Automatic Proxy Configuration For Zscaler Skyhigh Security

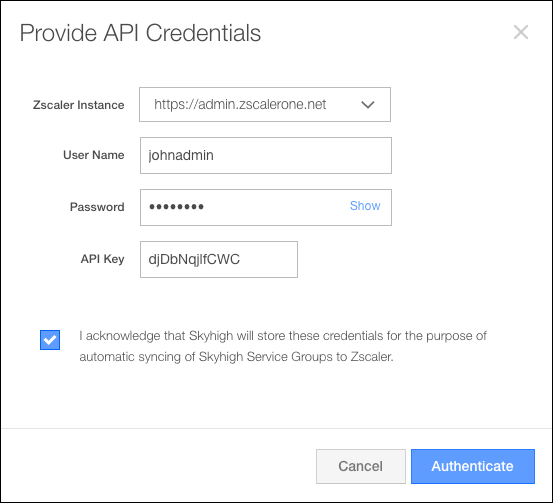
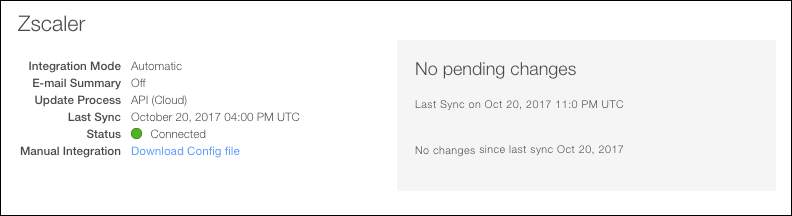
Skyhigh Security Client Proxy 4 5 0 Free Download Filecr You can configure skyhigh casb service groups to sync to zscaler manually or automatically: automatic. use the following instructions to sync to zscaler automatically. manual. if at any time you want to continue using the manual integration method, download the config file on the clr screen. Information on the identity proxy settings page. this is where zscaler users can view and modify identity proxy settings for cloud apps (box, google apps, salesforce, sharefile, or github).
Automatic Proxy Configuration For Zscaler Skyhigh Security Pac (proxy auto configuration) files define how web browsers and other user agents can automatically choose the appropriate proxy server for fetching a given url. Proxy auto configuration (pac) file bypasses are used for http https traffic (ports 80 and 443). these are useful when you need to define specific rules for what traffic should be sent directly to its destination and what traffic should go through the zscaler zero trust exchange. The course will offer an in depth look at traffic forwarding options for mobile users, including the functionality of zscaler client connector and the use of proxy autoconfig (pac) files. While running zscaler client connector and attempting to override the macos proxy settings, the local macos http s proxy settings should be automatically enabled and updated to use the local ip address and port for proxyman.
Automatic Proxy Configuration For Zscaler Skyhigh Security The course will offer an in depth look at traffic forwarding options for mobile users, including the functionality of zscaler client connector and the use of proxy autoconfig (pac) files. While running zscaler client connector and attempting to override the macos proxy settings, the local macos http s proxy settings should be automatically enabled and updated to use the local ip address and port for proxyman. The autopilot profile is downloaded and processed, you can sign into aad, enroll in intune, and fully configure the device, all using the proxy server (as long as there’s no authentication required – make sure you whitelist all the needed hosts). Set your browser proxy to gateway. [ yourzscalerdomain]:80. for example if your zscaler domain is zscalerbeta ; use gateway.zscalerbeta :80 proxy. add your okta url host ([yoursubdomain].okta ) and *.oktacdn to the proxy bypass list. your users are ready to single sign on to zscaler. It provides an overview of proxy autoconfiguration (pac) files, the zscaler client connector application, generic encrypted tunnel (gre) tunnels, and ipsec vpns. You also have the option to enable the automatic install of the zscaler default, or a custom certificate that users will require if the zia ssl inspection option is enabled.
Comments are closed.