Bug Bounty Pdf Security Computer Security

Lab Manual On Bug Bounty Pdf Computer Security Security This paper provides a comprehensive analysis of bug bounty programs, exploring their evolution, mechanisms, benefits, challenges, and impact on cybersecurity practices. Bug bounty free download as pdf file (.pdf), text file (.txt) or read online for free. the document presents an overview of bug bounty programs, which reward security experts for identifying vulnerabilities in software.

Bug Bounty Pdf Security Computer Security A collection of pdf books about the modern web application security and bug bounty. Modern bug bounty programs now have the technology required to dynamically assess talent by using both traditional measures of trust and those that consider performance and behavior. Adobe has released a security update for adobe acrobat and reader for windows and macos. this update addresses a critical vulnerability. successful exploitation could lead to arbitrary code execution. adobe is aware of cve 2026 34621 being exploited in the wild. A bug bounty program is an initiative offered by organizations, including websites and software developers, to incentivize individuals for discovering and reporting bugs, especially security.

Bug Bounty And Web Security Testing Course 2025 Easy Learning Adobe has released a security update for adobe acrobat and reader for windows and macos. this update addresses a critical vulnerability. successful exploitation could lead to arbitrary code execution. adobe is aware of cve 2026 34621 being exploited in the wild. A bug bounty program is an initiative offered by organizations, including websites and software developers, to incentivize individuals for discovering and reporting bugs, especially security. Three years back when ola was hacked, compromising the data of millions of users, they created india’s first full fledged bug bounty program to encourage independent security researchers to help them create a safe platform. I work as a senior application security engineer at bugcrowd, the #1 crowdsourced cybersecurity platform. i did sometimes still do bug bounties in my free time. Leveraging the vdp platform, the department of homeland security (dhs) launched the hack dhs pilot event, a crowd sourced bug bounty that incentivized the researcher community to search for vulnerabilities in certain dhs systems. In this paper, we present a data driven study of the chromium and firefox vulnerability reward programs. first, we estimate the dificulty of discovering a vulnerability using the probability of rediscovery as a novel metric.

Bug Bounty Pdf Vulnerability Computing Computer Security Three years back when ola was hacked, compromising the data of millions of users, they created india’s first full fledged bug bounty program to encourage independent security researchers to help them create a safe platform. I work as a senior application security engineer at bugcrowd, the #1 crowdsourced cybersecurity platform. i did sometimes still do bug bounties in my free time. Leveraging the vdp platform, the department of homeland security (dhs) launched the hack dhs pilot event, a crowd sourced bug bounty that incentivized the researcher community to search for vulnerabilities in certain dhs systems. In this paper, we present a data driven study of the chromium and firefox vulnerability reward programs. first, we estimate the dificulty of discovering a vulnerability using the probability of rediscovery as a novel metric.

Bug Bounty Hunting Tips Pdf Security Computer Security Leveraging the vdp platform, the department of homeland security (dhs) launched the hack dhs pilot event, a crowd sourced bug bounty that incentivized the researcher community to search for vulnerabilities in certain dhs systems. In this paper, we present a data driven study of the chromium and firefox vulnerability reward programs. first, we estimate the dificulty of discovering a vulnerability using the probability of rediscovery as a novel metric.
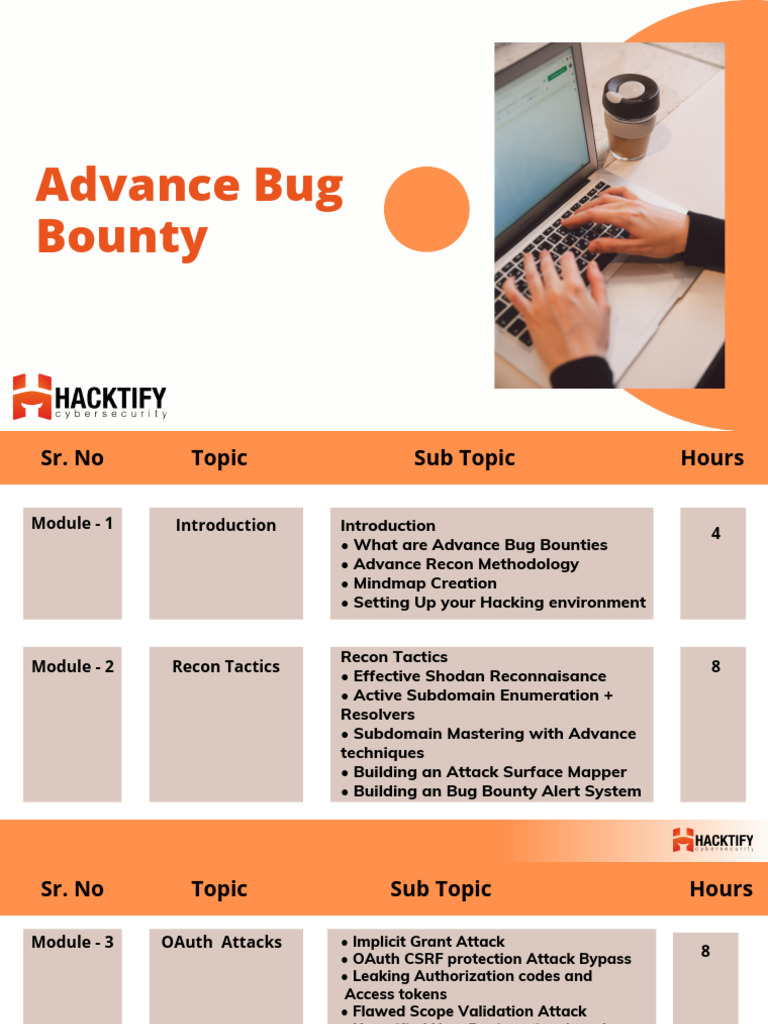
Advanced Bug Bounty Security Training Pdf Word Press Cyberspace
Comments are closed.