Bitcoin The Encryption Standard

301 Moved Permanently Bitcoin cryptography is the foundation of the whole bitcoin system, safeguarding wallets, transactions, and the blockchain itself. it employs a mix of digital signatures, public key cryptography, and hash functions to promote trust and security, all in the absence of central authorities. Sha 256 (secure hash algorithm 256 bit) is the cryptographic foundation that secures the bitcoin network, making transactions tamper proof. sha 256 secures not just the bitcoin network but also everyday it services such as amazon web services and app store downloads.

Encryption Archives Bitcoin News An explanation of the cryptography used in bitcoin (hash functions, digital signatures), how they work, and why they're used in bitcoin. Sha 256, or secure hash algorithm 256, is a hashing algorithm used to convert text of any length into a fixed size string of 256 bits (32 bytes). in this article, we explore exactly how does sha 256 work and why it was implemented on the bitcoin network. In creating bitcoin, satoshi nakamoto ingeniously blended several cryptographic technologies to forge a secure and functional digital currency network. two main cryptographic methods are central to bitcoin’s operations: sha 256 and ecdsa. Bitcoin is an open system by design. but when it comes to the private key storage (your access to your bitcoin) wallets use strong encryption like aes (advanced encryption standard) to protect that data. the encryption algorithm is used by the nsa for classified information.
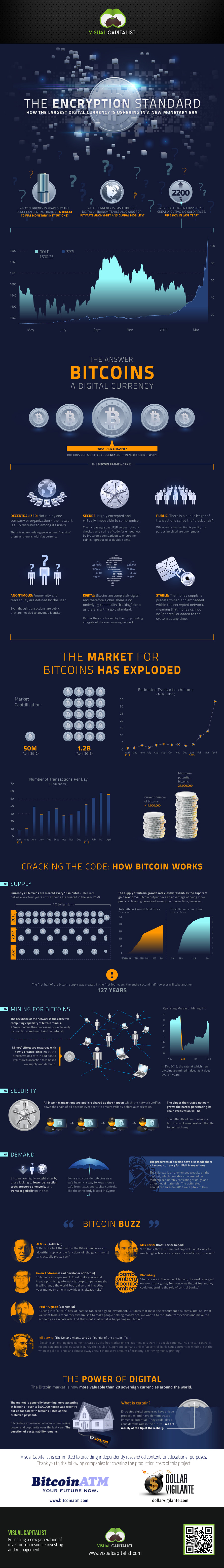
Bitcoin The Encryption Standard In creating bitcoin, satoshi nakamoto ingeniously blended several cryptographic technologies to forge a secure and functional digital currency network. two main cryptographic methods are central to bitcoin’s operations: sha 256 and ecdsa. Bitcoin is an open system by design. but when it comes to the private key storage (your access to your bitcoin) wallets use strong encryption like aes (advanced encryption standard) to protect that data. the encryption algorithm is used by the nsa for classified information. The cryptography behind bitcoin is a complex and multifaceted system that provides a robust security framework for the network. through the use of hash functions, digital signatures, and public key cryptography, bitcoin ensures the integrity and authenticity of transactions. Bitcoin headers use sha 256 to encrypt a variety of inputs and outputs. going further, bitcoin addresses are derived from public keys, which are in turn derived from private keys through an elliptic curve digital signature algorithm, or ecdsa. Ecdsa, the cryptographic cornerstone of bitcoin, ethereum, and other cryptocurrencies, has garnered significant attention following the announcement. bitcoin uses ecdsa for verifying digital signatures, ensuring the integrity of transactions. Bitcoin's $1.3 trillion security race: key initiatives aimed at quantum proofing the world's largest blockchain developers are considering ways to quantum proof the world's oldest cryptocurrency.

Bitcoin Encryption Generic Outline Color Icon The cryptography behind bitcoin is a complex and multifaceted system that provides a robust security framework for the network. through the use of hash functions, digital signatures, and public key cryptography, bitcoin ensures the integrity and authenticity of transactions. Bitcoin headers use sha 256 to encrypt a variety of inputs and outputs. going further, bitcoin addresses are derived from public keys, which are in turn derived from private keys through an elliptic curve digital signature algorithm, or ecdsa. Ecdsa, the cryptographic cornerstone of bitcoin, ethereum, and other cryptocurrencies, has garnered significant attention following the announcement. bitcoin uses ecdsa for verifying digital signatures, ensuring the integrity of transactions. Bitcoin's $1.3 trillion security race: key initiatives aimed at quantum proofing the world's largest blockchain developers are considering ways to quantum proof the world's oldest cryptocurrency.

Bitcoinwiki Ecdsa, the cryptographic cornerstone of bitcoin, ethereum, and other cryptocurrencies, has garnered significant attention following the announcement. bitcoin uses ecdsa for verifying digital signatures, ensuring the integrity of transactions. Bitcoin's $1.3 trillion security race: key initiatives aimed at quantum proofing the world's largest blockchain developers are considering ways to quantum proof the world's oldest cryptocurrency.
Comments are closed.