Aws Shared Responsibility Model Introduction To Devops Theclockend

The Aws Shared Responsibility Model Pdf Amazon Web Services Cloud Welcome to the world of the aws shared responsibility model and devops. in this guide, we’ll break down what aws is, how devops plays a crucial role, and why understanding the aws shared responsibility model is vital for your cloud security strategy. This shared model can help relieve the customer’s operational burden as aws operates, manages, and controls the components from the host operating system and virtualization layer down to the physical security of the facilities in which the service operates.

Aws Shared Responsibility Model Introduction To Devops Theclockend The shared responsibility model divides security duties between aws and you (the customer). aws is responsible for security of the cloud, while you are responsible for security in the cloud. Learn how aws ec2, virtualization, and the shared responsibility model work together in modern cloud architectures. Explore the shared responsibility model and its impact on cloud security posture, understanding how aws and customers divide security responsibilities. learn about compliance in the aws context and gain insights into identity and access management (iam). Aws global infrastructure & shared responsibility model | beginner guide in this video, we explore aws global infrastructure and the aws shared responsibility model, two core.

Shared Responsibility Model Amazon Web Services Aws Explore the shared responsibility model and its impact on cloud security posture, understanding how aws and customers divide security responsibilities. learn about compliance in the aws context and gain insights into identity and access management (iam). Aws global infrastructure & shared responsibility model | beginner guide in this video, we explore aws global infrastructure and the aws shared responsibility model, two core. This paper highlights aws capabilities that help you accelerate your devops journey, and how aws services can help remove the undifferentiated heavy lifting associated with devops adaptation. Shared responsibility security of the cloud security services in aws aws security frameworks how to prioritize evolutive path 1. assign security contacts select the regions & block the rest evaluate cloud security posture multi factor authentication. In cloud computing, aws follows the shared responsibility model. the responsibility here is shared between the customers to secure all their applications, data, and operations in the cloud and between aws for securing the cloud infrastructure. You are responsible for setting up and managing network controls, such as firewall rules, and for managing platform level identity and access management separately from iam.
What Is The Aws Shared Responsibility Model The Cloud Security This paper highlights aws capabilities that help you accelerate your devops journey, and how aws services can help remove the undifferentiated heavy lifting associated with devops adaptation. Shared responsibility security of the cloud security services in aws aws security frameworks how to prioritize evolutive path 1. assign security contacts select the regions & block the rest evaluate cloud security posture multi factor authentication. In cloud computing, aws follows the shared responsibility model. the responsibility here is shared between the customers to secure all their applications, data, and operations in the cloud and between aws for securing the cloud infrastructure. You are responsible for setting up and managing network controls, such as firewall rules, and for managing platform level identity and access management separately from iam.
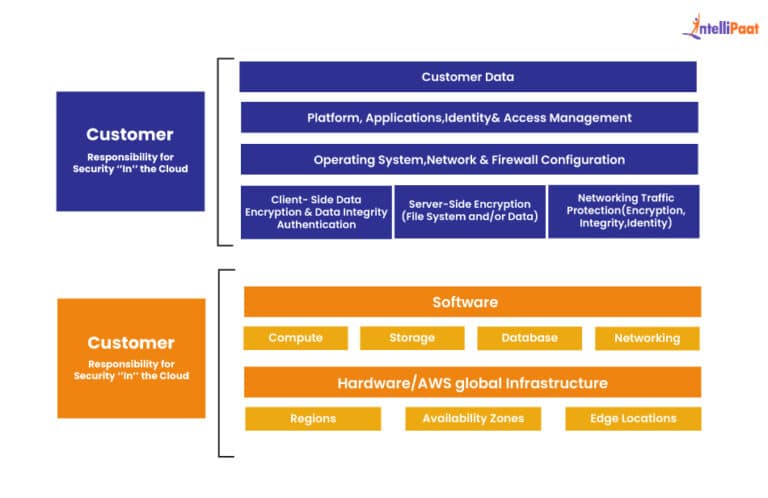
What Is The Aws Shared Responsibility Model The Cloud Security In cloud computing, aws follows the shared responsibility model. the responsibility here is shared between the customers to secure all their applications, data, and operations in the cloud and between aws for securing the cloud infrastructure. You are responsible for setting up and managing network controls, such as firewall rules, and for managing platform level identity and access management separately from iam.
Comments are closed.