Block Malicious Data Attacks With Ibm Security Guardium And Ibm

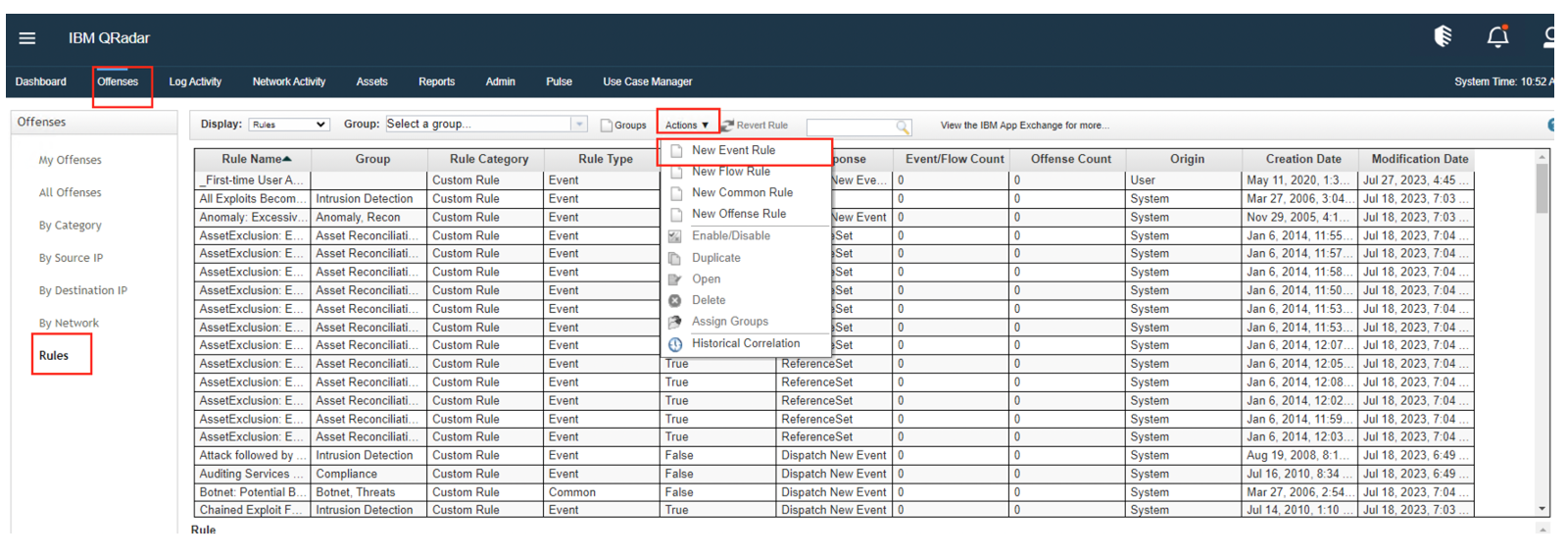
Block Malicious Data Attacks With Ibm Security Guardium And Ibm Block malicious data attacks with ibm security guardium and ibm security qradar monitor and remediate suspicious user activity by sudhagar tiroucamou, rahul k.p. on this page overview technologies products & services development practices. For cisos and security teams, the real challenge isn’t knowing these risks exist, but detecting and responding to them before data is compromised. this is where ibm guardium becomes a force.
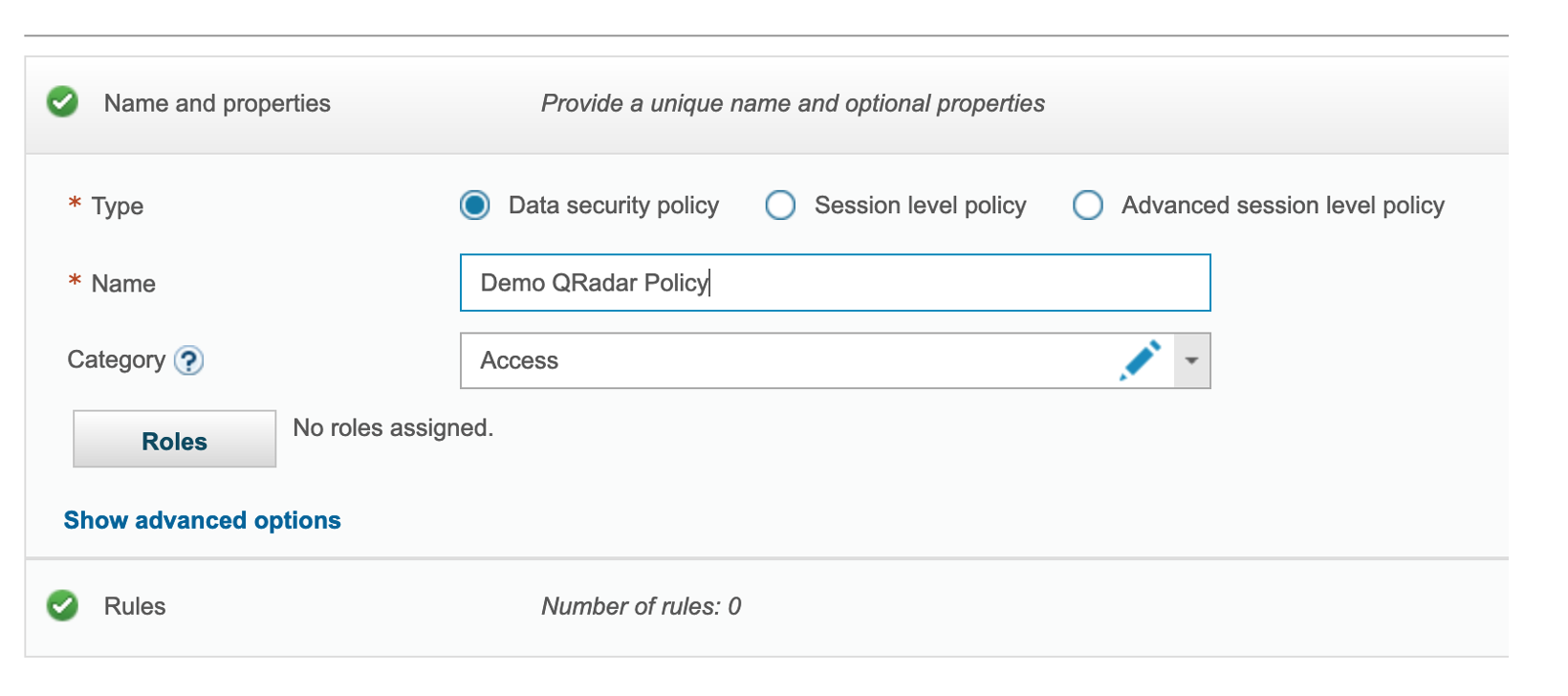
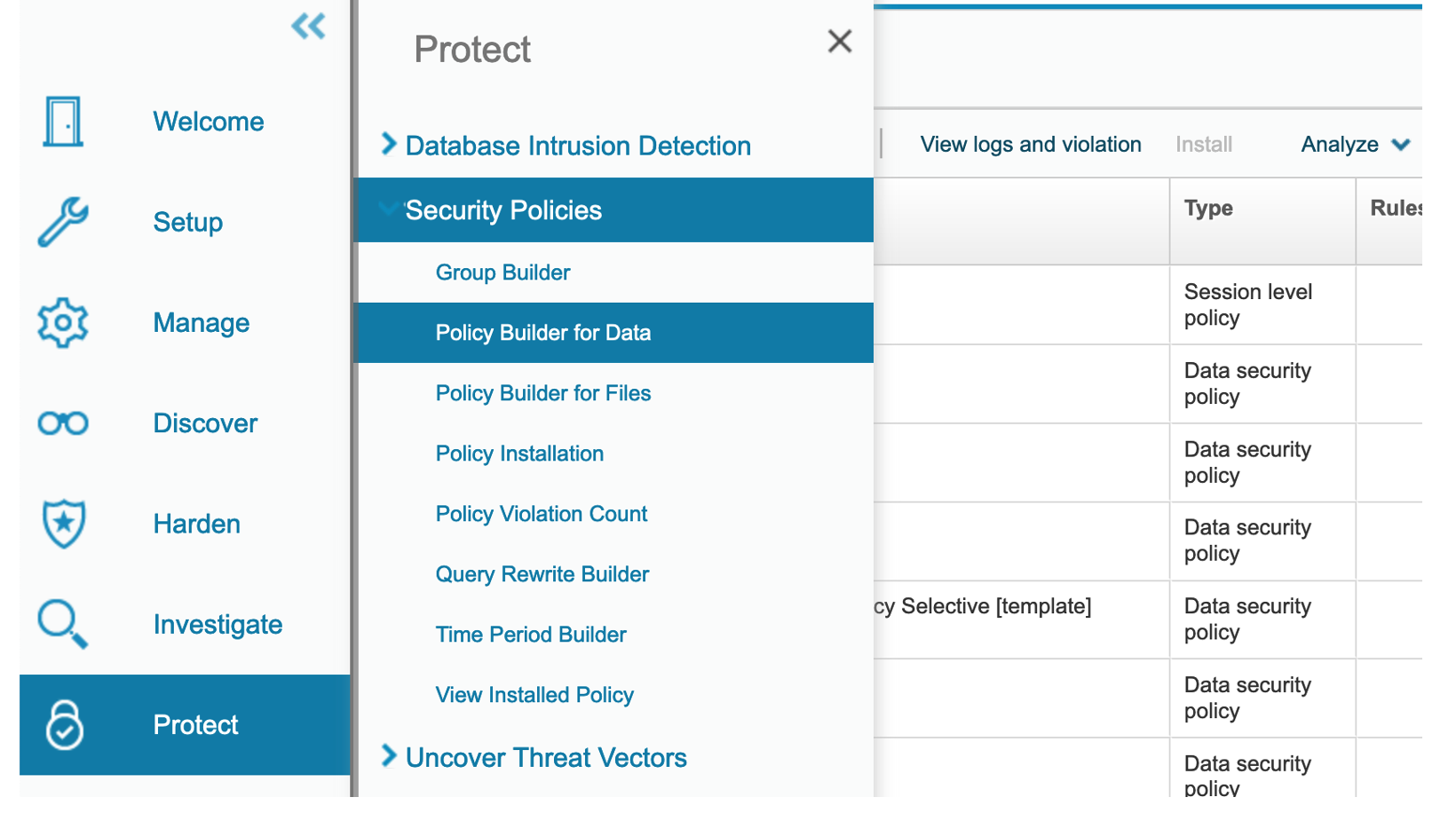
Ibm Security Guardium Data Protection Pdf Guardium data protection goes beyond monitoring to deliver automated, real time protection for sensitive information through dynamic masking, redaction, quarantining and blocking capabilities – automatically triggered by suspicious user behaviour or policy violations. Ibm guardium data protection unifies data security through real time monitoring, vulnerability scanning, and compliance automation. explore how it protects databases and detects insider threats. With guardium, your security teams can set entitlements and access controls, streamline compliance and get contextual insights and analytics to help detect and block suspicious activity. This platform provides an enriched understanding of risk to help security teams easily build and update data and user groups for closer monitoring and auditing; block or quarantine users or sessions for flagged suspicious activity; and remediate threats more quickly.

Data Security Ibm Security Guardium Data Protection Indrapr Pdf With guardium, your security teams can set entitlements and access controls, streamline compliance and get contextual insights and analytics to help detect and block suspicious activity. This platform provides an enriched understanding of risk to help security teams easily build and update data and user groups for closer monitoring and auditing; block or quarantine users or sessions for flagged suspicious activity; and remediate threats more quickly. By automating monitoring, vulnerability detection, and security analysis, ibm guardium allows it and security teams to focus on other strategic areas without compromising data protection. When potential threats are detected, organizations need to be able to instantly block or shut down a suspicious activity and open a case for deeper investigation. security analysts need to gain access to key insights that enable faster recovery and reduce the business impact. Highlights — monitor data activity from high value databases, data warehouses, mainframes, files, cloud and big data environments — automate the enforcement of data governance policies to protect sensitive data in originating data sources. Protect sensitive data across hybrid environments with ibm guardium. monitor, detect, and respond to data threats in real time.
Block Malicious Data Attacks With Ibm Security Guardium And Ibm By automating monitoring, vulnerability detection, and security analysis, ibm guardium allows it and security teams to focus on other strategic areas without compromising data protection. When potential threats are detected, organizations need to be able to instantly block or shut down a suspicious activity and open a case for deeper investigation. security analysts need to gain access to key insights that enable faster recovery and reduce the business impact. Highlights — monitor data activity from high value databases, data warehouses, mainframes, files, cloud and big data environments — automate the enforcement of data governance policies to protect sensitive data in originating data sources. Protect sensitive data across hybrid environments with ibm guardium. monitor, detect, and respond to data threats in real time.
Block Malicious Data Attacks With Ibm Security Guardium And Ibm Highlights — monitor data activity from high value databases, data warehouses, mainframes, files, cloud and big data environments — automate the enforcement of data governance policies to protect sensitive data in originating data sources. Protect sensitive data across hybrid environments with ibm guardium. monitor, detect, and respond to data threats in real time.
Block Malicious Data Attacks With Ibm Security Guardium And Ibm
Comments are closed.