10 3 10 Analyze A Ddos Attack

Analyze Ddos Attacks Wireshark Lab Report Insights Course Hero In this lab, we analyze a distributed denial of service (ddos) attack using wireshark. you’ll learn how to: capture packets on a live network segment more. Analyze the attack using the following filters: tcp.flags.syn==1 and tcp.flags.ack==1 tcp.flags.syn==1 and tcp.flags.ack==0 answer the question. complete this lab as follows: 1. from the favorites bar, open wireshark. 2. under capture, select enp2s0. 3. from the menu, select the blue fin.

Ddos Attack Detection Methodologies Ddos Attack Detection This article will guide you through the process of analyzing a ddos attack using wireshark, from capturing packets to interpreting the key indicators of malicious traffic. Detecting ddos attacks using wireshark involves a combination of monitoring traffic patterns, filtering suspicious packets, and analyzing network behaviors. by leveraging wireshark’s capabilities, you can identify potential threats and take immediate action to mitigate their impact. In this guide we present three options for simulating a ddos attack in your own lab:. This command initiates the pod attack on the windows 10 machine. in a pod attack, the attacker tries to crash, freeze, or destabilize the targeted system or service by sending malformed or oversized packets using a simple ping command.

Understanding And Preventing Ddos Attacks In this guide we present three options for simulating a ddos attack in your own lab:. This command initiates the pod attack on the windows 10 machine. in a pod attack, the attacker tries to crash, freeze, or destabilize the targeted system or service by sending malformed or oversized packets using a simple ping command. Analyzing a ddos attack involves monitoring network traffic for unusual spikes, identifying attack sources through ip tracking, and implementing countermeasures like rate limiting and traffic filtering. In this article, we will be looking on wireshark display filters and see how we could detect various network attacks with them in wireshark. Chances are, they might be a victim of what is known as a ddos attack, distributed denial of service attack. in a ddos attack, the attacker tries to make a particular service unavailable by directing continuous and huge traffic from multiple end systems. Identify the attack: recognize the signs of a ddos attack, such as a sudden surge in traffic, increased network latency, or unavailability of services. use network monitoring tools and traffic analysis to confirm the attack.
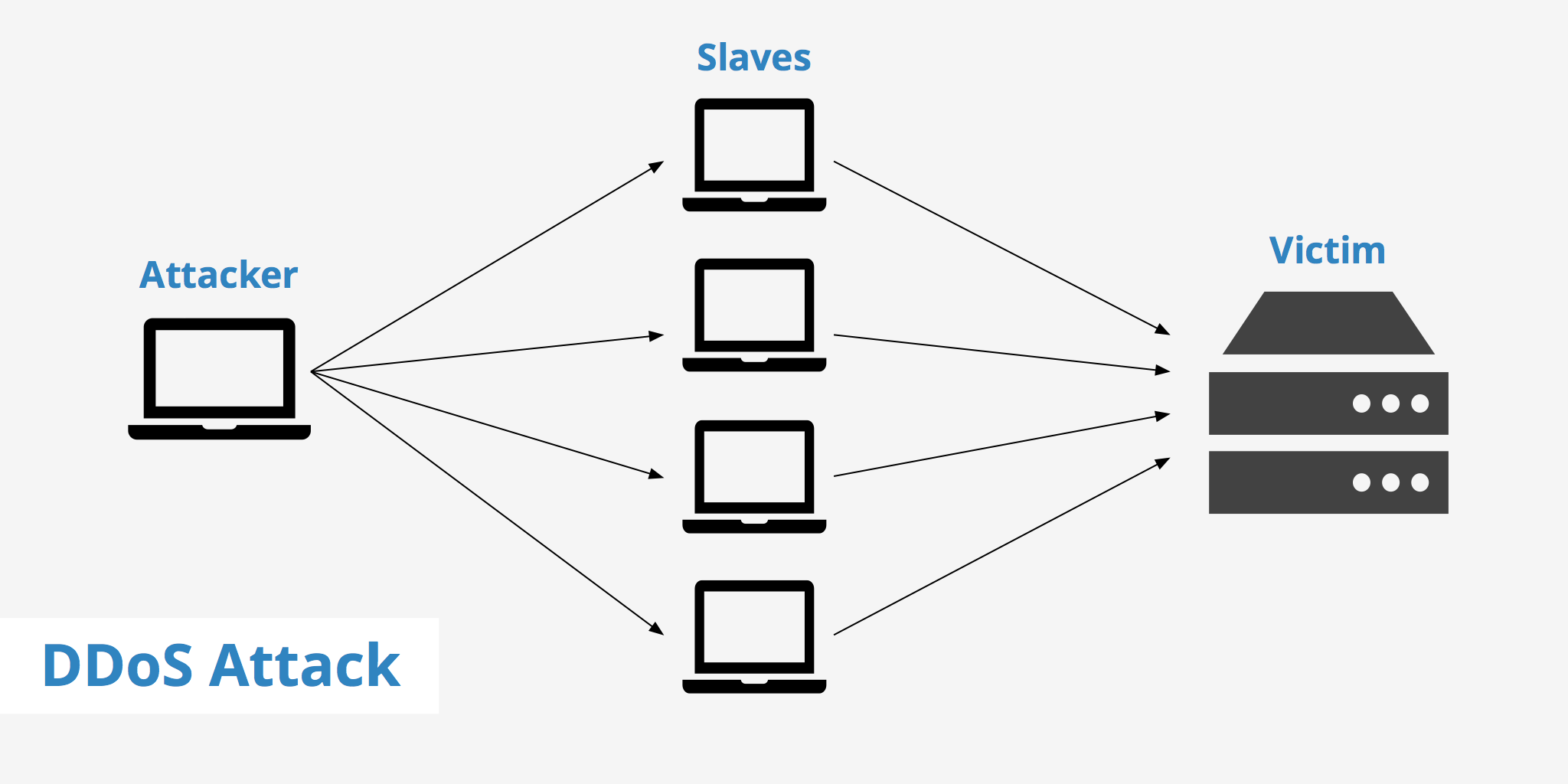
Ddos Attack Keycdn Support Analyzing a ddos attack involves monitoring network traffic for unusual spikes, identifying attack sources through ip tracking, and implementing countermeasures like rate limiting and traffic filtering. In this article, we will be looking on wireshark display filters and see how we could detect various network attacks with them in wireshark. Chances are, they might be a victim of what is known as a ddos attack, distributed denial of service attack. in a ddos attack, the attacker tries to make a particular service unavailable by directing continuous and huge traffic from multiple end systems. Identify the attack: recognize the signs of a ddos attack, such as a sudden surge in traffic, increased network latency, or unavailability of services. use network monitoring tools and traffic analysis to confirm the attack.
Comments are closed.