Analyzing Encrypted Malware Callbacks Pdf Component Object Model

Are Malware Detection Models Adversarial Robust Against Reversing encrypted callbacks and com interfaces free download as pdf file (.pdf), text file (.txt) or read online for free. the document discusses a virus that uses com interfaces and encrypted callbacks to communicate with a command and control server. Specific com objects also exist to directly perform functions beyond code execution, such as creating a scheduled task job, fileless download execution, and other adversary behaviors related to privilege escalation and persistence.

Analyzing Encrypted Malware Callbacks Pdf Component Object Model One of the main reasons i wrote this paper was to explain in depth the different stages involved in viruses that exchange data with the callback server using encrypted channels. A tutorial on bayesian optimization of expensive cost functions, with application to active user modeling and hierarchical reinforcement learning 12th dec 2016 (bayopt).pdf. In addition to malware classification, researchers in malware analysis have improved new techniques and methods to analyze the composition of malware samples by matching their functionalities and behaviors to multiple known malware families. We showcase how component object model (com) and windows management instrumentation (wmi) can be used to create such spoofing attacks. we discuss the internals of com and wmi and asynchronous local procedure call (alpc).

How To Decrypt And Analyze Encrypted Malware Payloads In addition to malware classification, researchers in malware analysis have improved new techniques and methods to analyze the composition of malware samples by matching their functionalities and behaviors to multiple known malware families. We showcase how component object model (com) and windows management instrumentation (wmi) can be used to create such spoofing attacks. we discuss the internals of com and wmi and asynchronous local procedure call (alpc). Encrypted malware by this method consists of encryption and decryption algorithms, keys and malicious codes. each time attacker employs new encryption algorithm and key to generate novel malware version. Encryption protocols may be utilized during the packing process to encrypt the entire packed file, making it harder for security tools to identify detect the malicious code or analyze its content. These components have hundreds of different com objects and have to load them through certain registry points. at this point, registry entries on specific clsid keys can be manipulated by an. The document discusses various techniques that malicious programs use to interact with the windows operating system and execute code, including using the windows api, handles, dlls, processes, threads, mutexes, services, and the component object model (com).

Overall Architecture Of The Malware Detection And Homology Analysis Encrypted malware by this method consists of encryption and decryption algorithms, keys and malicious codes. each time attacker employs new encryption algorithm and key to generate novel malware version. Encryption protocols may be utilized during the packing process to encrypt the entire packed file, making it harder for security tools to identify detect the malicious code or analyze its content. These components have hundreds of different com objects and have to load them through certain registry points. at this point, registry entries on specific clsid keys can be manipulated by an. The document discusses various techniques that malicious programs use to interact with the windows operating system and execute code, including using the windows api, handles, dlls, processes, threads, mutexes, services, and the component object model (com).
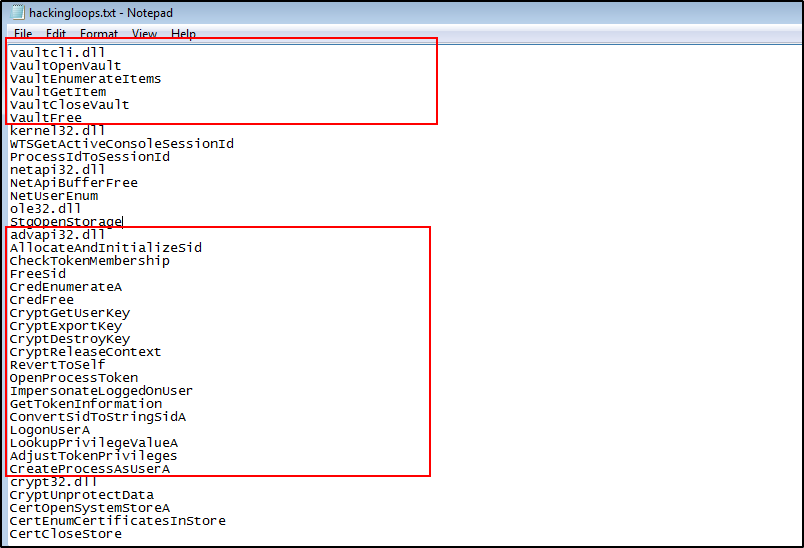
How To Perform Malware Analysis Without Code Execution These components have hundreds of different com objects and have to load them through certain registry points. at this point, registry entries on specific clsid keys can be manipulated by an. The document discusses various techniques that malicious programs use to interact with the windows operating system and execute code, including using the windows api, handles, dlls, processes, threads, mutexes, services, and the component object model (com).
Comments are closed.