Blog Is Your Database Safe

Blog Is Your Database Safe In this article, we'll delve into the importance of database security in backend development and outline key practices to bolster database security, helping developers navigate the complexities of safeguarding data in the digital age. Your client database is too valuable to leave unprotected. by taking a few simple steps today—such as seeding your data and implementing better access controls—you can safeguard your business against insider threats and competitor misuse.

Database Security Threats Best Practices Tips Vulners Learn essential database security best practices, including continuous monitoring, network segmentation, and robust encryption to protect your critical data assets from evolving cyber threats. Safeguarding your database is compulsory due to the rise in cyber threats. by adhering to the best practices described in this blog, you can lower risks, stop data breaches, and maintain regulatory compliance. In this section we dive into safe notes and how they relate to protecting data across leading databases. you’ll learn practical, battle tested steps to keep database security tight, from encryption to best practice configurations. Comprehensive guide to database security covering access control, encryption, monitoring, and the critical blind spot of database change security. protect your data with proven strategies.

Database Security Threats Best Practices Tips Vulners In this section we dive into safe notes and how they relate to protecting data across leading databases. you’ll learn practical, battle tested steps to keep database security tight, from encryption to best practice configurations. Comprehensive guide to database security covering access control, encryption, monitoring, and the critical blind spot of database change security. protect your data with proven strategies. Discover top database security best practices to protect your data. learn key strategies and faqs for effective database security. Keeping your database safe is all about protecting important info from bad guys who want to steal or mess with it. it's like making sure your digital treasure chest is locked tight. here's a simple breakdown of what you need to know to keep things secure. common threats to your database. Effective database security measures are proactive rather than reactive. they involve assessing vulnerabilities, implementing controls like encryption and access restrictions, and continuously monitoring systems for potential threats. Learn six best practices and tips to ensure your databases are always safe from unauthorized access, data loss, corruption, or theft.
Locking Down Your Data Best Practices For Database Security Discover top database security best practices to protect your data. learn key strategies and faqs for effective database security. Keeping your database safe is all about protecting important info from bad guys who want to steal or mess with it. it's like making sure your digital treasure chest is locked tight. here's a simple breakdown of what you need to know to keep things secure. common threats to your database. Effective database security measures are proactive rather than reactive. they involve assessing vulnerabilities, implementing controls like encryption and access restrictions, and continuously monitoring systems for potential threats. Learn six best practices and tips to ensure your databases are always safe from unauthorized access, data loss, corruption, or theft.
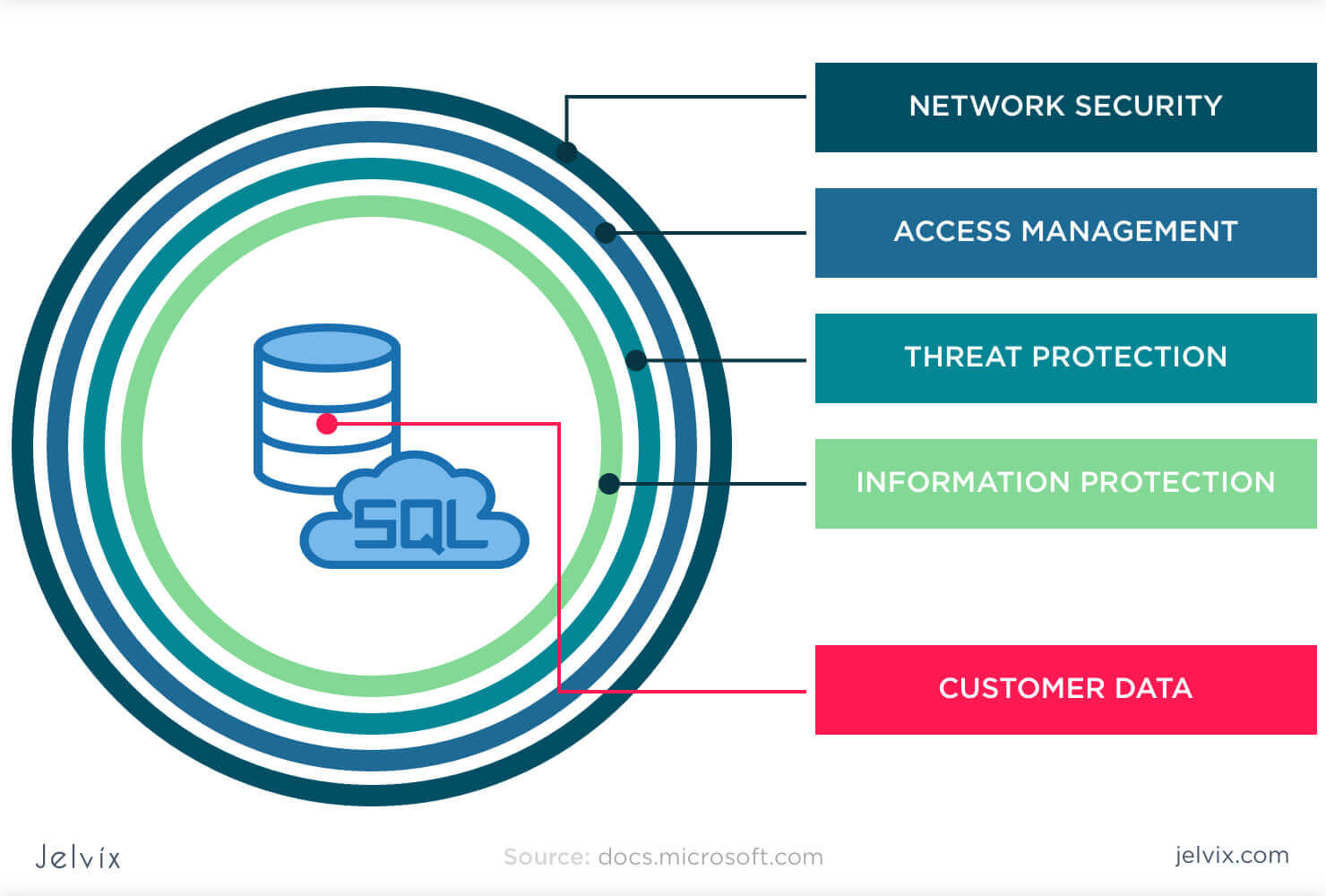
What Is Database Security Standards Threats Protection Effective database security measures are proactive rather than reactive. they involve assessing vulnerabilities, implementing controls like encryption and access restrictions, and continuously monitoring systems for potential threats. Learn six best practices and tips to ensure your databases are always safe from unauthorized access, data loss, corruption, or theft.
Comments are closed.