Basic Hardware Key Devpost
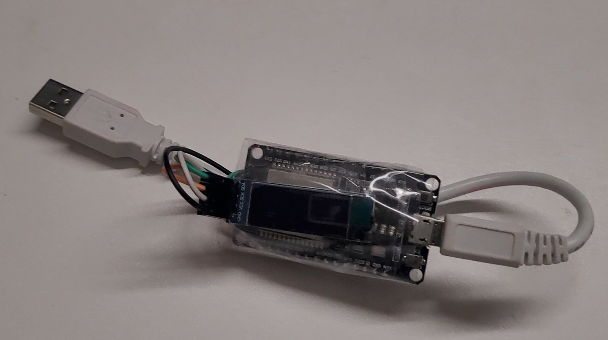
Basic Hardware Key Devpost Once hardware security keys become more popular, we may see a decrease in security breaches due to bad overused passwords. but for this to happen, hardware security keys must become affordable. A simple hardware key using an esp32.

Hardware Challenge Devpost Participate in online virtual and in person hackathons to build products, practice skills, learn technologies, win prizes, and grow your network. We learned that while newer methods like hardware security keys and passkeys offer better protection, they also have drawbacks in terms of widespread adoption, accessibility and device compatibility. A hardware security key contains a secure chip that uses encryption to verify your identity, whereas a usb simply stores files. modern security keys come in various formats, such as lightning and nfc, allowing them to work across different devices. Computer hardware refers to the physical components of a computer that you can see and touch. these components work together to process input and deliver output based on user instructions. in this article, we’ll explore the different types of computer hardware, their functions, and how they interact to make your computer work.

Devpost A hardware security key contains a secure chip that uses encryption to verify your identity, whereas a usb simply stores files. modern security keys come in various formats, such as lightning and nfc, allowing them to work across different devices. Computer hardware refers to the physical components of a computer that you can see and touch. these components work together to process input and deliver output based on user instructions. in this article, we’ll explore the different types of computer hardware, their functions, and how they interact to make your computer work. Essential guide to hardware security keys: what they are, why you need them, and how to choose the right one. In this article, we discuss what computer hardware is and the basic components of it along with how computer technicians can safely troubleshoot key parts of a personal computer. This page will give you all your hardware basics, what each part does, why it’s important, and how it effects your computer overall. the main components we’ll be covering are the following. A hardware security key is a small device often resembling a usb stick that acts as a physical form of authentication. it’s part of a cybersecurity method known as two factor authentication (2fa) or multi factor authentication (mfa).

Secure A Key Devpost Essential guide to hardware security keys: what they are, why you need them, and how to choose the right one. In this article, we discuss what computer hardware is and the basic components of it along with how computer technicians can safely troubleshoot key parts of a personal computer. This page will give you all your hardware basics, what each part does, why it’s important, and how it effects your computer overall. the main components we’ll be covering are the following. A hardware security key is a small device often resembling a usb stick that acts as a physical form of authentication. it’s part of a cybersecurity method known as two factor authentication (2fa) or multi factor authentication (mfa).

Devpost Blog This page will give you all your hardware basics, what each part does, why it’s important, and how it effects your computer overall. the main components we’ll be covering are the following. A hardware security key is a small device often resembling a usb stick that acts as a physical form of authentication. it’s part of a cybersecurity method known as two factor authentication (2fa) or multi factor authentication (mfa).
Comments are closed.