Adversarial Transferability And Beyond
Adversarial Transferability In Embedded Sensor Systems An Activity We categorize existing methodologies to enhance adversarial transferability and discuss the fundamental principles guiding each approach. while the predominant body of research primarily concentrates on image classification, we also extend our discussion to encompass other vision tasks and beyond. Conjecture: the effectiveness of adversarial examples can be increased by not only increasing the logit of the target class but also decreasing the probability of the ground truth class.
Github Jindonggu Awesome Adversarial Transferability A Curated List To enhance targeted ae transferability, we propose a novel approach using inverse target gradient competition (itc) and spatial distance stretching (sds) in the optimiza tion process. specifically, we employ a siamese network like framework to generate both non targeted and targeted aes. We conduct extensive experiments for different scenarios on diverse datasets, showing a positive correlation between adversarial transferability and knowledge transferability. our findings will shed light on future research about effective knowledge transfer learning and adversarial transferability analyses. Robustness against attackers is necessary for entrusting ai with life sensitive tasks, such as medical diagnosis. by exploring transferability, our work helps explain the nature of adversarial attacks and offers a defense direction via decorrelated ensembles of models. Lso brought to light a concerning vulnerability: adversarial examples. these crafted inputs, imperceptible to humans, can manipulate machine learning models into making err.

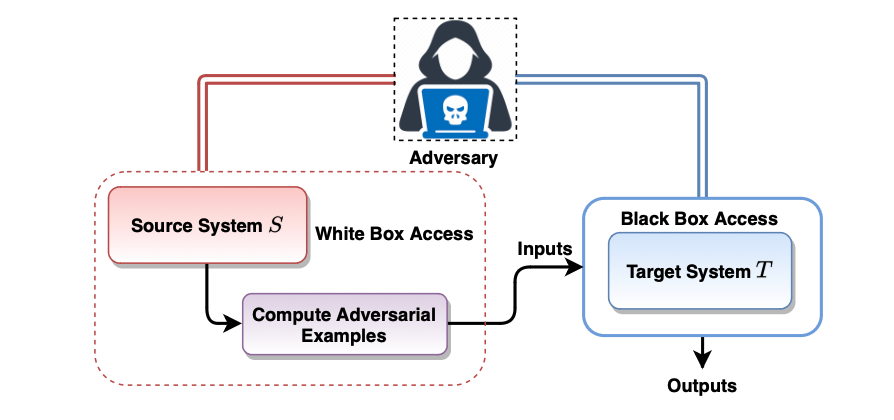
Disrupting Adversarial Transferability In Deep Neural Networks Robustness against attackers is necessary for entrusting ai with life sensitive tasks, such as medical diagnosis. by exploring transferability, our work helps explain the nature of adversarial attacks and offers a defense direction via decorrelated ensembles of models. Lso brought to light a concerning vulnerability: adversarial examples. these crafted inputs, imperceptible to humans, can manipulate machine learning models into making err. In this paper, for the first time, we revisit this convention and demonstrate that those discarded, sub optimal adversarial examples can be reused to boost transferability. We categorize existing methodologies to enhance adversarial transferability and discuss the fundamental principles guiding each approach. while the predominant body of research primarily concentrates on image classification, we also extend our discussion to encompass other vision tasks and beyond. In this section, we embark on a theoretical exploration of adversarial transferability, commencing with the canonical setup of transfer based adversarial attacks.
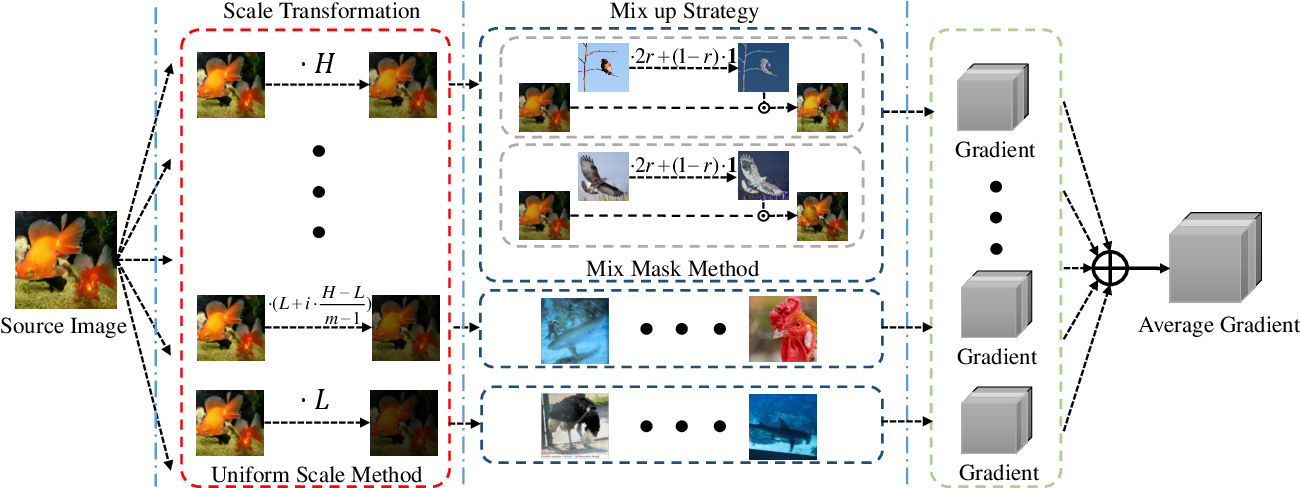
Boost Adversarial Transferability By Uniform Scale And Mix Mask Method In this paper, for the first time, we revisit this convention and demonstrate that those discarded, sub optimal adversarial examples can be reused to boost transferability. We categorize existing methodologies to enhance adversarial transferability and discuss the fundamental principles guiding each approach. while the predominant body of research primarily concentrates on image classification, we also extend our discussion to encompass other vision tasks and beyond. In this section, we embark on a theoretical exploration of adversarial transferability, commencing with the canonical setup of transfer based adversarial attacks.

What Is Adversarial Transferability In this section, we embark on a theoretical exploration of adversarial transferability, commencing with the canonical setup of transfer based adversarial attacks.

Transferability Ranking Of Adversarial Examples Ai Research Paper Details
Comments are closed.