Basic Malware Analysis Using Capavirustotal Pe Tree Malbuster
Basic Malware Analysis Using Capa Virustotal Pe Tree Malbuster This write up covers the malbuster challenge from tryhackme. the room focuses on static malware analysis and behavioral inspection through tools such as pe tree and capa. Hi, it is a beginner level malware analysis excercise. we are using petree & capa to gain idea about an unknown sample.
Tree Based Classifier Ensembles For Pe Malware Analysis A Performance This room aims to be a practice room for dissecting pe headers and static analysis 1. in this scenario, you will act as one of the reverse engineers that will analyse malware samples based on the detections reported by your soc team. Initially i used the virustotal behavior analysis but wanted a cleaner result so i ran capa on the sample directly. within the samples dir use the command capa malbuster 1.exe and observe the results. Based on virustotal detection, what is the malware signature of malbuster 2 according to avira? let's get the hash value for malbuster 2 first, then we can check avira detection in virustotal. In this scenario, you will act as one of the reverse engineers that will analyse malware samples based on the detections reported by your soc team. this room requires basic knowledge of malware static analysis. we recommend going through the following rooms before attempting this challenge.
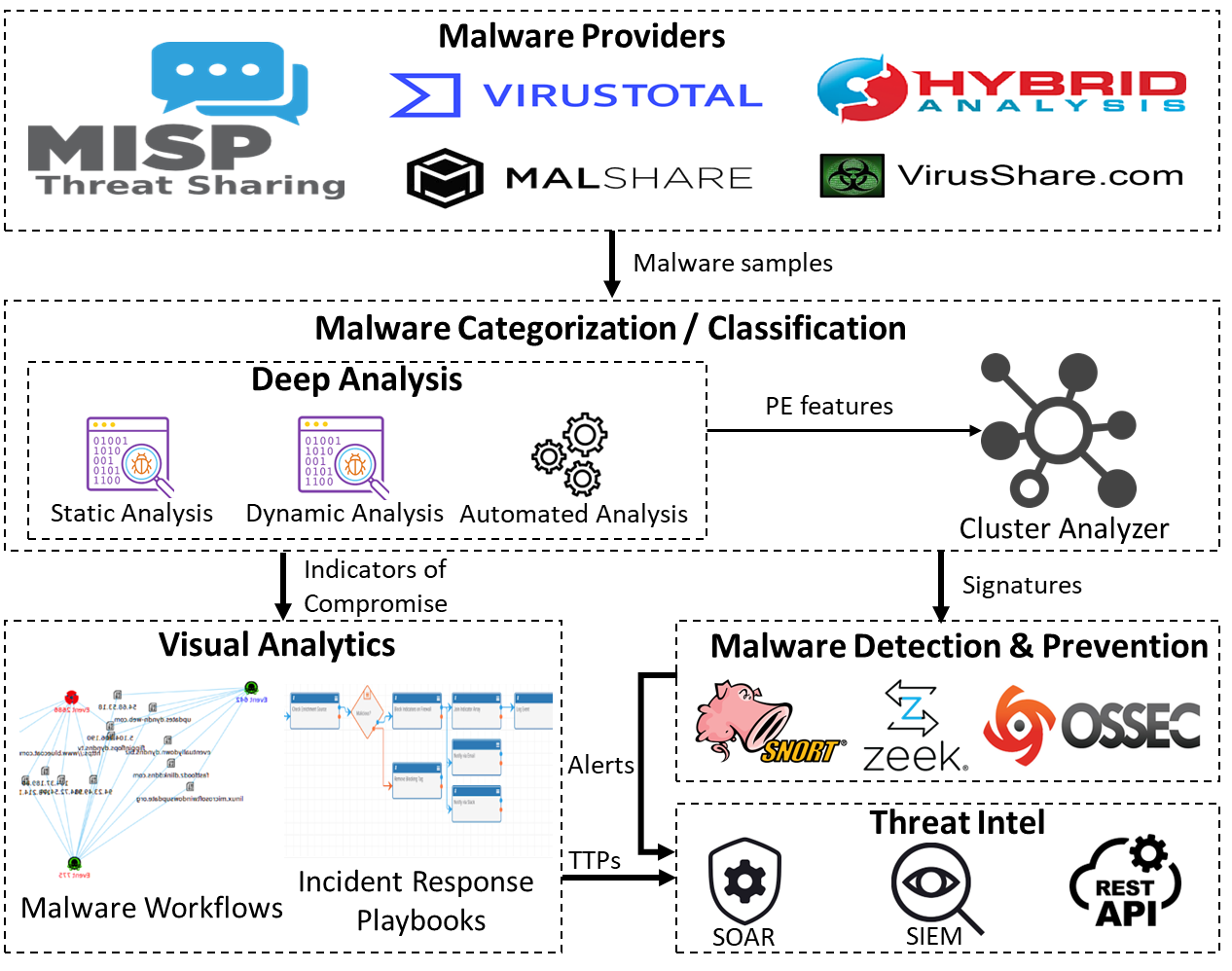
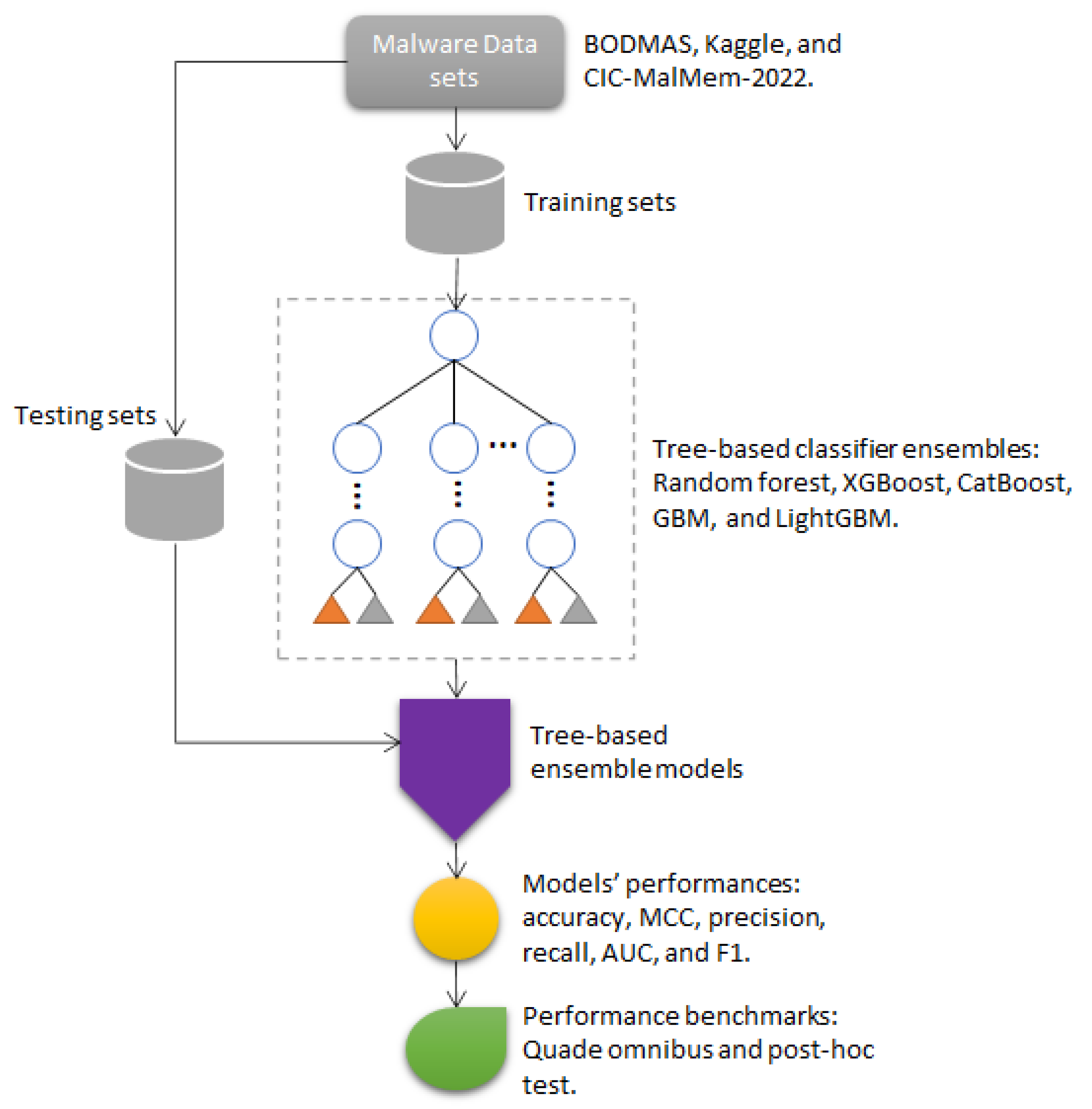
2211 01535 Reliable Malware Analysis And Detection Using Topology Based on virustotal detection, what is the malware signature of malbuster 2 according to avira? let's get the hash value for malbuster 2 first, then we can check avira detection in virustotal. In this scenario, you will act as one of the reverse engineers that will analyse malware samples based on the detections reported by your soc team. this room requires basic knowledge of malware static analysis. we recommend going through the following rooms before attempting this challenge. This details reverse engineering activities and answers for labs contained in the book ‘practical malware analysis’ by michael sikorski and andrew honig, which is published by no starch press. Based on virustotal detection, what is the malware signature of malbuster 2 according to avira? using the same method to get the hash value in the 2nd question, i then input that value in virustotal. Several tree based ensemble approaches are trained on three distinct pe malware training datasets in order to generate classification models. the performance of classification models is then determined by validating them on a testing dataset. In this module, we will embark on a journey to learn malware analysis from the basics to understanding the common techniques malware authors use. finally, we will learn about the tools that enable a malware analyst to gain a foothold in identifying what the malware authors are up to and defeat them.
Comments are closed.