Automating Security Workflows With Agents

Automating Security Workflows With Agents Ai powered agents represent the natural evolution of security copilot, going beyond ai assistant capabilities. they autonomously manage high volume security and it tasks, seamlessly integrated with microsoft security solutions and partner solutions. This example streamlines routine security assessment workflows by orchestrating multiple expert agents using microsoft autogen and making interactive endpoints available via fastapi.
Agentic Workflows Automated Security Workflow That Works Security copilot provides pre built workflows, integrates seamlessly with microsoft tools, and simplifies agent deployment. security copilot includes a red canary plugin that retrieves red canary security event information, enabling you to automate workflows and trigger custom azure logic apps. The 11 ai agents below map to each of these stages, automating key steps and connecting the dots across tools to reduce noise, speed up investigation, and strengthen overall response. At google, we’ve moved from talking about ai agents to actively using them for security with a dedicated, focused approach to building ai agents boldly and responsibly. here are four critical. To get started with microsoft security copilot and harness agentic ai to transform security and it operations, follow these steps in the journey to discover and use agents.

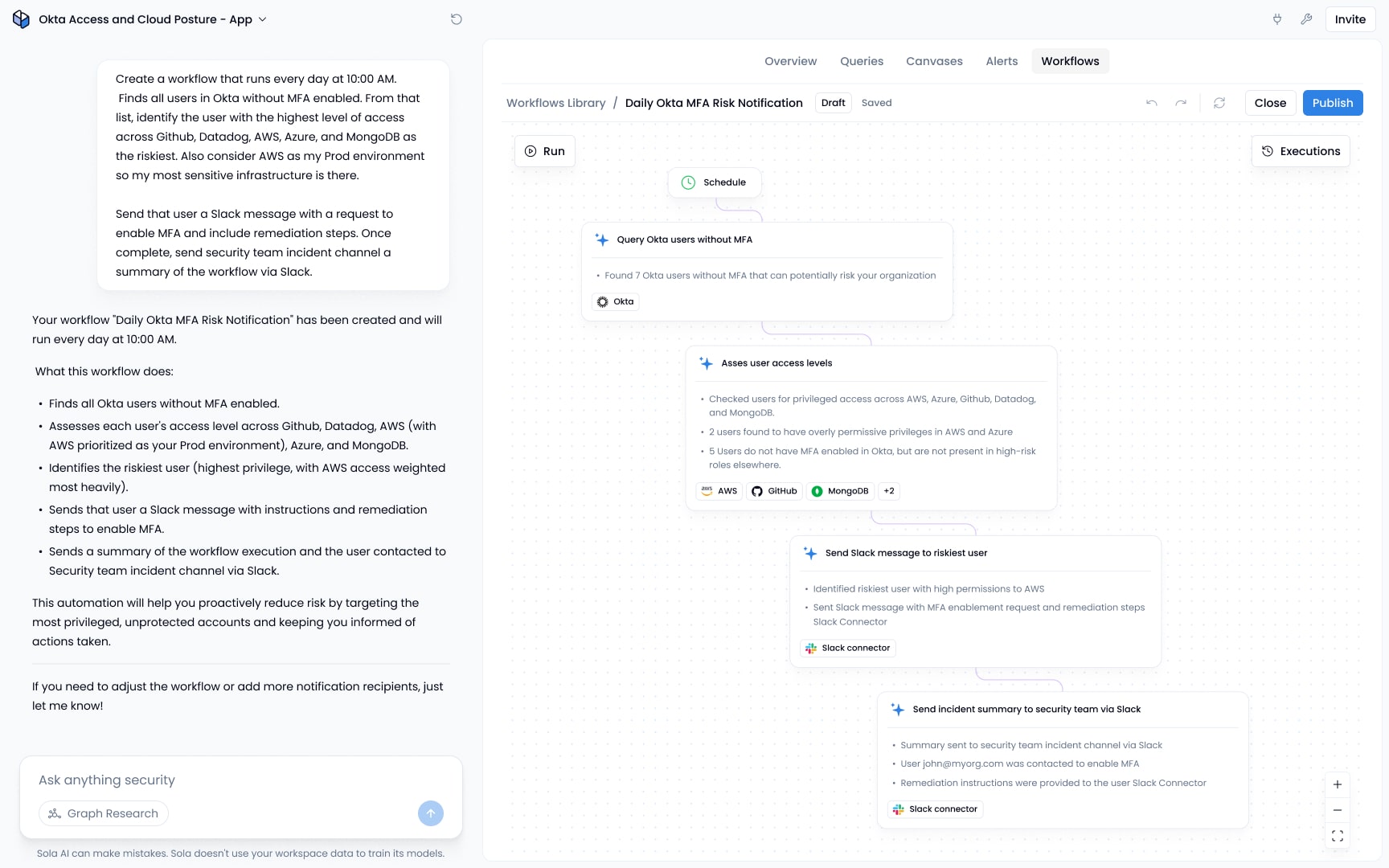
On Demand Webinar Attack Automation With Computer Using Agents Push At google, we’ve moved from talking about ai agents to actively using them for security with a dedicated, focused approach to building ai agents boldly and responsibly. here are four critical. To get started with microsoft security copilot and harness agentic ai to transform security and it operations, follow these steps in the journey to discover and use agents. Working alongside your human experts, torq hyperagents infuses agentic reasoning into security workflows, automating repetitive tasks and executing context aware actions to speed up analysis, response, and communication. See how tenable hexa ai custom agents empower you to counter machine speed threats by automating vulnerability remediation. learn how the model context protocol (mcp) automates execution of risk driven patching workflows, shifting your strategy from reactive tracking to continuous exposure management. Learn how soc automation reduces manual workloads, improves threat detection, and accelerates response with ai driven tools and real time security workflows. Discover how to build secure automated workflows with cybersecurity ai agents, protecting systems while optimizing efficiency and threat response.
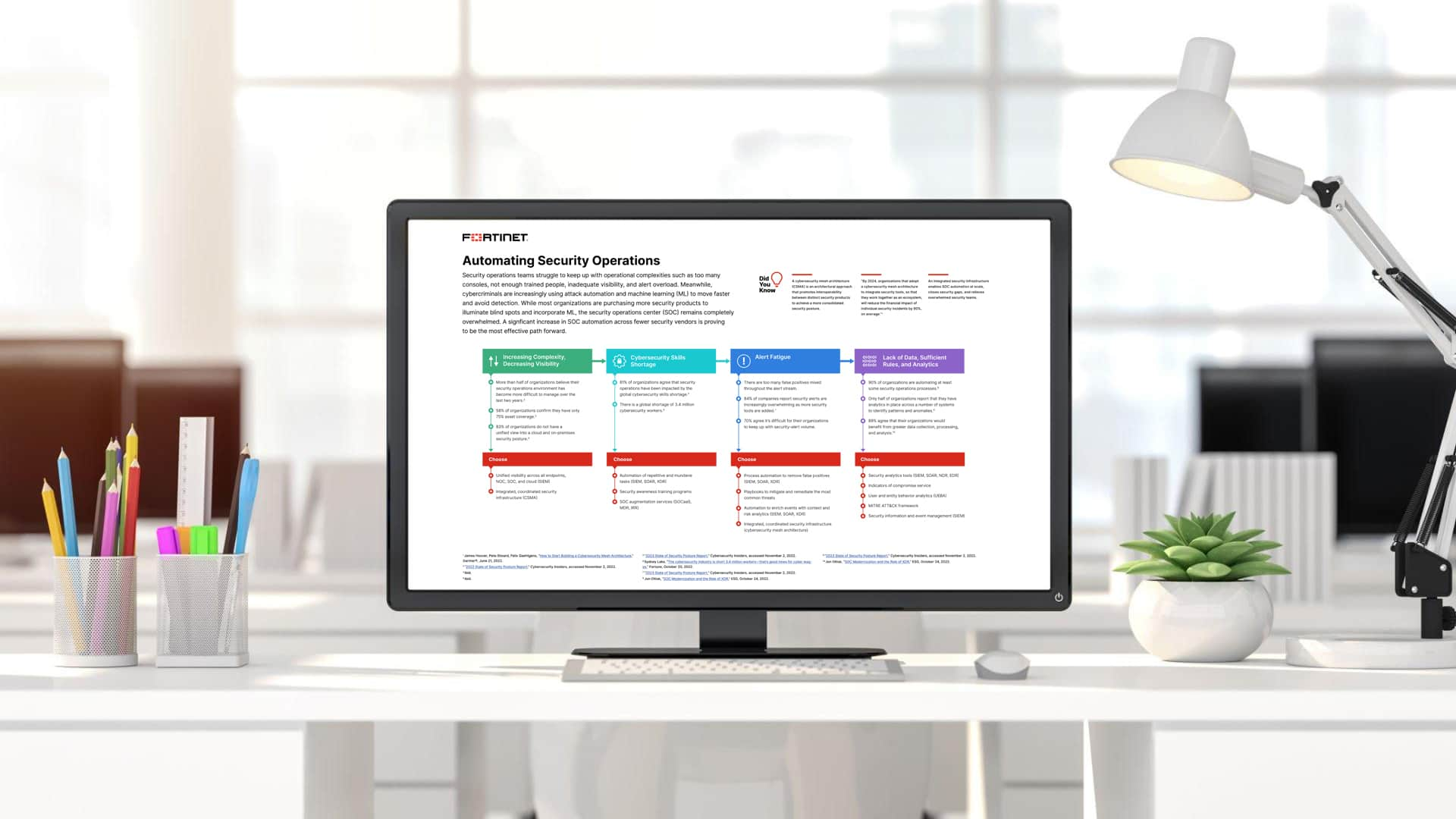
Automating Security Operations B2b Insights Working alongside your human experts, torq hyperagents infuses agentic reasoning into security workflows, automating repetitive tasks and executing context aware actions to speed up analysis, response, and communication. See how tenable hexa ai custom agents empower you to counter machine speed threats by automating vulnerability remediation. learn how the model context protocol (mcp) automates execution of risk driven patching workflows, shifting your strategy from reactive tracking to continuous exposure management. Learn how soc automation reduces manual workloads, improves threat detection, and accelerates response with ai driven tools and real time security workflows. Discover how to build secure automated workflows with cybersecurity ai agents, protecting systems while optimizing efficiency and threat response.
Comments are closed.