Attack Simulation Series

Cybereason Attack Simulation Series Get an inside look at how multi stage attack campaigns operate today and the ways a defender can break the kill chain and end the attack before crown jewels are compromised. Nukemap is a website for visualizing the effects of nuclear detonations.
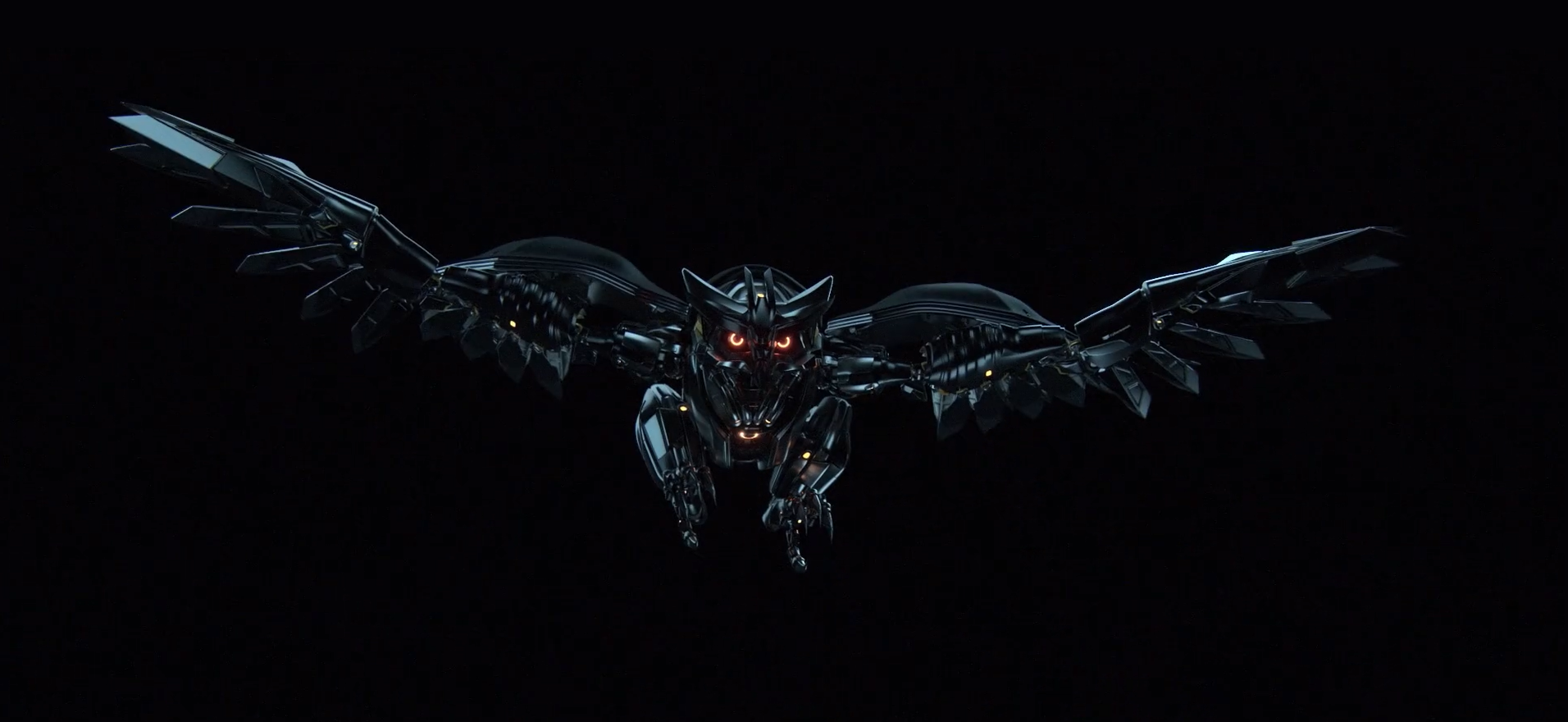
Attack Simulation Series These simulations test your security policies and practices, as well as train your employees to increase their awareness and decrease their susceptibility to attacks. this article walks you through creating a simulated phishing attack using attack simulation training. Join security analysts ed lin and brock bauer for a series that walks through breaches in real time, demonstrating the most popular tactics attackers use. learn their entry, bypass, and obfuscation methods, and then watch as we walk you through the steps you can take to respond to these threats. Nukesim is for one thing: helping people understand, fast, what different nuclear weapons would do in real places. you can run scenarios on the map, compare weapon profiles, read context, and follow live external news without jumping between tools. Here you will find some samples, scripts, tools and other pieces of information that we feel as a product group will help you get the most out of our feature attack simulation and training.

Cyber Attack Simulation Aquila I Solutions Nukesim is for one thing: helping people understand, fast, what different nuclear weapons would do in real places. you can run scenarios on the map, compare weapon profiles, read context, and follow live external news without jumping between tools. Here you will find some samples, scripts, tools and other pieces of information that we feel as a product group will help you get the most out of our feature attack simulation and training. We wanted to answer this question with a visually compelling multimedia experience, so we partnered with bluecadet to design a location based interactive that made it easy to learn how a bomb blast would affect your neighborhood. In this special attack simulation, you will: witness the attacker's infiltration watch the malicious operation as it moves across the entire environment see the way a defender can break the kill chain and end an attack. A general discussion on the historic threat of nuclear weapons, the impact a nuclear attack would have on the united states, and technical details and background on the simulation models. It merges threat intelligence, vulnerability data, attack surface management and continuous testing to give you real time clarity on which critical adversary behaviors would bypass controls and succeed in your environment—and how to fix the issues before attackers can exploit them.

Live Attack Simulation Ransomware Threat Hunter Series We wanted to answer this question with a visually compelling multimedia experience, so we partnered with bluecadet to design a location based interactive that made it easy to learn how a bomb blast would affect your neighborhood. In this special attack simulation, you will: witness the attacker's infiltration watch the malicious operation as it moves across the entire environment see the way a defender can break the kill chain and end an attack. A general discussion on the historic threat of nuclear weapons, the impact a nuclear attack would have on the united states, and technical details and background on the simulation models. It merges threat intelligence, vulnerability data, attack surface management and continuous testing to give you real time clarity on which critical adversary behaviors would bypass controls and succeed in your environment—and how to fix the issues before attackers can exploit them.
Comments are closed.