Attacks Vectors Cybersecurity Tutorials For Beginners
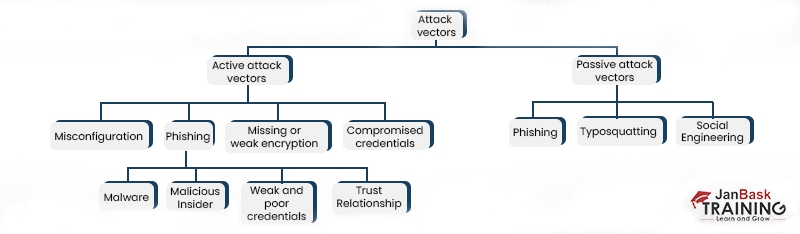
What Are Attack Vectors In Cyber Security This section covers cybercrimes, attacker behavior and common attack techniques. cyber crimes cyber criminal types social engineering cyber stalking botnets attack vector malware phishing identity theft cybersecurity evolution & objectives covers the evolution of cybersecurity along with frameworks, metrics and protection of critical. In this article we will look at what is an attack vector and some examples of attack vectors using which cyber attacks are performed. this article is a part of our cyber security tutorial for beginners.

Top 10 Common Vectors Of Cyberattacks Understand phishing, malware, ddos, and other common attack types. learn how attacks work and how to defend against them. cyber attacks are increasing, and understanding attack vectors is essential for defense. Deepen your understanding of cybersecurity threat vectors. this tutorial breaks down specific attack types, their mechanisms, and how to identify them early. That’s where attack vectors come into play—the methods cybercriminals use to sneak into systems, steal data, and cause chaos. our guide breaks down attack vectors in plain english—what they are, why they matter, and how to stay ahead of bad actors before they get the upper hand. Attack vectors are the method that adversaries use to breach a network. recognizing and tracking them is key for cybersecurity. learn more!.

What Are Attack Vectors In Cyber Security That’s where attack vectors come into play—the methods cybercriminals use to sneak into systems, steal data, and cause chaos. our guide breaks down attack vectors in plain english—what they are, why they matter, and how to stay ahead of bad actors before they get the upper hand. Attack vectors are the method that adversaries use to breach a network. recognizing and tracking them is key for cybersecurity. learn more!. Learn how to protect your organization from cyber threats by understanding attack vectors. this guide covers types of attack vectors, real world examples, and key prevention strategies. Explore our cyber security for beginners courses and learn about different types of cyber threats, common attack vectors, and important security principles. discover the significance of network security, web security, and cloud security in safeguarding digital assets. Explore the most common types of cyber attack vectors; from phishing and ransomware to insider threats and zero day exploits. learn how attackers gain entry, what makes systems vulnerable, and how to mitigate risks with proven security strategies. In this cybersecurity tutorial, you will learn how to identify and analyze potential attack vectors, understand the fundamentals of cybersecurity threats, and implement effective strategies to mitigate cybersecurity risks and vulnerabilities.
How To Identify Potential Attack Vectors In Cybersecurity Labex Learn how to protect your organization from cyber threats by understanding attack vectors. this guide covers types of attack vectors, real world examples, and key prevention strategies. Explore our cyber security for beginners courses and learn about different types of cyber threats, common attack vectors, and important security principles. discover the significance of network security, web security, and cloud security in safeguarding digital assets. Explore the most common types of cyber attack vectors; from phishing and ransomware to insider threats and zero day exploits. learn how attackers gain entry, what makes systems vulnerable, and how to mitigate risks with proven security strategies. In this cybersecurity tutorial, you will learn how to identify and analyze potential attack vectors, understand the fundamentals of cybersecurity threats, and implement effective strategies to mitigate cybersecurity risks and vulnerabilities.
Basics Of Exploitation Attack Vectors Explore the most common types of cyber attack vectors; from phishing and ransomware to insider threats and zero day exploits. learn how attackers gain entry, what makes systems vulnerable, and how to mitigate risks with proven security strategies. In this cybersecurity tutorial, you will learn how to identify and analyze potential attack vectors, understand the fundamentals of cybersecurity threats, and implement effective strategies to mitigate cybersecurity risks and vulnerabilities.

Emerging Attack Vectors And Techniques Onelayer
Comments are closed.