Administering Security Infrastructure Pdf Security Computer Security

Administering Security Infrastructure Pdf Security Computer Security This document provides an overview and objectives of an online training course for administering imperva security infrastructure version 13.0. the course teaches students how to install, configure, and maintain securesphere system components and perform initial administration and configuration tasks. This course is intended for anyone who will need to configure and maintain securesphere, such as: database administrators, security team role(s), system administrators, web application developers, and professional services using imperva securesphere.

Monitoring And Administering System And Network Security Pdf This is a documentation describing the situation of computer security incident and how a business will continue to function. the situations are catastrophic situations and long duration. Security planning risk analysis security policies cyber security ethics download as a pdf or view online for free. This article provides valuable insights into the various methods that organizations can use to secure their network infrastructure and protect their sensitive information against cyber threats. Guide for security focused configuration management of information systems provides guidelines for organizations responsible for managing and administering the security of federal information systems and associated environments of operation.

Network Security Pdf Security Computer Security This article provides valuable insights into the various methods that organizations can use to secure their network infrastructure and protect their sensitive information against cyber threats. Guide for security focused configuration management of information systems provides guidelines for organizations responsible for managing and administering the security of federal information systems and associated environments of operation. The security architecture planning module takes a close look at paloalto network’s next generation hardware and firewall os product offerings. students also examine various attack strategies including sql injection, cross site scripting and numerous network attacks. Reviewing and coordinating reporting of security advisory alerts (saa), compliance reviews, security and privacy awareness training, incident reports, contingency plan testing, and other it security program elements. This cyber security and it infrastructure protection derivative book serves as a security practitioner’s guide to today’s most crucial issues in cyber security and it infrastructure protection. For security purposes, all applications should be housed and run in a virtual environment.

Computer Security Incident Handling Role Of Management In Effective The security architecture planning module takes a close look at paloalto network’s next generation hardware and firewall os product offerings. students also examine various attack strategies including sql injection, cross site scripting and numerous network attacks. Reviewing and coordinating reporting of security advisory alerts (saa), compliance reviews, security and privacy awareness training, incident reports, contingency plan testing, and other it security program elements. This cyber security and it infrastructure protection derivative book serves as a security practitioner’s guide to today’s most crucial issues in cyber security and it infrastructure protection. For security purposes, all applications should be housed and run in a virtual environment.
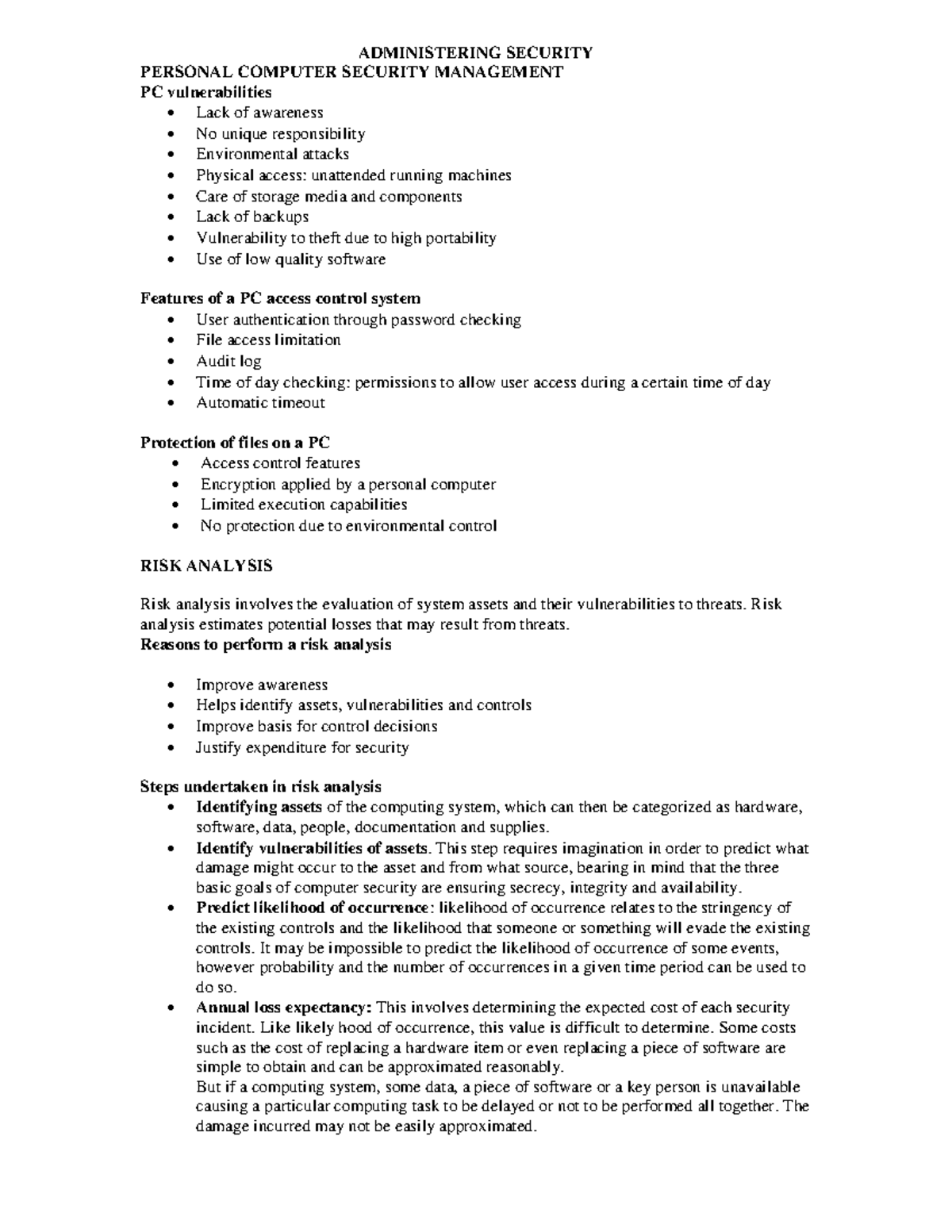
Administering Security Administering Security Personal Computer This cyber security and it infrastructure protection derivative book serves as a security practitioner’s guide to today’s most crucial issues in cyber security and it infrastructure protection. For security purposes, all applications should be housed and run in a virtual environment.
Comments are closed.