Application Security Testing Types Cycode
Types Of Application Security Testing Tools In 2025 Cycode This guide will break down the most critical types of application and software security testing, explaining how each works, when to use them, and their strengths and limitations. This guide will break down the most critical types of application and software security testing, explaining how each works, when to use them, and their strengths and limitations.

Connectorx App Security Testing Complete Aspm With Cycode It combines application security testing (ast), software supply chain security, and application security posture management (aspm) to eliminate silos and provide actionable, code to runtime context. Cycode is an ai native application security platform focused on delivering integrated security protections across the software development lifecycle, covering application security testing, security posture management, and software supply chain security. The cycode command line interface (cli) is an application you can install locally to scan your repositories for secrets, infrastructure as code misconfigurations, software composition analysis vulnerabilities, and static application security testing issues. Cycode is an ai powered application security posture management (aspm) platform that revolutionizes software security. it delivers comprehensive protection from source code to cloud deployment, leveraging advanced ai analytics for real time threat detection and automated vulnerability remediation.
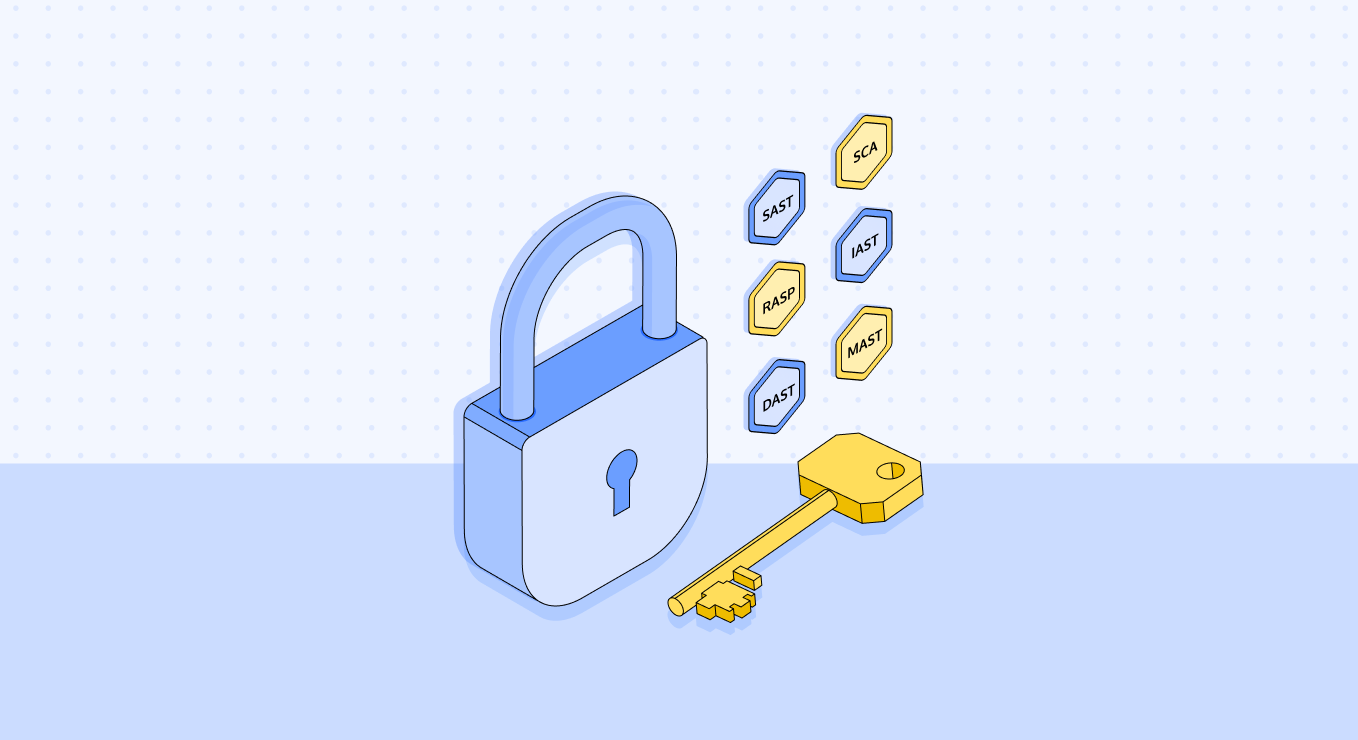
Application Security Testing Types Cycode The cycode command line interface (cli) is an application you can install locally to scan your repositories for secrets, infrastructure as code misconfigurations, software composition analysis vulnerabilities, and static application security testing issues. Cycode is an ai powered application security posture management (aspm) platform that revolutionizes software security. it delivers comprehensive protection from source code to cloud deployment, leveraging advanced ai analytics for real time threat detection and automated vulnerability remediation. Cycode is unique in its ability to perform software composition analysis on both software and pipeline components and to pinpoint vulnerable dependency locations in production. Combines sast, nextgen sca, secrets detection, iac security, container scanning, and pipeline security in a single platform. delivers continuous insight into security posture from code to cloud with centralized dashboards and automated alerts. Learn about the different types of application security testing tools sast, dast, sca and more that help build a comprehensive devsecops strategy. These techniques examine source code, application behavior at runtime, and interactions between components to uncover potential vulnerabilities, such as cross site scripting (xss), sql injection, insecure authentication, and misconfigured permissions.
Application Security Testing Types Cycode Cycode is unique in its ability to perform software composition analysis on both software and pipeline components and to pinpoint vulnerable dependency locations in production. Combines sast, nextgen sca, secrets detection, iac security, container scanning, and pipeline security in a single platform. delivers continuous insight into security posture from code to cloud with centralized dashboards and automated alerts. Learn about the different types of application security testing tools sast, dast, sca and more that help build a comprehensive devsecops strategy. These techniques examine source code, application behavior at runtime, and interactions between components to uncover potential vulnerabilities, such as cross site scripting (xss), sql injection, insecure authentication, and misconfigured permissions.

Application Security Testing Types Cycode Learn about the different types of application security testing tools sast, dast, sca and more that help build a comprehensive devsecops strategy. These techniques examine source code, application behavior at runtime, and interactions between components to uncover potential vulnerabilities, such as cross site scripting (xss), sql injection, insecure authentication, and misconfigured permissions.
Comments are closed.