the embedded memory layout.

Memory Layout Diagram Quizlet Consider example of nxp s32k144 linker file as an example. there are two commands generally used in linker script, those are memory and section. When developing embedded firmware, it’s not enough to just write working code — you must also understand where your code and data live in memory. a solid grasp of the embedded memory layout. The use of the points container object has the benefit of a convenient c object orientated interface, while supporting a vectorisation friendly struct of arrays data layout in memory (as seen in the diagram below). Memory organization is essential for efficient data processing and storage. the memory hierarchy ensures quick access to data by the cpu, while larger, slower storage devices hold data for the long term. The memory layout diagram tool is intended to produce graphical diagrams of the layout of memory regions in a system. these are most useful in describing retro systems, or systems which have fixed logical memory maps. While ddr4 design must be guided by rules and strategies to produce an optimized layout which minimizes emi issues and synchronizes signals, it is important that these good design practices are followed with a comprehensive analysis to verify proper functionality.
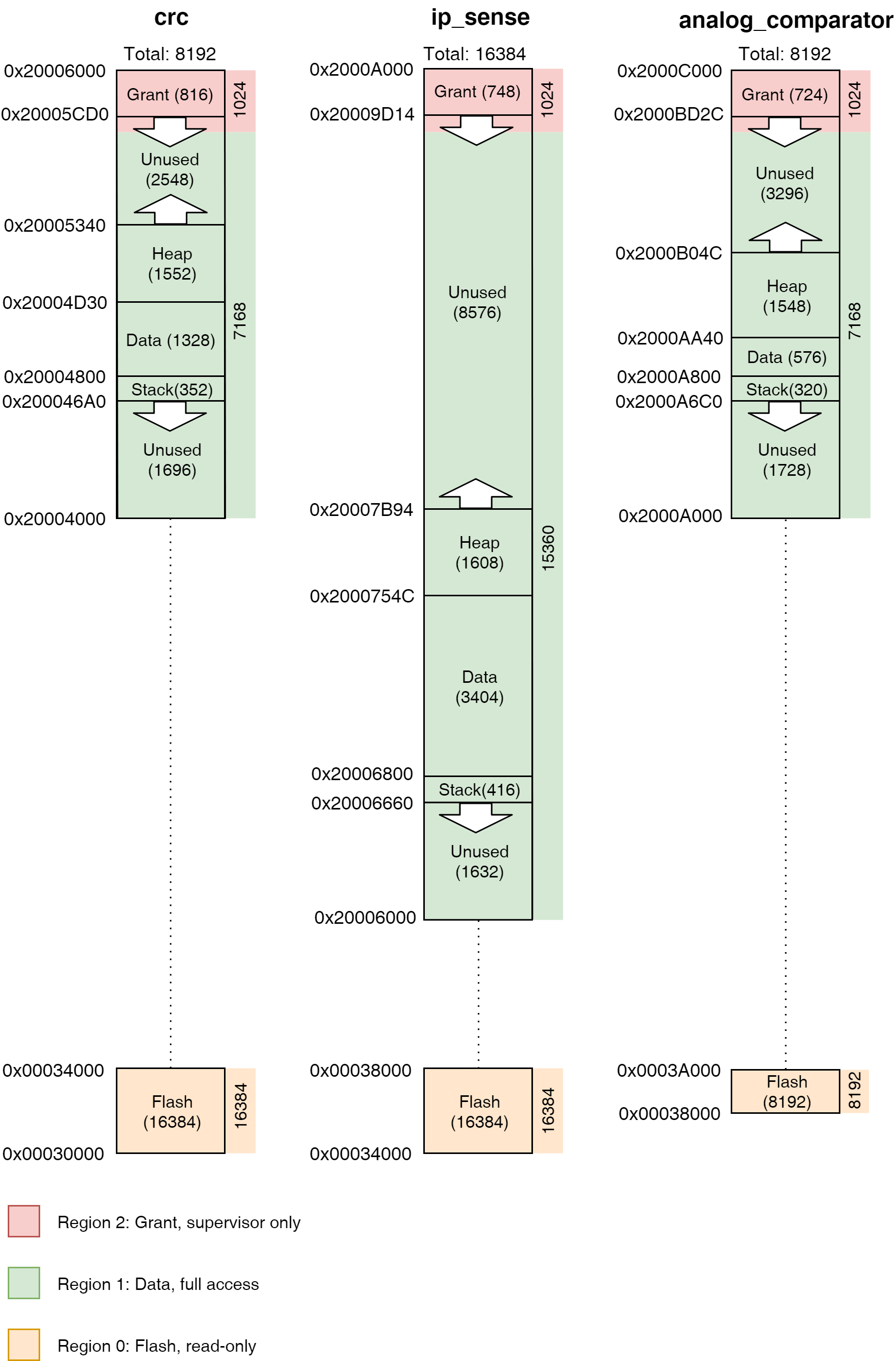
Memory Layout The Tock Book The use of the points container object has the benefit of a convenient c object orientated interface, while supporting a vectorisation friendly struct of arrays data layout in memory (as seen in the diagram below). Memory organization is essential for efficient data processing and storage. the memory hierarchy ensures quick access to data by the cpu, while larger, slower storage devices hold data for the long term. The memory layout diagram tool is intended to produce graphical diagrams of the layout of memory regions in a system. these are most useful in describing retro systems, or systems which have fixed logical memory maps. While ddr4 design must be guided by rules and strategies to produce an optimized layout which minimizes emi issues and synchronizes signals, it is important that these good design practices are followed with a comprehensive analysis to verify proper functionality.
Github Kevin 23100211 Memory Layout Design The memory layout diagram tool is intended to produce graphical diagrams of the layout of memory regions in a system. these are most useful in describing retro systems, or systems which have fixed logical memory maps. While ddr4 design must be guided by rules and strategies to produce an optimized layout which minimizes emi issues and synchronizes signals, it is important that these good design practices are followed with a comprehensive analysis to verify proper functionality.
Security Blog
Comments are closed.