Aes Ecb Cryptography Breaking Encryption Without A Key

File Ecb Decryption Svg Wikimedia Commons Ecb (electronic codebook) is one of the simplest modes of operation for aes. in ecb mode, each block of plaintext is encrypted separately with the same key, and there is no feedback. This group of challenges focuses on aes ecb (electronic code book), implementing cbc (cipher block chaining) yourself, and decrypting an aes ecb ciphertext with a padding oracle. this is the challenge that put me off of cryptopals for a good four years, all because i missed the instruction:.

Not Only Is Zoom S Strong End To End Encryption Not Actually End To End Electronic code book (ecb) is the simplest aes block cipher mode. a block cipher takes a fixed size block of text (b bits) and a key and outputs a block of b bit encrypted text. A detailed walkthrough of how to exploit a padding oracle attack to break aes ecb encryption using a byte by byte decryption approach. A standard format for this is the cryptographic message syntax, or pkcs #7. because it's a standard, you will likely have several options for an open source library to handle the format. by including this metadata, you can do things like rotate keys over time, or migrate data to new algorithms. I have determined aes in ecb mode is used to encrypt arbitrarily supplied plaintext by an oracle. i hypothesize the flag is appended to the plaintext before it is encrypted.
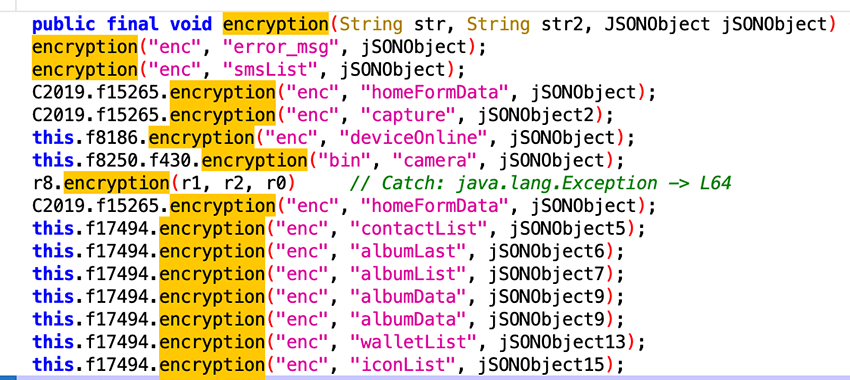
Toxicpanda Malware In 2025 Bitsight Trace Threat Research A standard format for this is the cryptographic message syntax, or pkcs #7. because it's a standard, you will likely have several options for an open source library to handle the format. by including this metadata, you can do things like rotate keys over time, or migrate data to new algorithms. I have determined aes in ecb mode is used to encrypt arbitrarily supplied plaintext by an oracle. i hypothesize the flag is appended to the plaintext before it is encrypted. Ofb 8 encryption returns the plaintext unencrypted for affected keys. some modes (such as aes siv and aes gcm siv) are built to be more nonce misuse resistant, i.e. resilient to scenarios in which the randomness generation is faulty or under the control of the attacker. In a project that i'm currently working on, we are encrypting some data using aes with ecb mode in a database. each piece of data being encrypted is very small, no more than 10 characters long. very importantly, each entry of that database is encrypted using a different and unique key. Encryption of different plaintext packets can be calculated in parallel, which is fast. the same plaintext block will be encrypted into the same ciphertext block, and the statistical rules of the plaintext grouping will not be hidden. as shown below. This repo contains two simple attacks on aes ecb. the purpose of these attacks is to demonstrate aes in mode ecb is insecure, in particular when multiple blocks are encrypted, and so aes should be used in a different mode (cbc, ctr, …) that incorporate a nonce or initialization vector.

Aes Ecb Examples Codesandbox Ofb 8 encryption returns the plaintext unencrypted for affected keys. some modes (such as aes siv and aes gcm siv) are built to be more nonce misuse resistant, i.e. resilient to scenarios in which the randomness generation is faulty or under the control of the attacker. In a project that i'm currently working on, we are encrypting some data using aes with ecb mode in a database. each piece of data being encrypted is very small, no more than 10 characters long. very importantly, each entry of that database is encrypted using a different and unique key. Encryption of different plaintext packets can be calculated in parallel, which is fast. the same plaintext block will be encrypted into the same ciphertext block, and the statistical rules of the plaintext grouping will not be hidden. as shown below. This repo contains two simple attacks on aes ecb. the purpose of these attacks is to demonstrate aes in mode ecb is insecure, in particular when multiple blocks are encrypted, and so aes should be used in a different mode (cbc, ctr, …) that incorporate a nonce or initialization vector.
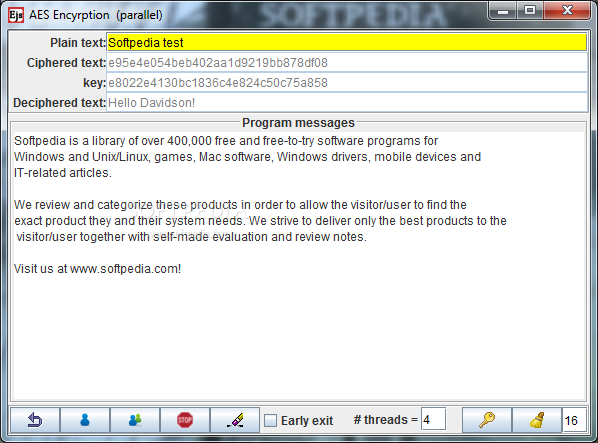
Breaking Aes Encryption Download Softpedia Encryption of different plaintext packets can be calculated in parallel, which is fast. the same plaintext block will be encrypted into the same ciphertext block, and the statistical rules of the plaintext grouping will not be hidden. as shown below. This repo contains two simple attacks on aes ecb. the purpose of these attacks is to demonstrate aes in mode ecb is insecure, in particular when multiple blocks are encrypted, and so aes should be used in a different mode (cbc, ctr, …) that incorporate a nonce or initialization vector.

Aes Advanced Encryption Standard In Cryptography
Comments are closed.