Bit Binary To Intermediate Cipher Text Download Table

Bit Cipher 1 Example Of Bit Cipher 2 Practical Stream Cipher 3 Pdf For network security, we shall implement stair case algorithm for generating intermediate cipher. in this paper; a novel approach for information security is introduced. This first set of resources is a full set of worksheets with teachers notes on a variety of ciphers. i developed these as part of an assignment whilst doing my pgce.

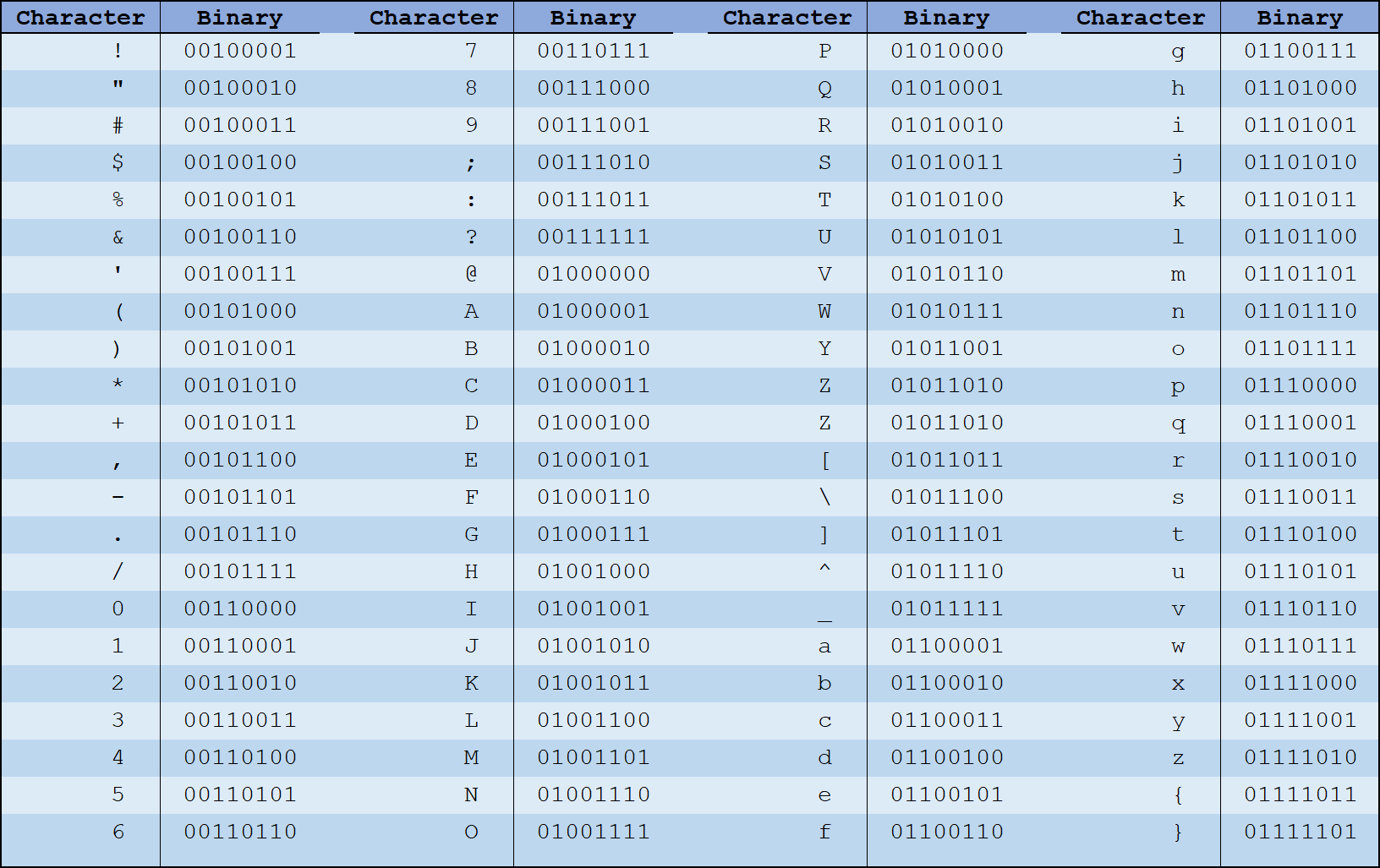
Bit Binary To Intermediate Cipher Text Download Table Computers store instructions, texts and characters as binary data. all unicode characters can be represented soly by utf 8 encoded ones and zeros (binary numbers). find out what your data looks like on the disk. To perform the reverse operation, convert each sequence of bits into a number, then associate that number with the corresponding character in the chosen encoding table. Free tools for solving ctfs, analyzing codes, cracking ciphers, finding hidden data, aiding in word games, and assisting with math — all processed locally in your browser. Key schedule: generates 48 bit subkeys for each of the 16 rounds. example key schedule for round 1: initial key: 00001111 00010101 01110001 11001100 10010100 01111001 10011111 pc 1 permutation: apply pc 1 to get 56 bit key.
Cyber Org Practice Ctf Free tools for solving ctfs, analyzing codes, cracking ciphers, finding hidden data, aiding in word games, and assisting with math — all processed locally in your browser. Key schedule: generates 48 bit subkeys for each of the 16 rounds. example key schedule for round 1: initial key: 00001111 00010101 01110001 11001100 10010100 01111001 10011111 pc 1 permutation: apply pc 1 to get 56 bit key. This is a page dedicated to simple text manipulation tools, which all can be replicated with just paper and pencil. if you know of another cipher that you think should be on here or a tool that would be useful, request it and perhaps it can be added to the site. Here's a handy reference table showing common characters, their ascii values, and binary representations. this is exactly what our converter uses behind the scenes!. In this example, the 1st bit of the plaintext is moved to the 58th position, the 2nd bit to the 50th position, and so on, following this table. the table continues for all 64 bits. Select an algorithm below to encode or decode messages or learn more about the supported algorithms. encode and decode text using common algorithms and substitution ciphers.

Binary To Various Conversions Pdf Binary Coded Decimal Computer This is a page dedicated to simple text manipulation tools, which all can be replicated with just paper and pencil. if you know of another cipher that you think should be on here or a tool that would be useful, request it and perhaps it can be added to the site. Here's a handy reference table showing common characters, their ascii values, and binary representations. this is exactly what our converter uses behind the scenes!. In this example, the 1st bit of the plaintext is moved to the 58th position, the 2nd bit to the 50th position, and so on, following this table. the table continues for all 64 bits. Select an algorithm below to encode or decode messages or learn more about the supported algorithms. encode and decode text using common algorithms and substitution ciphers.

8 Bit Binary To Final Cipher Text Download Table In this example, the 1st bit of the plaintext is moved to the 58th position, the 2nd bit to the 50th position, and so on, following this table. the table continues for all 64 bits. Select an algorithm below to encode or decode messages or learn more about the supported algorithms. encode and decode text using common algorithms and substitution ciphers.

8 Bit Binary To Final Cipher Text Download Table
Comments are closed.