Block Ciphers Ctf Handbook
Ctf Handbook Pdf Computer File Software Engineering A block cipher is an algorithm which is used in conjunction with a cryptosystem in order to package a message into evenly distributed 'blocks' which are encrypted one at a time. In this lesson, we’ll cover block ciphers and different block cipher modes. we’ll also take a look at some attacks against poorly implemented block ciphers. block ciphers will take in a message of a fixed length, your private key, and they produce a ciphertext of that length.

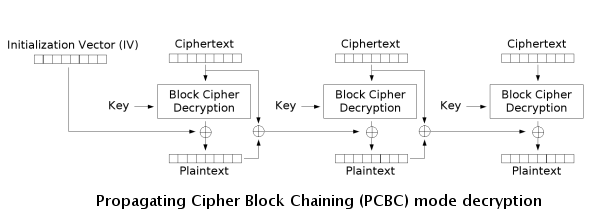
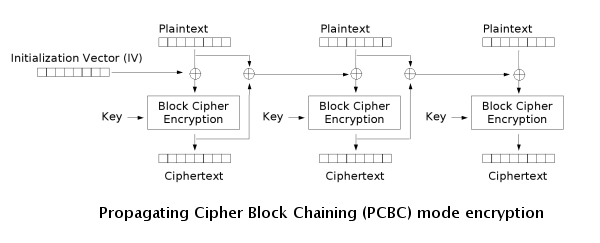
Introduction To Modern Block Ciphers Pdf Cipher Cryptography Choosing the s ‐boxes and p ‐box choosing the s ‐boxes and p ‐box at random would result in an insecure block cipher (key recovery aner ≈224 outputs) [bs’89] several rules used in choice of s and p boxes:. In this lesson, we'll cover block ciphers and different block cipher modes. we'll also take a look at some attacks against poorly implemented block ciphers. block ciphers will take in a message of a fixed length, your private key, and they produce a ciphertext of that length. A block cipher is an encryption algorithm that processes data in fixed size blocks (e.g., 128 bits) rather than one bit at a time. however, to encrypt data larger than a single block, different modes of operation are used to ensure both security and efficiency. Ctf handbook free download as pdf file (.pdf), text file (.txt) or read online for free.
Ciphers Ctf Support A block cipher is an encryption algorithm that processes data in fixed size blocks (e.g., 128 bits) rather than one bit at a time. however, to encrypt data larger than a single block, different modes of operation are used to ensure both security and efficiency. Ctf handbook free download as pdf file (.pdf), text file (.txt) or read online for free. The book offers beginners a reliable, systematic tutorial on ctf competition. at the same time, it includes real case studies and a wealth of our competition experience, making it a valuable asset for experienced ctf players. Get started with block cipher cryptography and discover the best practices for secure data encryption. learn about the different types of block ciphers, their strengths, and weaknesses. Ecb cbc wtf. 3. flipping cookie. 4. lazy cbc. This book introduces readers to traditional categories and new techniques of tasks related to capture the flag (ctf) cybersecurity competition.
Block Ciphers Ctf Handbook The book offers beginners a reliable, systematic tutorial on ctf competition. at the same time, it includes real case studies and a wealth of our competition experience, making it a valuable asset for experienced ctf players. Get started with block cipher cryptography and discover the best practices for secure data encryption. learn about the different types of block ciphers, their strengths, and weaknesses. Ecb cbc wtf. 3. flipping cookie. 4. lazy cbc. This book introduces readers to traditional categories and new techniques of tasks related to capture the flag (ctf) cybersecurity competition.
Block Ciphers Ctf Handbook Ecb cbc wtf. 3. flipping cookie. 4. lazy cbc. This book introduces readers to traditional categories and new techniques of tasks related to capture the flag (ctf) cybersecurity competition.
Block Ciphers Ctf Handbook
Comments are closed.