Attack Simulation Training With Microsoft Defender
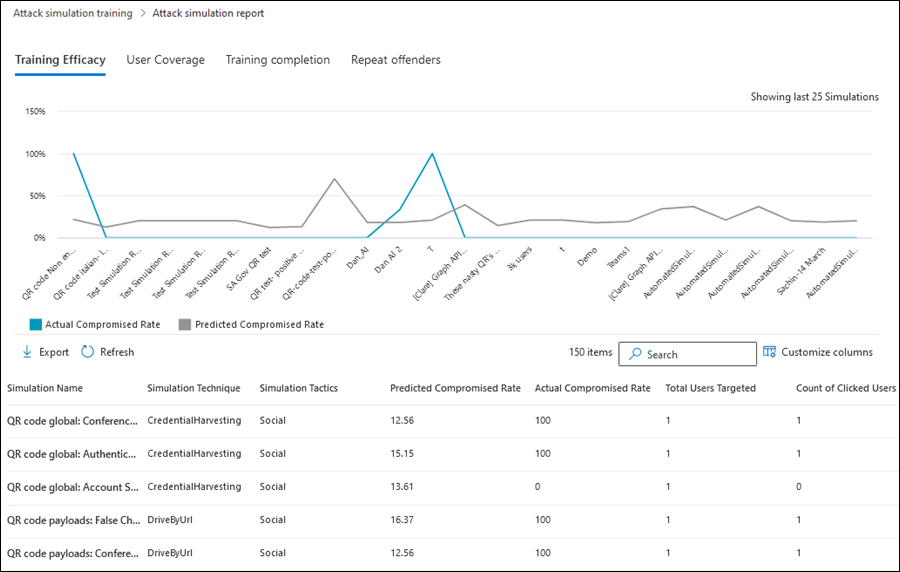
Reports For Attack Simulation Training Microsoft Defender For Office Admins can learn how to simulate phishing attacks and train their users on phishing prevention using attack simulation training in microsoft defender for office 365 plan 2. A complete step by step guide to microsoft 365 attack simulation training, covering setup, phishing payload selection, targeting, training assignments, reporting, and best practices to help organizations strengthen user awareness and reduce phishing risks.
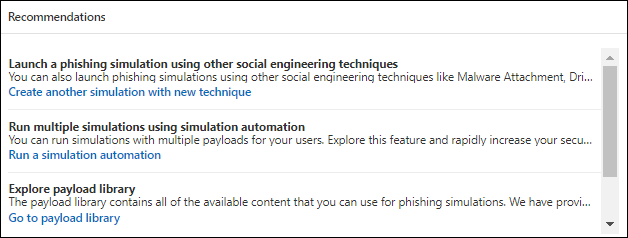
Reports For Attack Simulation Training Microsoft Defender For Office In organizations with microsoft defender for office 365 plan 2 (add on licenses or included in subscriptions like microsoft 365 e5), you can use attack simulation training in the microsoft defender portal to run realistic attack scenarios in your organization. In this blog, i am showing the different features within microsoft defender for office 365's attack simulation solution. Learn how to create targeted attack simulation training in microsoft defender with dynamic groups to simulate real world phishing attacks. To launch a simulated phishing attack, perform the following steps: navigate to the microsoft defender portal → email & collaboration → attack simulation training → simulations. select launch a simulation. choose the technique you’d like to use. the available options are: credential harvest. malware attachment. link in attachment. link to malware.
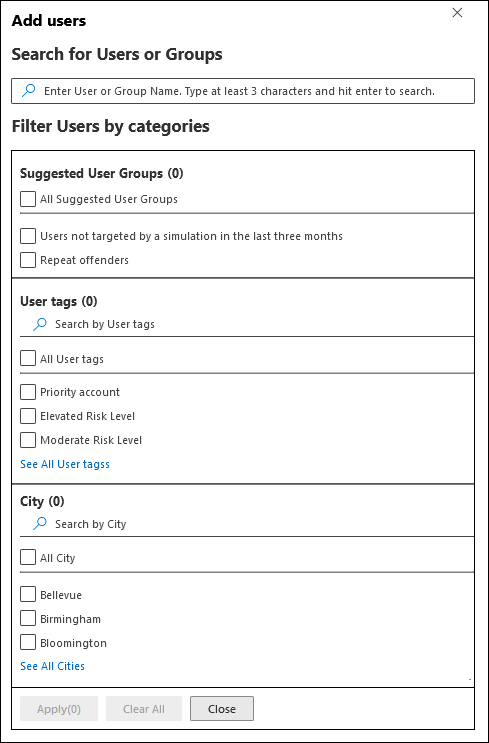
Training Campaigns In Attack Simulation Training Microsoft Defender Learn how to create targeted attack simulation training in microsoft defender with dynamic groups to simulate real world phishing attacks. To launch a simulated phishing attack, perform the following steps: navigate to the microsoft defender portal → email & collaboration → attack simulation training → simulations. select launch a simulation. choose the technique you’d like to use. the available options are: credential harvest. malware attachment. link in attachment. link to malware. Real review of microsoft attack simulation training. licensing reality, compliance requirements, when it works, when you need alternatives. This article demonstrates how microsoft defender for office 365 attack simulation training can be used, from prerequisites and licensing to simulation setup and result analysis. Learn how to delivery #cybersecurity training to users and conduct attack simulation using #microsoft #defender plan the attack, choose payload, target users, educate them and analyse the. Learn how to create launch simulation attacks in microsoft defender for office 365. learn to analyze results and setup custom simulation attacks.
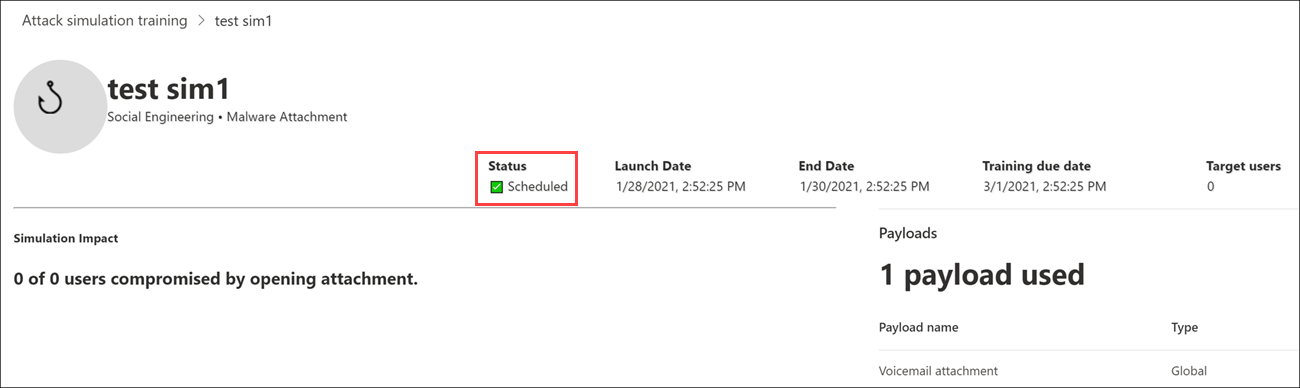
Attack Simulation Training Deployment Considerations And Faq Real review of microsoft attack simulation training. licensing reality, compliance requirements, when it works, when you need alternatives. This article demonstrates how microsoft defender for office 365 attack simulation training can be used, from prerequisites and licensing to simulation setup and result analysis. Learn how to delivery #cybersecurity training to users and conduct attack simulation using #microsoft #defender plan the attack, choose payload, target users, educate them and analyse the. Learn how to create launch simulation attacks in microsoft defender for office 365. learn to analyze results and setup custom simulation attacks.
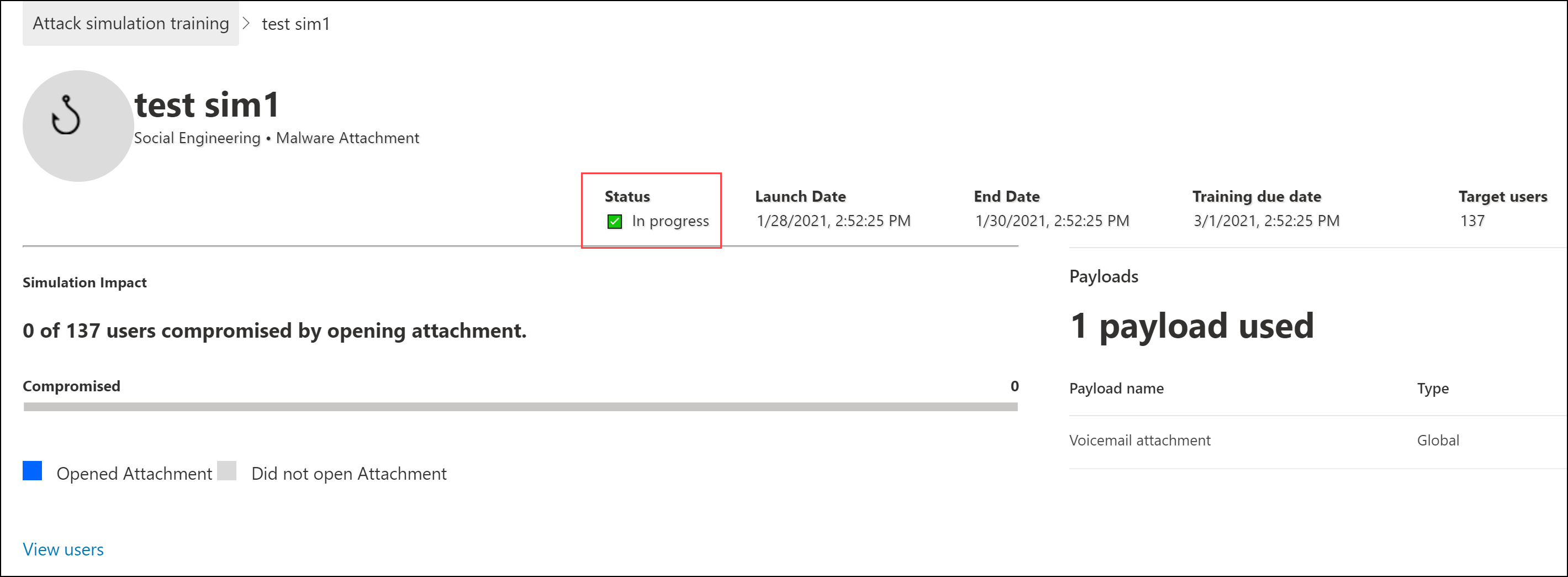
Attack Simulation Training Deployment Considerations And Faq Learn how to delivery #cybersecurity training to users and conduct attack simulation using #microsoft #defender plan the attack, choose payload, target users, educate them and analyse the. Learn how to create launch simulation attacks in microsoft defender for office 365. learn to analyze results and setup custom simulation attacks.
Comments are closed.