Analyze A Dos Attack

Let S Learn The Technology Together How To Perform Dos Attack Early detection of a dos attack is crucial for mitigating its impact and ensuring business continuity. in this article, we will explore how organisations detect dos attacks, the tools and techniques used, and the importance of a proactive monitoring strategy. You know that a denial of service attack (dos attack) can make a machine or network resource unavailable to the employees in your company. these types of dos attacks are often done by.
Denial Of Service Dos Attack Types And Prevention Once your firewall and logging systems are set up, it’s time to simulate common attacks and analyze the resulting logs. common attacks include port scans, brute force attacks, and dos. After successfully conducting both a tcp based and udp based dos attack, we can begin to analyze the collected network traffic using zeek and the zeek cut utility commands to display the capture traffic. Identify the source, analyze network traffic for anomalies, determine the specific type of dos attack involved, and propose effective strategies to mitigate future attacks. This project demonstrates the impact of various denial of service (dos) attacks on a webserver using wireshark, a protocol analyzer. the attacks include syn flood, icmp flood, and address spoofing, analyzed through traffic magnitude and effectiveness using different attacker nodes.

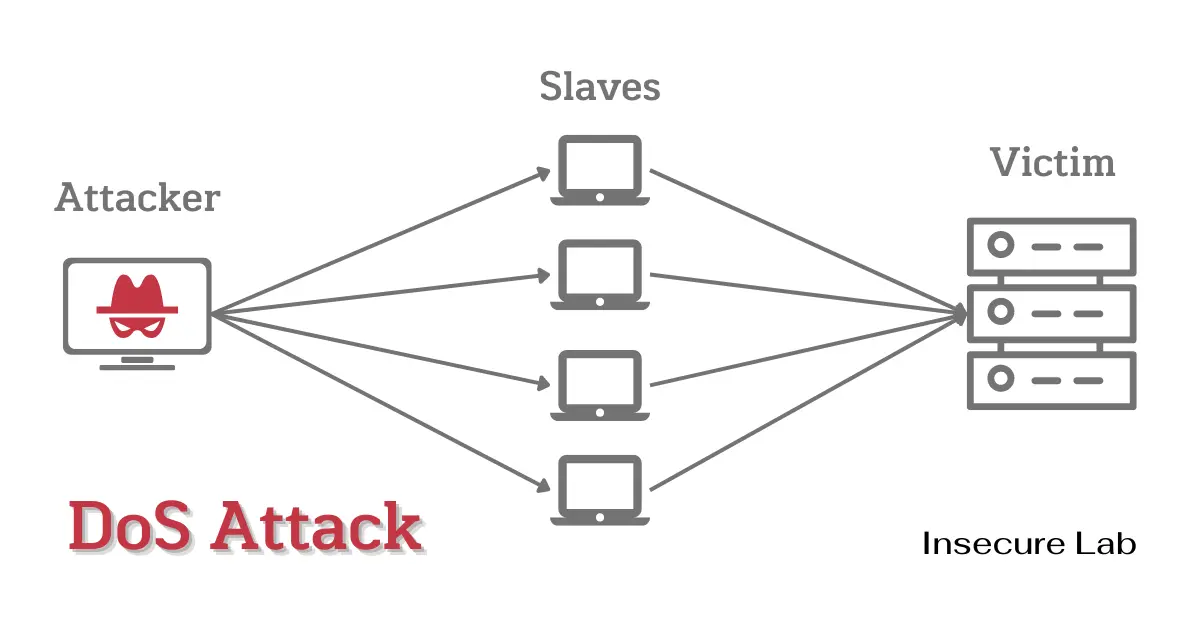
Dos Attack Illustration Stable Diffusion Online Identify the source, analyze network traffic for anomalies, determine the specific type of dos attack involved, and propose effective strategies to mitigate future attacks. This project demonstrates the impact of various denial of service (dos) attacks on a webserver using wireshark, a protocol analyzer. the attacks include syn flood, icmp flood, and address spoofing, analyzed through traffic magnitude and effectiveness using different attacker nodes. Dos attacks are attempts to interrupt a website or network's operations by overwhelming it with traffic. the attacker achieves this by sending an enormous amount of requests to the target server, which causes it to slow down or even crash, making it inaccessible to legitimate users. Once a potential dos attack has been detected, it is essential to analyze the attack traffic to determine the type and scope of the attack. this involves examining the traffic patterns, source ip addresses, and other characteristics of the attack. In this paper, we provide an extensive summary and analysis of the present techniques, tools, and best practices which are used to detect and defend against dos attacks. we also applied some machine learning algorithms with nsl kdd dataset in order to detect dos attack. Identify the attack: recognize the signs of a ddos attack, such as a sudden surge in traffic, increased network latency, or unavailability of services. use network monitoring tools and traffic analysis to confirm the attack.
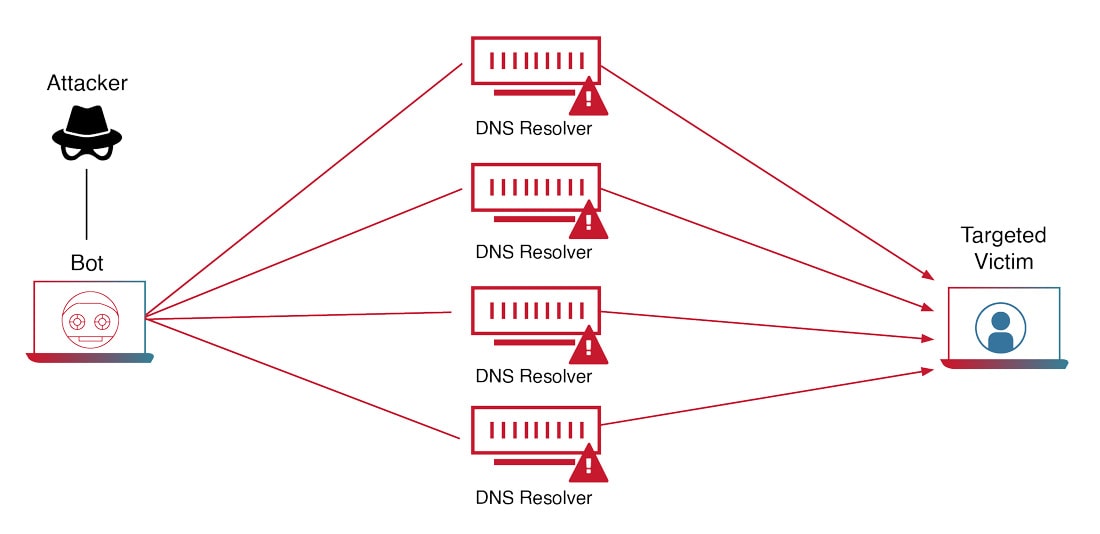
Dos Attack Dos attacks are attempts to interrupt a website or network's operations by overwhelming it with traffic. the attacker achieves this by sending an enormous amount of requests to the target server, which causes it to slow down or even crash, making it inaccessible to legitimate users. Once a potential dos attack has been detected, it is essential to analyze the attack traffic to determine the type and scope of the attack. this involves examining the traffic patterns, source ip addresses, and other characteristics of the attack. In this paper, we provide an extensive summary and analysis of the present techniques, tools, and best practices which are used to detect and defend against dos attacks. we also applied some machine learning algorithms with nsl kdd dataset in order to detect dos attack. Identify the attack: recognize the signs of a ddos attack, such as a sudden surge in traffic, increased network latency, or unavailability of services. use network monitoring tools and traffic analysis to confirm the attack.
Dos Attack Detection Scheme Download Scientific Diagram In this paper, we provide an extensive summary and analysis of the present techniques, tools, and best practices which are used to detect and defend against dos attacks. we also applied some machine learning algorithms with nsl kdd dataset in order to detect dos attack. Identify the attack: recognize the signs of a ddos attack, such as a sudden surge in traffic, increased network latency, or unavailability of services. use network monitoring tools and traffic analysis to confirm the attack.
Comments are closed.