Aws Cryptographic Computing Amazon Web Services

Amazon Web Services Aws Cloud Computing Services What is cryptographic computing at aws? aws cryptography tools and services utilize a wide range of encryption and storage technologies that can help you protect your data at rest and in transit. Aws has already made several innovations in cryptographic computing, and we're creating new opportunities for data owners and data users across a wide range of industries to engage and collaborate.

Cryptographic Details Aws Payment Cryptography This post, part of a series on cryptography in the cloud, provides an overview of the cloud cryptography services offered within amazon web services (aws): when to use them, when not to use them, and important usage considerations. In this blog post, we’ll delve into the world of aws cryptographic services and tools, exploring their capabilities, use cases, and best practices for securing your cloud resources. the importance of cryptography in amazon web services (aws) cannot be overstated. Learn about aws's experience implementing and deploying cryptographic algorithms that utilize carefully targeted micro architectural optimizations and are formally verified with automated reasoning. The following tables summarize the cryptographic algorithms, modes, and key sizes that aws considers suitable for deployment across its services to protect your data.

Aws Amazon Web Services Cloud Computing Platform Stock Photo Alamy Learn about aws's experience implementing and deploying cryptographic algorithms that utilize carefully targeted micro architectural optimizations and are formally verified with automated reasoning. The following tables summarize the cryptographic algorithms, modes, and key sizes that aws considers suitable for deployment across its services to protect your data. If you heavily use aws services, prioritize a cryptography solution like aws kms or acm that integrates seamlessly with s3, rds, or lambda. this ensures smoother workflows and reduces development effort. To address these needs, amazon web services (aws) is developing new techniques for cryptographic computing, a set of technologies that allow computations to be performed on encrypted data, so that sensitive data is never exposed. Choosing the right aws cryptography services depends on your specific use case, data security requirements, compliance obligations, and operational preferences as outlined in the following tables. Most aws services that support server side encryption are integrated with aws key management service (aws kms) to protect the encryption keys that protect your data. for a list of integrated services, see aws service integration.
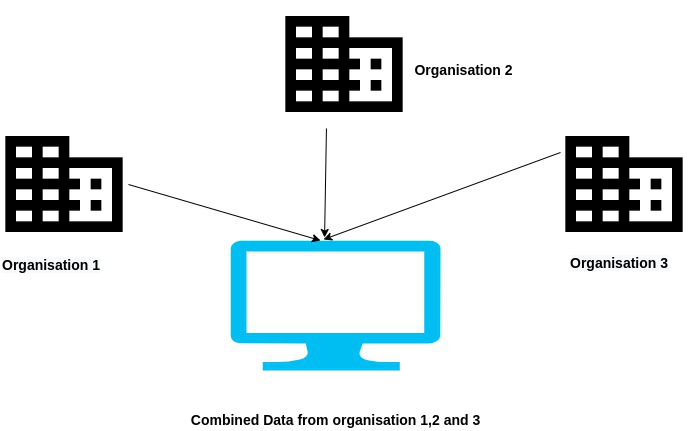
Amazon Web Services Introduction To Cryptographic Computing If you heavily use aws services, prioritize a cryptography solution like aws kms or acm that integrates seamlessly with s3, rds, or lambda. this ensures smoother workflows and reduces development effort. To address these needs, amazon web services (aws) is developing new techniques for cryptographic computing, a set of technologies that allow computations to be performed on encrypted data, so that sensitive data is never exposed. Choosing the right aws cryptography services depends on your specific use case, data security requirements, compliance obligations, and operational preferences as outlined in the following tables. Most aws services that support server side encryption are integrated with aws key management service (aws kms) to protect the encryption keys that protect your data. for a list of integrated services, see aws service integration.
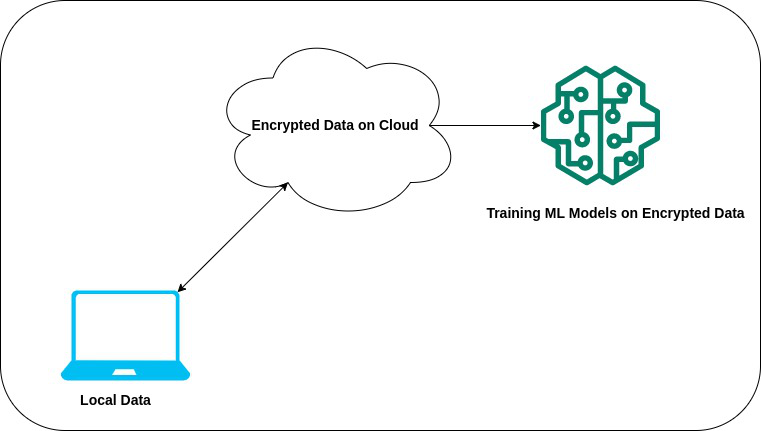
Amazon Web Services Introduction To Cryptographic Computing Choosing the right aws cryptography services depends on your specific use case, data security requirements, compliance obligations, and operational preferences as outlined in the following tables. Most aws services that support server side encryption are integrated with aws key management service (aws kms) to protect the encryption keys that protect your data. for a list of integrated services, see aws service integration.
Comments are closed.